October 2024
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover enterprise system and rolling asset security, trending reports, and more.
How Washington is Helping the Trucking Industry Battle Back Against Cargo Theft
Cargo theft has long been a challenge for the trucking industry, but today it’s reaching unprecedented levels. As thefts hit record highs, criminals are using increasingly sophisticated methods, combining stealth with digital tactics to target valuable shipments. Read the article to find out what congress is doing to protect your fleet.
Why Weak Cybersecurity Leaves Your Freight Vulnerable to Cargo Thieves
High-value cargo theft has jeopardized the livelihoods of supply chain businesses for decades. Shippers entrust brokers and carriers with safely moving their shipments from point A to B. All it takes is one costly incident for a transportation business to lose its reputation. Find out what you can do to protect your cargo.
Explore How AI is Transforming the Transportation Industry
NMFTA's AI for Transportation: Benefits, Risks, and Best Practices whitepaper breaks down the key benefits AI offers—such as route optimization, predictive maintenance, and autonomous driving—while also addressing the risks and challenges, including data privacy, legal compliance, and cybersecurity. Download the whitepaper now and gain actionable strategies to navigate the future of AI in transportation.
Your Fleet is at Risk: Download Seed-Key Exchange Guide Now
Modern trucks rely on advanced systems vulnerable to cyberattacks, posing serious risks to fleet operations. Traditional security methods, like the seed-key exchange, are becoming outdated, leaving fleets exposed to potential disruptions. Download NMFTA's latest guide to learn how upgrading to stronger security measures, such as certificate-based authentication, is essential.
Join NMFTA at Manifest 2025
NMFTA will host a session at Manifest 2025 that will discuss key cybersecurity trends from the past decade and offer predictions for the future. Topics include ransomware, nation-state attacks, AI and machine learning in cyber defense and offense, and cloud security. The session will explore emerging threats, regulatory challenges, and new technologies shaping the field, providing attendees with insights to prepare for future cybersecurity challenges.
Use our link below and save $200 on your registration.
Peek into 2025's Supply Chain Cybersecurity Trends
November 14, at 1:00-2:00 pm ET | Online
Join us as we dive into the top cybersecurity trends impacting the supply chain in 2025, from Ransomware as a Service (RaaS) to evolving advanced persistent threat actors (APT) tactics. Our expert panel will cover physical asset threats like vehicle telematics and enterprise cybersecurity, giving you the insights you need to stay ahead. Don’t miss this in-depth discussion—register now!
Explore the Impact of AI in Transportation with the NMFTA Cybersecurity Team
December 5, at 2:00-3:00 pm ET | Online
Join the NMFTA Cyber team for this engaging webinar that will explore the rapidly growing role of AI in the transportation industry. They’ll examine both the significant benefits AI offers and the critical risks it poses, providing a balanced view of its potential impact.
On Demand: Navigating the Impact of Chinese Infrastructure at Ports
As global connectivity continues to expand, so does the complexity and risk of integrating systems and technologies from potential geopolitical rivals. This webinar explored the multifaceted implications of Chinese infrastructure on U.S. logistics, focusing on recent incidents, espionage risks, and the strategic challenges faced by the U.S. and its allies.
Last Chance to Register
October 27-29 | Cleveland, OH
Time is almost up! The 2024 NMFTA Cybersecurity Conference is just days away, and we don’t want you to miss this critical opportunity to bolster your organization’s cyber defenses.
As a leader in the industry, you know the stakes are higher than ever when it comes to cybersecurity. This is your last chance to join fellow c-suite executives, IT leaders, and cybersecurity experts in tackling the most pressing challenges facing the transportation industry.
New Session Added: Fireside Chat: From Dashboard to Data: OEM Insights on Truck Cybersecurity
In This Month's Report...
BianLian Ransomware Targets Global Cargo Alliance (GCA)
On September 11, 2024, analysts identified a communication that the ransomware group BianLian posted on its dark web (DW) leak site in which it claimed to have targeted Global Cargo Alliance (GCA), a Miami, Florida–based international freight and logistics company. BianLian claimed to have acquired one terabyte of data including HR data, financial information, partner and vendor data, internal communications, and other databases. As proof of the hack BianLian posted sensitive documents belonging to GCA on its DW leak site.
Emerging in June 2022, BianLian appears to be financially motivated. The group mainly targets US-based companies and critical infrastructure but has recently begun to attack more international targets, including in Australia and Canada.
In a reference to BianLian’s tactics, techniques, and procedures (TTPs), the group normally gains access to a victim's system through valid Remote Desktop Protocol (RDP) credentials, open-source tools and command-line scripting for discovery and credential harvesting. The group then exfiltrates the victim’s data via File Transfer Protocol (FTP), Rclone, or Mega. Originally, BianLian employed a double-extortion model, but around January 2023, it shifted to primarily exfiltration-based extortion.
Chinese Threat Actor Volt Typhoon Utilizes Versa Zero-Day Exploit to Breach Systems
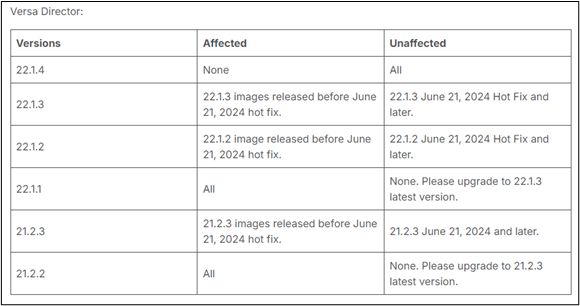
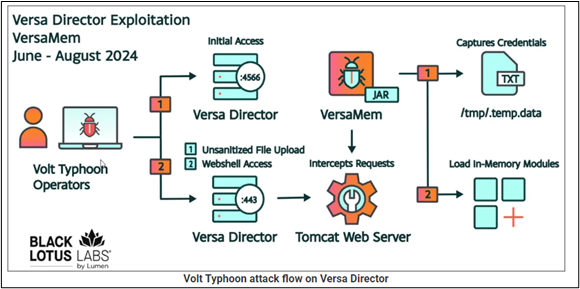
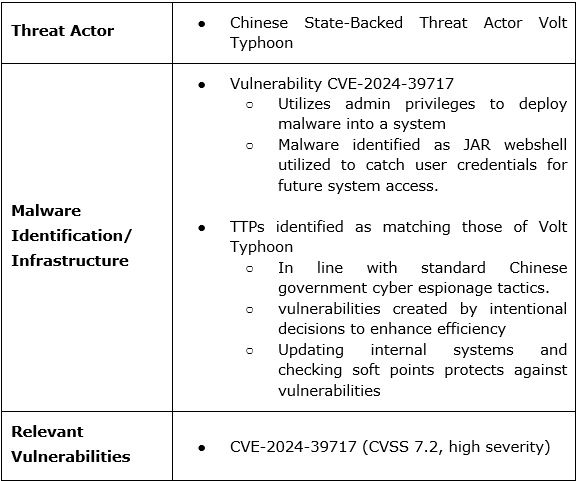
The threat actor group Volt Typhoon has been identified as the likely perpetrator of a series of attacks utilizing a vulnerability tracked as CVE-2024-39717 due to links to the group’s known tactics, techniques and procedures (TTPs). Volt Typhoon is a Chinese state-backed hacking group that is assessed to be mostly politically motivated, engaging in cyber espionage for the Chinese government. Volt Typhoon usually operates by hijacking SOHO routers and VPNs to launch attacks at target companies and organizations. The group uses the compromised routers and devices to feed malicious traffic into legitimate traffic to mask their entry and remain undetected. Volt Typhoons known TTPs were observed in all four verified cases of an attempted exploitation of CVE-2024-39717 before its public identification. The vulnerability exploited in the Volt Typhoon attacks is known as Versa Director Dangerous File Type Upload Vulnerability and was identified on 23 August 2024. It has a severity score of 7.2 out of 10, corresponding to a high-severity vulnerability.
The vulnerability resides in Versa Networks’ management, monitoring and orchestration software, known as Versa Director, in versions 21.2.3, 22.1.2, and 22.1.3. It is a platform used by internet service providers (ISPs) and managed service providers (MSPs) to manage wide-area network (WAN) connections created through software-defined wide area network (SD-WAN) services. CVE-2024-39717 is a flaw in the system that allows admins to upload custom icons within the Versa Director graphical user interface (GUI). The flaw allows threat actors who have gained administrator access in a system to upload malicious Java files hidden as PNG images that can be executed remotely. The vulnerability was specially crafted to affect Versa Director software. Volt Typhoon explored this vulnerability by accessing an exposed high-availability (HA) port to gain initial access. Then the group created an account with admin privileges to plant malicious software, known as a JAR webshell, that is utilized to capture the login credentials of other users. Updating the Versa director to version 22.1.4 fixes the vulnerability.
Typhoon Volt is a well-known threat actor that has a consistent history of developing new attack techniques and exposing new vulnerabilities. Volt Typhoon’s tendency to probe systems for new vulnerabilities is reflective of China's overall strategy for cyber espionage, a field the Chinese government has dedicated increasing resources to over the last two decades. Additionally, the objective of this particular campaign featured credential gathering to access a target's systems legitimately to observe operations and exfiltrate sensitive data without detection. This technique is a favorite among Chinese government-backed threat actors.
The initial access point identified as the exposed HA was later discovered to have been intentionally left unsecured by Versa Networks to enable Versa Director’s high availability features. The company noted that, if properly protected by a firewall, the vulnerability is not an issue. Acknowledging this exposes the necessity of software vendors and partner companies to properly communicate potential vulnerabilities that must be accounted for internally. To mitigate exploitations of CVE-2024-39717 and similar vulnerabilities, updating operating systems regularly and conducting tests of internal systems allows for proactive identification of soft points and mitigation of potential avenues for threat actor entry.
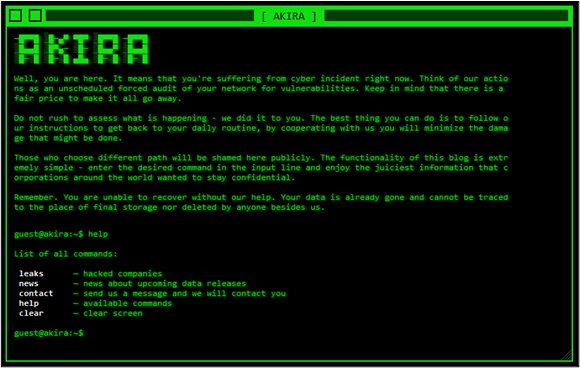
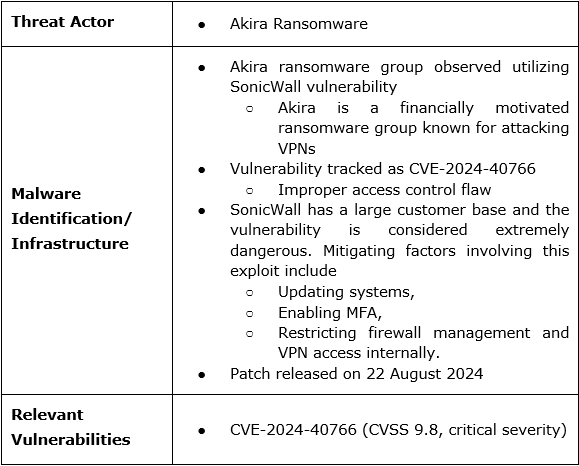
Ransomware Threat Actor Akira Utilizes SonicWall Vulnerability to Infiltrate Target Systems
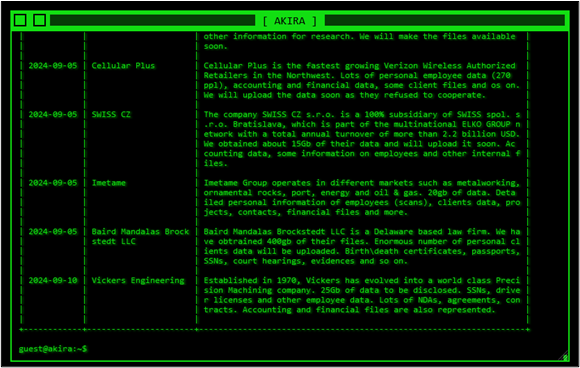
The ransomware group Akira has been observed utilizing a SonicWall Sonic OS firewall vulnerability to gain initial access into systems and execute ransomware attacks. Active since March 2023, Akira appears to be financially motivated. The group's typical tactics, techniques, and procedures (TTPs) involve targeting victims through VPN services, especially in cases involving the lack of multi-factor authentication (MFA). Once it has infiltrated a victim's system, Akira attempts to create new domain accounts to establish persistence and extract data. Like many other ransomware groups, Akira publicly discloses compromised data of its victims on its dark web leak site in cases where the targeted companies do not comply with ransom demands.
The identified vulnerability has been tracked as CVE-2024-40766, which is an improper access control flaw that affects generations 5–7 of SonicWall’s firewalls. The vulnerability was reported patched on 22 August, but it was announced the vulnerability also affects the secure sockets layer VPN (SSLVPN) feature of SonicWall’s firewalls, and that the vulnerability has continued to be exploited for ransomware attacks. The campaign has been linked to Akira due to the observed TTPs utilized in the identified attacks. The use of vulnerabilities involving VPNs and the disabling of MFA were observed in multiple attacks which are in line with Akira’s TTPs.
As of this writing CVE-2024-40766 has been assigned a CVSS score of 9.8, indicating critical severity, and SonicWall has advised all of its customers to update their systems as soon as possible to patch the vulnerability. SonicWall services over 500,000 businesses across 215 different countries, nearly all of which are vulnerable to this exploit. Additionally, ransomware groups other than Akira have been observed utilizing the vulnerability, including HelloKitty and FiveHands. Considering these factors this vulnerability poses a critical threat to business utilizing SonicWall firewall infrastructure as CVE-2024-40766 offers an unimpeded avenue into an internal system and can grant threat actors lateral movement behind a systems defenses. Mitigating factors involving this exploit include updating systems, enabling MFA, and restricting firewall management and VPN access internally.
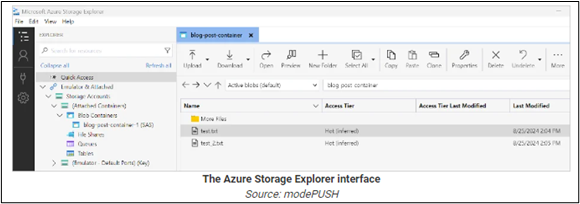
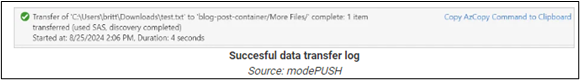
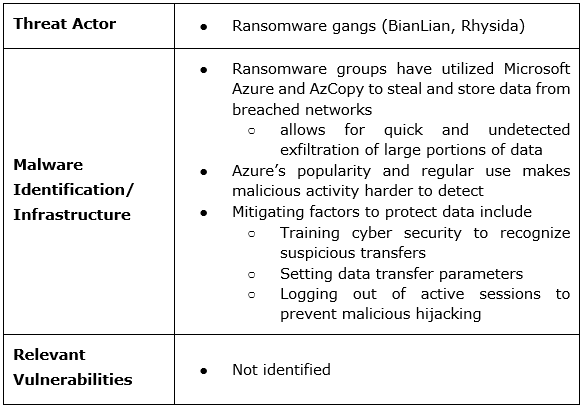
Multiple Ransomware Groups Utilize Microsoft Azure to Exfiltrate and Store Data
Ransomware gangs such as BianLian and Rhysida were observed exploiting Microsoft Azure Storage Explorer and AzCopy to steal and store data from breached networks. Azure is a cloud computing platform developed by Microsoft to build, deploy and manage applications through the Microsoft network. AzCopy is a Microsoft utility used to transfer data to, from, or between accounts. Ransomware groups have utilized these processes to exfiltrate data from compromised networks into their own accounts. This process is only utilized in the data exfiltration portion of a threat actor's attack on a system, meaning that the targeted entity’s system must already be compromised.
Azure is a common target among some ransomware groups due to its popularity and widespread use by commercial entities. This use means that data transfers between Azure accounts may conceal botnet activity and limit the likelihood that internal threat monitoring systems would identify any suspicious behaviors. Azure can also handle large data transfers, which can allow ransomware groups to quickly exfiltrate large amounts of data. Utilizing internal tools developed and offered by a developer, such as Microsoft, during an attack allows ransomware attackers to blend into the systems environment. When executing a ransomware attack and solidifying malware persistence, obfuscation is a key part of the process.
Therefore, repurposing and utilizing internal tools within a target system allows ransomware actors to do more damage with less malware infrastructure that may risk exposing the attack to network security. In these cases, logging out of systems when not in use can limit a threat actor's ability to use internal tools and mitigate the impact of an attack. It may also force ransomware actors to utilize other tools that increase the risk of exposing an attempted cyberattack. Additional mitigating actions include training to recognize suspicious internal system behavior, and setting parameters for file transfers in order to detect abnormal transfers or unsanctioned access.
October 21-24
Detroit, MI
Join NMFTA Cybersecurity Research Engineer, Anne Zachos, at the 8th Annual Auto-ISAC Cybersecurity Summit.
November 5-6
Ocala, FL
NMFTA's Artie Crawford, Joe Ohr, and Ben Wilkens will be speaking during the Florida Trucking Association's Fall Round Up beginning on November 5.
November 8-9
Greenville, SC
NMFTA's Ben Wilkens will be speaking during the South Carolina Trucking Association's Convergence Conference beginning on November 8.
November 11-13
Nashville, TN
NMFTA's Ben Wilkens, will be speaking during the Women in Trucking Association's Accelerate Conference and Expo beginning on November 11.
CISA Kicks Off 21st Anniversary of Cybersecurity Awareness Month
This month, the Cybersecurity and Infrastructure Security Agency (CISA) announced the kickoff of the 21st Cybersecurity Awareness Month. Throughout October, CISA and the National Cybersecurity Alliance (NCA) will focus on ways to “Secure Our World” by educating the public on how to stay safe online. Learn how you can get involved via the link below.
Cybersecurity Considered Afterthought within Manufacturing and Transportation Organizations: Study
More than two in three (69%) manufacturing leaders and nearly three in four (73%) transportation respondents confirmed the opportunity of dynamic computing innovation outweighs the corresponding increase in cybersecurity risk.
Biden Proposes Banning Chinese Vehicles, 'Connected Car' Technology from U.S. Roads
Last month, the U.S. Commerce Department proposed prohibiting key Chinese software and hardware in connected vehicles on American roads due to national security concerns, a move that would effectively bar Chinese cars and trucks from the U.S. market.
The planned regulation, first reported by Reuters, would also force American and other major automakers in years ahead to remove key Chinese software and hardware from vehicles in the United States.
FHWA Adoption of Cybersecurity Evaluation Tool
The Federal Highway Administration (FHWA) announces that it is adopting the Cyber Security Evaluation Tool (CSET) as a voluntary tool transportation authorities can use to assist in identifying, detecting, protecting against, responding to, and recovering from cyber incidents.
Podcast: Cyber Threats and Solutions in the Supply Chain
NMFTA's Joe Ohr chatted with Logistics of Logistics' Joe Lynch last month about the critical role of cybersecurity in the supply chain, transportation, and logistics space. In our digital era, cyber threats like ransomware from organized, state-sponsored groups pose significant risks to global supply chains.
Joe encouraged listeners to attend the trucking industry's only cybersecurity conference this October 27-29 in Cleveland: www.nmftacyber.com.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!










.png)
.png?width=600&height=400&name=CIR%20Images%20(2).png)
.png)
.png)



.png)
