May 2025
NMFTA Cyber Intelligence Newsletter
We’re witnessing an uptick in digital threats, from AI-powered ransomware to highly coordinated attacks targeting vehicle systems and logistics infrastructure. The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to is arm you with intelligence, tools, and tactics to prepare for the attacks that are already underway. Each month we cover enterprise system and rolling asset security, trending reports, and more.
NMFTA's Cybersecurity Team to Take the Stage
Will you be attending Home Delivery World USA later this month in Nashville? If so, don't miss our cybersecurity session at 12:00 pm CT on May 22 featuring SJKargel Consulting LLC's Susan Kargel, NMFTA's Joe Ohr and Ben Wilkens, moderated by InfraGard's John Hantzis.
Ransomware as a Service: Emerging Threats⚠️
Forget lone hackers in basements. Today’s ransomware is a well-oiled machine, backed by criminal syndicates and offered as a service to anyone with a grudge and a credit card.
Discover how this shadow economy is targeting freight operations—and what you can do.
Get Ready! The NMFTA 2025 Cybersecurity Conference is
5 Months Away📅
October 26-28, 2025 | Austin, TX
Only five months left until the NMFTA 2025 Cybersecurity Conference, a premier event dedicated to exploring the intersection of cybersecurity and the trucking industry. Our cyber team is building an exciting agenda packed with actionable insights, cutting-edge research, and real-world solutions. Stay tuned—full agenda coming soon.
Want first access to registration and speaker updates? Subscribe to NMFTA’s email list and be the first to know.
June 12, 2025 | 1:00-2:00 pm ET
As cargo theft becomes more sophisticated through cyber-enabled tactics, your fleet could be the next target without even knowing it. Join NMFTA’s upcoming webinar, Mitigating the Risk of Cyber-Enabled Cargo Theft, to uncover how these high-tech heists happen—and how to stop them before your freight disappears.
Watch on Demand
The NMFTA cybersecurity team hosted the Securing the Future of Heavy Vehicle Cybersecurity—The CyberTruck Challenge webinar. Discussion in the webinar revolved around the mission of the CyberTruck Challenge and how it prepares students to tackle cybersecurity threats in heavy vehicles.
Roadmap to Resilience: Practical Cyber Defense for Trucking IT Teams
Mid-sized fleets are targets for hackers, and a single attack will result in downtime and lost revenue. Learned tailored defenses for those caught between budget constraints and rising threats.
In This Month's Report...
CISA Warns of New "Fast Flux" Cyber Technique
The United States (U.S.) Cybersecurity and Infrastructure Security Agency (CISA) released an announcement warning of a new and growing technique, identified as “Fast Flux,” that cybercriminals have adopted. The technique allows threat actors to consistently evade detection within a compromised system. When foreign malware infiltrates a system it needs to connect to its command-and-control (C2) server to transmit data or wait for commands. These commands are vulnerable to detection from internal security systems, the more interactions with the C2 server that the malware has, the more likely the malware is to be discovered. The Fast Flux technique decreases the risk of detection by rapidly switching domain name system (DNS) records associated with the C2 connection. Through this technique the malware can more easily evade detection, and even if the system identifies and acts upon a suspicious connection or communication, the malware can utilize other internet protocol (IP) addresses to continue operating.
This technique typically uses a bot net as the technique requires the use of multiple IPs. The technique has been used in malware attacks from groups such as Hive and Nefilim and can be utilized in multiple attack vectors such as phishing, distributed denial-of-service (DDoS), and ransomware. The amount of infrastructure required to conduct this attack means the attacker must have advanced skills or a connection to an established botnet. Utilizing anomaly detection systems that track DNS queries can help identify this form of attack by tracking unknown DNS communications. Consistently reviewing DNS communications can also help identify compromised systems.

Lawmakers Seek Deeper Look into Chinese Cyber Risks
House Republicans have reintroduced a bill aimed at taking a closer look at the growing cyberthreats coming from China, specifically the Chinese cybercampaigns targeting the U.S. critical infrastructure. The bill pushes for an assessment into how Chinese hackers might be targeting different parts of America’s critical infrastructure from power grids to hospitals to banks.
Instead of treating cybersecurity in a general format which looks at it from one perspective, the legislation is seeking to break things down to the specific sectors. That means looking at each critical area, water, energy, healthcare, and transportation in order to figure out where the biggest vulnerabilities are and how they might be exploited by Chinese state-sponsored hackers.
The move comes in response to ongoing concerns about campaigns like Volt Typhoon, where Chinese hackers have been accused of quietly infiltrating critical U.S. networks—possibly preparing for future conflict scenarios or large-scale disruptions.
The bill presents a significant shift toward a precise and coordinated approach of understanding cyberthreats introduced from China. By mandating assessments for individual critical infrastructure sectors, lawmakers aim to go beyond generalized cybersecurity posturing and address the unique risk profiles within each domain. This sector specific strategy acknowledges that vulnerabilities and risks are unique for each sector separately.
Furthermore, an interagency collaboration approach showcases the recognition that no single government entity has full visibility or control over the digital infrastructure and cyber landscape. Bringing together insights from Department of Homeland Security (DHS), CISA, the Department of Defense (DOD), and the intelligence community is essential to develop a more precise national cyber defense.
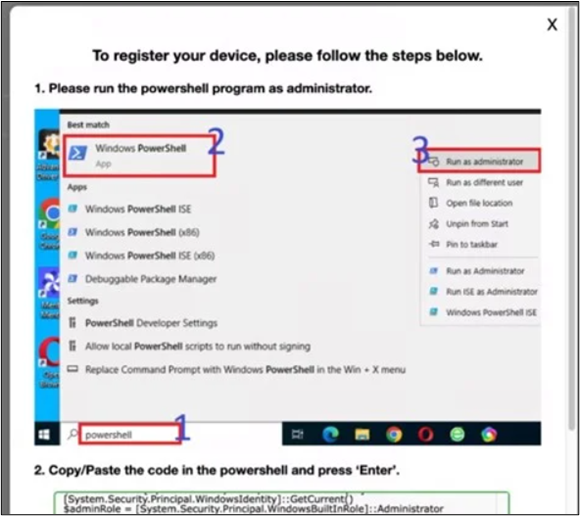
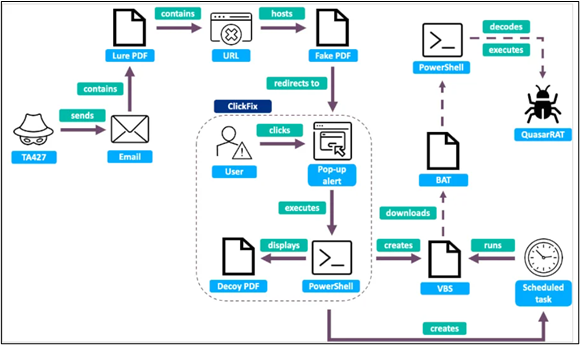
ClickFix Social Engineering Tactic Spreads Among State-Backed Threat Actors
The new ClickFix social engineering tactic, which the North Korean threat group Lazarus had previously adopted, has begun to spread to other North Korean threat actors and to state-backed threat actors in countries such as Russia and Iran. ClickFix is a tactic whereby a malicious website impersonates legitimate software that prompts a victim to click a “fix” button, which downloads malware to a target computer. This form of attack is typically distributed via phishing campaigns. Multiple threat groups such as Muddy Water from Iran, APT28 from Russia, and Kimsuky from North Korea, have begun to utilize the technique in their own targeted operations.
The expansion of this method reflects its success within recent cybercampaigns. Each of the identified groups has utilized this technique in slightly different ways exemplifying its versatility and applicability. Its integration into the tactics, techniques, and procedures (TTPs) of multiple groups indicates it will likely grow in use and sophistication over time. Training to recognize this new form of attack can help in its identification as well as the tracking of its development. Exhibiting health suspicion whenever interacting with a link from an unknown or suspicious email can also mitigate the effects of phishing scams.
2025 Data Breach Investigations Report
The 2025 Verizon Data Breach Investigations Report offers critical insights into the latest attack vectors, including a significant rise in third-party breaches and ransomware incidents. Read the report and stay informed on ways to strengthen your organization's cybersecurity posture
Viasat Modems Zero-Day Vulnerabilities Let Attackers Execute Remote Code
A newly discovered zero-day vulnerability (CVE-2024-6198) in multiple Viasat satellite modem models allows unauthenticated attackers to execute remote code, posing significant threats to critical infrastructure reliant on these devices. Read the article below for insights into the technical details of the exploit and outlined steps to ensure your devices are updated and secure.
FBI Releases Annual Internet Crime Report
The Federal Bureau of Investigation's (FBI) newly released 2024 Internet Crime Report reveals a staggering $16.6 billion in losses from cybercrime—a 33% increase over the previous year—driven by phishing, ransomware, and a surge in cryptocurrency fraud. This report is a must-read for anyone looking to understand the evolving threat landscape and protect themselves or their organization from growing risks.
Many Fuel Tank Monitoring Systems Vulnerable to Disruption
A recent report from Dark Reading reveals that thousands of internet-connected automatic tank gauges (ATGs), essential for monitoring fuel levels and leaks at gas stations and critical facilities, are vulnerable to cyberattacks. Read this article and gain an understanding of the emerging threats to fuel infrastructure and the urgent need for enhanced cybersecurity measures.
OOIDA Promotes Cybersecurity Initiative
In April, the OOIDA Foundation featured the #NMFTA cybersecurity team's recent initiative, the Owner Operator Core Controls Checklist, in its "Trucker Success" newsletter. This checklist provides easy to follow steps you can take to dramatically increase your level of cybersecurity without breaking the bank.

Turn Dials to NMFTA's Recurring Dave Nemo Show
Segment: Freight Focus: Insights from the NMFTA
Upcoming Shows: 9:00 am ET on Wednesday, May 28; Wednesday, June 25; Wednesday, July 23
SiriusXM Channel 146 (Road Dog Trucking)
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!





.png?width=500&height=281&name=CyberWebinar-CyberTruck-Challenge-May-8-1920x1080-1-1920x1080%20(1).png)



