November 2024
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover enterprise system and rolling asset security, trending reports, and more.
Just Released: New Report
The trucking industry is at a pivotal crossroads. As we move into 2025, new cybersecurity threats—from AI-enhanced phishing to cyber-enabled cargo theft—are reshaping the landscape. Download our comprehensive report and explore critical developments you need to understand to stay ahead.
Happening Today: Peek into 2025's Supply Chain Cybersecurity Trends
Today, at 1:00-2:00 pm ET | Online
Join us today, at no charge, as we dive into the top cybersecurity trends impacting the supply chain in 2025, from Ransomware as a Service (RaaS) to evolving advanced persistent threat actors (APT) tactics. Our expert panel will cover physical asset threats like vehicle telematics and enterprise cybersecurity, giving you the insights you need to stay ahead. Don’t miss this in-depth discussion—register now!
Champions Again! NMFTA Signs On Once More For Cybersecurity Awareness Month
Read the article below to see how NMFTA is supporting the National Cybersecurity Alliance's Cybersecurity Awareness Month.
How Washington is Helping the Trucking Industry Battle Back Against Cargo Theft
Cargo theft has long been a challenge for the trucking industry, but today it’s reaching unprecedented levels. As thefts hit record highs, criminals are using increasingly sophisticated methods, combining stealth with digital tactics to target valuable shipments. Read the article to find out what U.S. congress is doing to protect your fleet.
Join NMFTA at Manifest 2025
At Manifest 2025, NMFTA will lead a powerful session diving into the top cybersecurity trends of the past decade and bold predictions for what lies ahead. Attendees will leave with valuable insights on emerging risks, evolving regulations, and cutting-edge technologies, equipping them to tackle the future of cybersecurity head-on.
Use our link below and save $200 on your registration.
NMFTA and Transport Topics Hosts Webinar on AI in Transportation
December 5, at 2:00-3:00 pm ET | Online
Join the NMFTA Cybersecurity team and Transport Topics, at no-charge, for this engaging webinar that will explore the rapidly growing role of AI in the transportation industry. They’ll examine both the significant benefits AI offers and the critical risks it poses, providing a balanced view of its potential impact.
ICYMI: Navigating the Impact of Chinese Infrastructure at Ports
Watch on Demand
As global connectivity continues to expand, so does the complexity and risk of integrating systems and technologies from potential geopolitical rivals. This webinar explored the multifaceted implications of Chinese infrastructure on U.S. logistics, focusing on recent incidents, espionage risks, and the strategic challenges faced by the U.S. and its allies.

Save the Date for #NMFTACyber 2025
October 26-28 | Austin, TX
Missed out on joining us at #NMFTACyber 2024? We're already gearing up for a bigger and better Cybersecurity Conference in next year. Make plans to join us at the NMFTA Cybersecurity Conference, October 26-28, 2025, at the Westin Downtown Austin.
Click below to watch the videos and see the photo album of the 2024 NMFTA Cyber Conference.
In This Month's Report...
Chinese Threat Actor Salt Typhoon Targets United States Internet Service Providers
Multiple unidentified United States–based internet service providers (ISPs) have been targeted by a Chinese-Government linked threat actor tracked as Salt Typhoon. Also known as APT 41, the group's reported aim is to conduct espionage campaigns and utilize United States–based ISPs to launch future attacks. This is in line with the Chinese Government's ongoing espionage efforts in the United States featured in past attacks on United States critical infrastructure. This attempted infiltration of ISPs appears to have been an effort to establish a foothold within the infrastructure and access sensitive data or launch future cyberattacks. Actively monitored since 2012, Salt Typhoon has a history of targeting critical infrastructure in the United States as well as other western nations. In a reference to its tactics, techniques, and Procedures (TTPs) Salt Typhoon frequently utilizes spearfishing techniques as well as identified vulnerabilities to gain initial access to Systems. It has often been observed engaging in supply chain attacks. Some of the group's typical targets include healthcare, tech, media, software, telecoms, cryptocurrency, and education, among others.
ISPs are a strategic target for Chinese state-backed threat actors as they can offer access to multiple sectors, enable greater intelligence gathering advantages and active monitoring of communications, and provide a ready-made launch pad for future cyberattacks on critical infrastructure. These attacks have the capability of causing major economic disruption, beget broad cyberattacks on the population, and interfere with transportation, healthcare, telecommunication, and other sectors of United states infrastructure. Attacks such as these are likely to continue, as the Federal Bureau of Investigations (FBI) sent out an advisory indicating the Chinese Government has plans to further engage in similar espionage efforts. Mitigating factors to protect infrastructure include promptly updating security systems when such updates are available, conducting tests on internal systems to identify soft points, and actively monitoring internal systems for suspicious activity.



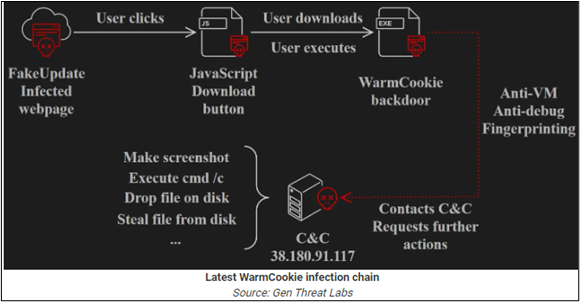
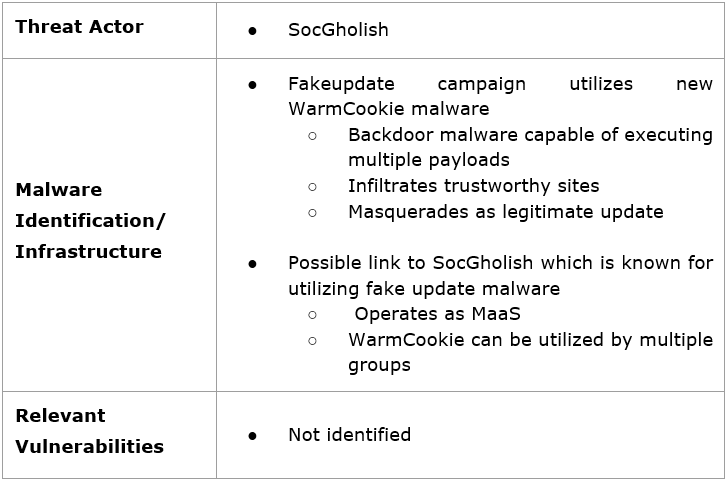
FakeUpdate Campaign Identified Utilizing New WarmCookie Malware
A new FakeUpdate campaign has been identified utilizing an updated version of the WarmCookie backdoor malware. WarmCookie is a backdoor program capable of executing a variety of commands that is typically distributed via phishing attacks and malicious downloads. Some of its capabilities include data and file theft, device profiling, program enumeration (via the Windows Registry), arbitrary command execution (via CMD), screenshot capturing, and the ability to introduce additional payloads on the infected system. In its most recent campaign, some new features identified associated with WarmCookie include the ability to run dynamic-link libraries (DLL) from the temp folder and sending back the output and the ability to transfer and execute EXE and PowerShell files.
In its latest campaign the malware was observed being distributed as fake Google Chrome, FireFox, Microsoft, and Java updates. WarmCookie operates by enticing a user to click on a fake browser update notice, this will then trigger the infection process where the user saves the files and executes the fake update. The malware then runs a check for virtual machines to ensure that the malware is not being run in a sandbox environment and to prevent its code from being captured and countered. The attacker can then execute various payloads in the infected system.
A possible source of the code is the cybercriminal group SocGholish. Active since April 2018, SocGholish, also known as FakeUpdates, is a Russia-linked cybercriminal group with possible associations with Evil Corp. Its fake update malware has been observed in use by multiple threat groups, indicating SocGholish may operate as a malware-as-a-service (MaaS) program. WarmCookie requires both technical skill and a degree of social engineering to execute effectively. Additionally, the malware features anti analysis capabilities and payload versatility. Considering these factors the malware is both dangerous and difficult to identify. The malware's ability to compromise trustworthy applications increases the risk of infection, further exemplifying that extreme caution is a best practice when confronted by pop ups, even on trustworthy sites. Its ability to be distributed via phishing email adds another layer of vulnerability, as a threat actor can target a system through seemingly legitimate internal channels.
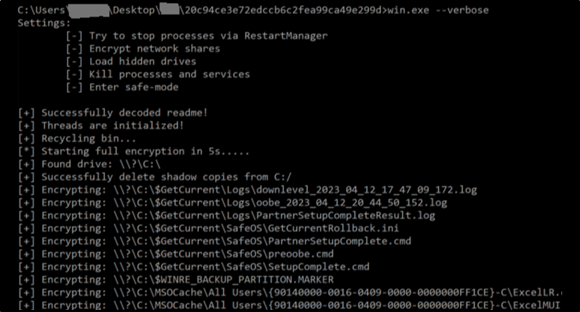
Ransomware Groups Target Veeam RCE Vulnerability in New Cyberattacks
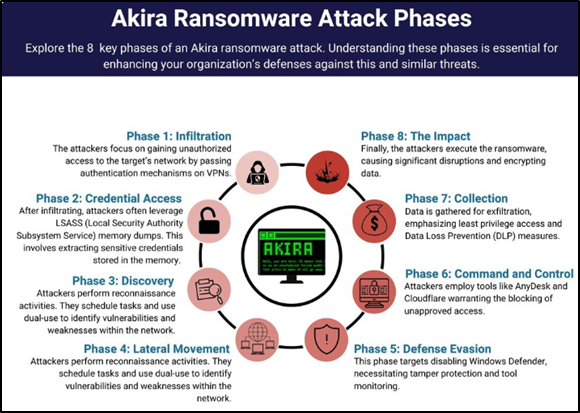
Multiple ransomware groups have been identified targeting a Veeam software company vulnerability tracked as CVE-2024-40711. The vulnerability exists within Veeam’s Backup & Relocation servers and, when exploited, grants an attacker remote code execution (RCE) abilities within a compromised system. CVE-2024-40711 has been rated with a severity of 9.8/10 making it a critical vulnerability that takes little effort to exploit. In the observed cases, the exploitation process begins through virtual private network (VPN) gateways that lack multi-factor authentication. Once inside, the threat actor can simply trigger Veeam’s Backup & Relocation servers and create a local admin account internally to bypass security and deploy ransomware packages. The identified ransomware packages involved in the most recent attacks include Akira and Fog ransomware. Fog is a new ransomware group emerging in April 2024, not much is known about its tactics, techniques, and procedures
Fog is a new ransomware group emerging in April 2024, not much is known about its tactics, techniques, and procedures. The group has been known to purchase credentials from initial access brokers (IABs) to gain entry into a system, and then utilize known vulnerabilities to achieve lateral movement, establish persistence, and steal data. Akira is older and more well established, emerging in March 2023. Akira has targeted companies and organizations specializing mainly in the sectors of finance, real estate and manufacturing. Like many other ransomware groups, Akira publicly discloses compromised data of its victims on its dark web leak site in cases where the targeted companies do not comply with ransom demands. In a reference to its tactics, techniques, and procedures (TTPs) AKIRA ransomware commonly targets victims through VPN services, especially in cases involving the lack of multi-factor authentication (MFA). Once It has infiltrated a victim's system Akira attempts to to create new domain accounts to establish persistence and extract data.
In reference to Akira, the CVE-2024-40711 vulnerability fits in well with the group’s modus operandi. The vulnerability is easy to take advantage of, especially for skilled ransomware groups such as Akira that specialize in VPN exploitation. Additionally, the identified lack of multi-factor authentication presented another vulnerability for Akira to exploit. In reference to Fog, while being relatively new, the group has been observed taking advantage of known vulnerabilities in the past, making this critical vulnerability a viable target for that group as well. The accessibility of CVE-2024-40711 means that a wide range of threat actors with a variety of skill levels are likely to target entities utilizing Veeam’s software until the vulnerability is reliably patched, and no other exploitations are identified.

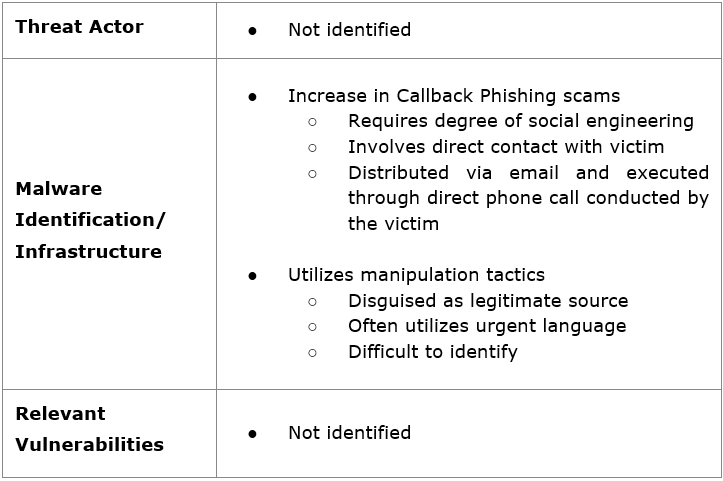
Callback Phishing Attacks Utilize Google Groups to Steal Information
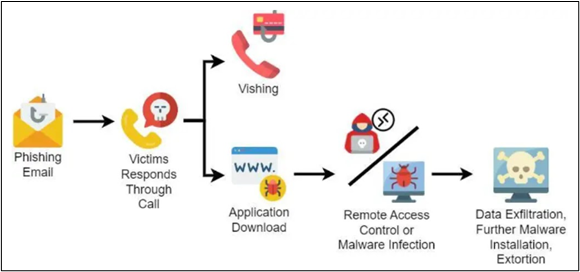
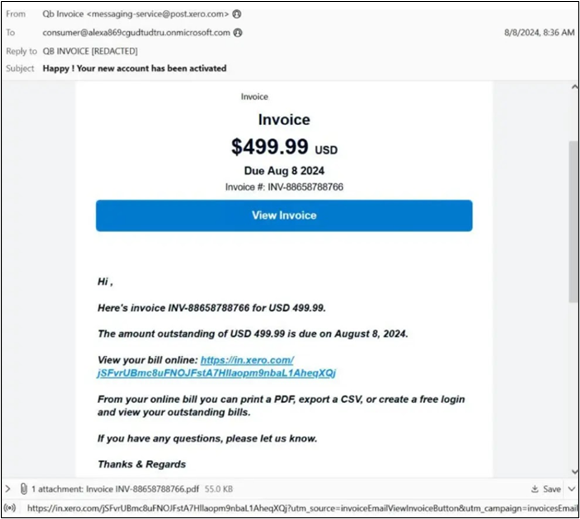
A significant surge in callback phishing attacks has been observed since July 2024, with a 140% increase between July and September alone. The attacks mainly targeted Google Groups from which the attackers were obtaining login information to various accounts. Callback phishing attacks are a hybrid form of standard phishing attacks that include a heightened degree of social engineering and direct interaction. The attacks begin with typical phishing emails that impersonate well-known brands, with some emails containing malware and other malicious code. Where these attacks differ is in the requested interaction of the victim.
In the most recent observed attacks, the phishing emails surround topics such as unpaid invoices or account terminations and prompt the victim to call a number to rectify the issue. The emails include proper headers, authentic business links, and real addresses to appear legitimate. When the call is conducted, the malicious actor can extract sensitive personal information such as bank numbers and Social Security information, gain control over the victim's computer through the victim granting the actor admin access, and deploy malware by convincing the victim to download malicious files. The attackers have also been observed leveraging real authentication protocols such as DomainKeys Identified Mail (DKIM) signatures to gain the victim’s trust. Analysts note these attacks have been mostly observed targeting financial institutions and individuals.
Phishing attacks require a level of social engineering skill in order to develop convincing enough content to entice a victim to click on malicious links. Callback phishing takes this concept to a new extreme by combining technical skill with direct conversations between victims and attackers. Callback phishing leaves a smaller technical footprint in the initial stages of the attack and relies heavily on extracting information directly from the victim, meaning the attacker must be exceptionally convincing. Many of the observed attacks included urgent language such as “overdue payment” or “account error,” causing the victim to approach the situation more distressed and less likely to question the legitimacy of the source. This technique decreases the chances of system detection as the access is granted directly from the victim, bypassing most security features.
Callback phishing’s use of manipulation tactics makes it difficult to detect without proper training on phishing attacks. Encouraging suspicion of unknown emails is a common practice in cyber security, but social engineering and phishing emails can vary in complexity and can foster a false belief that all scams are easily recognizable. Keeping up to date on evolving tactics is beneficial, but the most effective way of protecting sensitive information is by not sharing personal information over the phone to unverified sources, especially if the source was sent directly through email.
November 19-21
Chattanooga, TN
Join NMFTA's Joe Ohr and Keith Peterson at the F3: Future of Freight Festival beginning on November 19.
January 27-29, 2025
Atlanta, GA
NMFTA's Joe Ohr and Keith Peterson will be speaking at SMC3 Jumpstart beginning on January 27.
February 10, 2025
Las Vegas, NV
NMFTA's Artie Crawford, and Joe Ohr will be speaking at Manifest 2025.
Proposed Security Requirements for Restricted Transactions
Stay informed on the latest proposed security requirements for restricted transactions and understand their impact on your organization by reading the article below.
White House Representative Stephen Viña Warns of Rising China Cyber Threat at Sold Out NMFTA Cybersecurity Conference
Read the article below and discover critical insights from White House representative Stephen Viña on the growing cybersecurity threats posed by China, as discussed at the NMFTA Cybersecurity conference.
Ransomware Remains Top Cybersecurity Concern for Trucking Industry
Read the article below and discover why ransomware is the trucking industry’s biggest cybersecurity threat and how businesses can protect themselves.
Threat of Cyberattacks: Trucking's New Nightmare
Cyberattacks are growing in number, with the transportation industry becoming an enticing new victim. Read the article below and see what experts at NMFTA's Cybersecurity Conference had to say.
Engaging with Security Researchers: Embracing a "See Something, Say Something" Culture
In an age where digital systems have an electronic tendril in nearly every aspect of our lives, the role of cybersecurity researchers is more important than ever. These individuals and groups proactively identify weaknesses in software, networks, and hardware, often before malicious actors get a chance to exploit them. Read the article below and find out how the "See Something, Say Something" campaign can help your organization.
Werner's Mahon Details Aggressive Approach to Cybersecurity
Werner Enterprises cybersecurity lead Daragh Mahon detailed his aggressive and innovative approach to cybersecurity during a conference Oct. 29. Click below and find out more about his approach.
Podcast: Cyber Threats and Solutions in the Supply Chain
NMFTA's Joe Ohr chatted with Logistics of Logistics' Joe Lynch last month about the critical role of cybersecurity in the supply chain, transportation, and logistics space. In our digital era, cyber threats like ransomware from organized, state-sponsored groups pose significant risks to global supply chains.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!



.png)




.png)
.png?width=600&height=400&name=CIR%20Images%20(9).png)
.png?width=600&height=400&name=CIR%20Images%20(5).png)

.png?width=2048&name=NMFTA-Logo-200x100%20(1).png)