May 2024
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover system and rolling asset security, trending reports, and more.
Free Whitepaper
Securing Legacy Maintenance Software
Don't let outdated software become a security roadblock.
NMFTA, a leader in trucking cybersecurity research, has conducted a comprehensive study on securing legacy fleet management software in the trucking industry, in partnership with Jaime Lightfoot, security researcher and software develop at Lightfoot Labs.
Download the whitepaper to learn:
- Threats to legacy maintenance software
- Legacy fleet maintenance software vulnerabilities
- Practical solutions for securing legacy maintenance systems
- Industry best practices
NMFTA Cyber Experts Featured in Three-Part Series
Inside Lane recently talked with NMFTA's cybersecurity experts for two installments of its three-part series which explores the trucking industry's urgent need to adopt more robust cybersecurity measures.
Part 2: Amid rising cyber threats, the trucking industry strengthens defenses against hackers targeting critical transportation infrastructure, with NMFTA's Joe Ohr and industry experts rallying to secure the nation's supply chain from digital attacks.
Part 3: NMFTA dives into effective cybersecurity strategies for trucking businesses, emphasizing prevention and easy-to-implement tips for protecting against cyber threats.
How to Protect Your Trucking Company from Third-Party Risks
73 percent of organizations say they have heavy dependence on outside service providers. Yet only 54 percent of companies make third party risk management (TPRM) a part of their broader risk management program, and 37 percent say they don’t have TPRM programs at all.
How AI is Revolutionizing Cybersecurity in the Trucking Industry
From manipulating logistics platforms to automating security responses, the impact of artificial intelligence (AI) is undeniable. Red this blog to learn how to leverage AI for good while minimizing its potential dangers.
I Have 1 Minute...
1. Patch for AKIRA and LockBit Ransomware Cyberthreats
Ransomware groups AKIRA and LockBit targeted transportation and logistics companies in Illinois and Montana, respectively. These attacks highlight the vulnerability of this sector to ransomware attacks. It is important to ensure that your systems are patched and up-to-date, and that you have strong backups in place. You should also educate your employees about the dangers of phishing attacks and how to avoid them.
2. Malware Phishing Operation Hits Oil and Gas Sectors with Rhadamanthys Intrusion
A phishing campaign targeting oil and gas companies used a lure from the U.S. Department of Transportation (DOT) to deliver Rhadamanthys information-stealer malware. This campaign highlights the evolving tactics of cybercriminals and the importance of employee awareness training. Employees should be trained to be suspicious of unsolicited emails, even if they appear to come from a legitimate source. They should also be careful about clicking on links or opening attachments in emails.
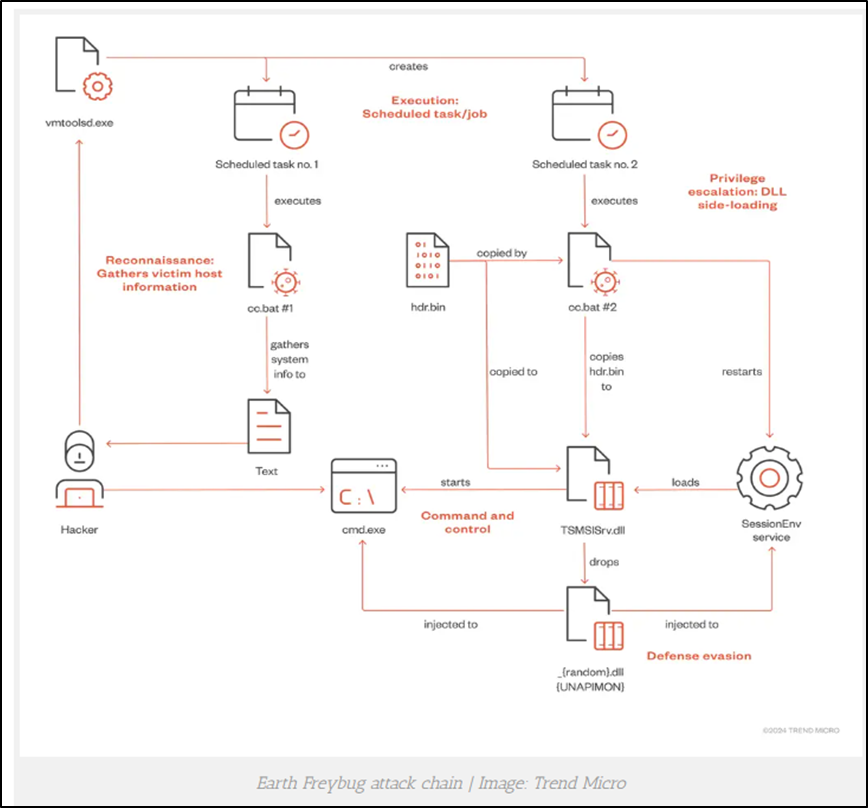
3. Chinese Threat Actor Earth Freybug Uses New Technique to Evade Detection
A China-linked threat actor called Earth Freybug is using a new technique that combines DLL hijacking and API unhooking to evade detection. This technique highlights the increasing sophistication of cyberattacks and the need for robust security defenses. Organizations should keep their systems up-to-date and implement security measures that can detect and prevent these types of attacks.
Read The Full Report...
Krypton Alert: AKIRA Claims Attack on Lotz Trucking in Illinois
On April 16, 2024, analysts identified a communication that was posted by the ransomware group AKIRA in which the group claimed via its dark web leak site to have targeted Lotz Trucking, an Ottawa, Illinois–based transportation and logistics company. AKIRA claimed to have stolen 15 GB of data, including financial information, NDAs, employee documents, and more. The group did not provide a timeframe for the data publication.
Analysts note that AKIRA appears to be a new family of ransomware that was detected in March 2023. Since then, the ransomware group has targeted companies and organizations specializing mainly in the sectors of finance, real estate and manufacturing. Like many other ransomware groups, AKIRA publicly discloses compromised data of its victims on its dark web leak site in cases where the targeted companies do not comply with ransom demands. Analysts further note that AKIRA ransomware commonly targets victims through VPN services, especially in cases involving the lack of multi-factor authentication (MFA).

Krypton Alert: LockBit Ransomware Targets Tri-State Truck & Equipment
On April 20, 2024, analysts identified a communication that the ransomware group LockBit posted on its dark web (DW) leak site in which it claimed to have targeted Tri-State Truck & Equipment, a Montana-based truck manufacturing and repair company. LockBit did not indicate how much or what data it acquired but did state all data was made publicly available on April 19, 2023 via a download link on its DW leak site.
LockBit appears to be a financially motivated group, which emerged in September 2019. The ransomware group targets victims operating in various sectors including transportation, logistics, healthcare, manufacturing and engineering, with most notable previous victims based in the United States, Latin America, Europe, China, India and Indonesia.
In a reference to LockBit’s tactics, techniques, and procedures (TTPs), analysts note that the group usually implements a double-extortion tactic for an additional leverage to collect ransom payments. In order to target networks, the group uses various methods, including unpatched vulnerabilities, insider access, and zero-day exploits. Additionally, the group functions as ransomware-as-a-service (RaaS), which enables LockBit to sell or rent predeveloped ransomware tools to its affiliates to execute ransomware attacks.

Rhadamanthys Info-Stealer Distributed in Campaign Targeting Oil and Gas Sector
Rhadamanthys, a malware-as-a-service (MaaS) operation facilitated through an information-stealer malware, was linked to a series of phishing attacks targeting companies in the oil and gas sector using a lure purportedly from the US Department of Transportation. The campaign began in February 2024 and may still be ongoing, with a unique series of lures relating to vehicle incidents and a range of TTPs that allow the threat actor to successfully deliver phishing emails to targets while evading filters. The email lures involve reports of an alleged vehicle collision, including subjects such as “Urgent: Review Information Approximately Your Car Accident,” “Attention Needed: Your Vehicle's Collision,” and “Incident Implicating Your Car: Insistent Care Required.” The emails contain an embedded link that, when clicked, exploits an open-redirect vulnerability that allows threat actors to redirect web traffic through legitimate domains to alternative locations. The traffic redirection in this
campaign starts from a URL hosted on Google Maps or Google Images, passing through a URL generated by a URL-shortening service, ultimately to a .pdf file hosted on the docptypefinder.info domain, which was determined to have been created and registered on at the start of the phishing campaign. The hosted .pdf purports to come from the “Federal Bureau of Transportation,” later referred to as the US Department of Transportation, and is a clickable image that downloads a .zip archive file onto the victim’s system. This .zip archive contains the malware loader for Rhadamanthys, which after being downloaded and deployed establishes command-and-control (C2) infrastructure and harvests various information, including login credentials and cryptocurrency data.
Rhadamanthys’ campaign notably followed a series of major updates to the info-stealer in mid-January 2024, when Version 0.5.0 was published and deployed in attacks. Updates identified in the malware’s latest release included “additional plugins, stealing capabilities, and evasive tactics,” all of which likely contributed to the relatively quick success in the malware’s campaign launched the following month. The malware itself is offered for relatively higher prices than many similar MaaS operations, ranging from weekly prices of $59 to lifetime prices of $999. The success reported in Rhadamanthys’ recent campaign despite the relatively high cost reiterates the effectiveness of the recent updates the threat actor implemented and further indicates the likelihood of its continued use in campaigns targeting entities in other sectors.




Chinese Threat Actor Uses DLL Hijacking and API Unhooking in New Malware Campaign
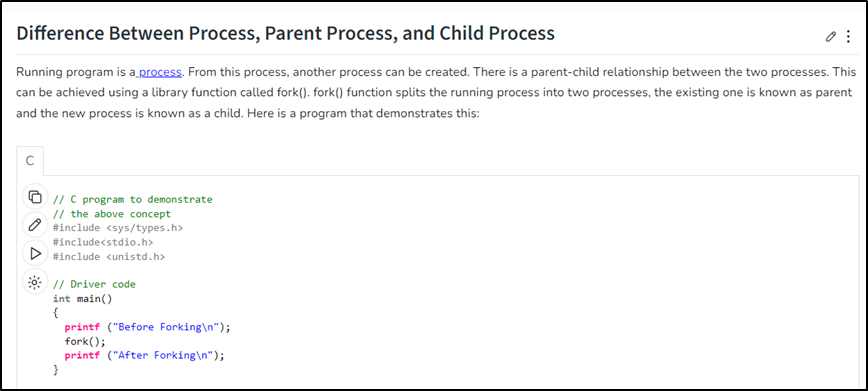
A China-linked threat cluster tracked as “Earth Freybug” has been deploying a unique dynamic-link library (DLL) hijacking and application programming interface (API) unhooking technique. This process is intended to prevent child processes from being monitored via the employment of a malware dubbed UNAPIMON. This malware also assists the threat actor in maintaining persistence and avoiding detection with a compromised network. The Earth Freybug threat cluster employs a combination of living-off-the-land binaries (LOLBins) and custom malware strains in its attacks. The group has also modified additional techniques such as dynamic-link library (DLL) hijacking and application programming interface (API) unhooking. UNAPIMON is a C++-based malware, and is designed to prevent child processes from being monitored by leveraging an open-source Microsoft library called Detours to unhook critical API functions, thereby evading detection in sandbox environments that implement API monitoring through hooking. A child process is a process created by another process. The creator process is called the “parent process.” The benefit of a child process is that it can start or stop at will without affecting the parent process. The child process, however, is typically dependent on the parent process. If the parent process dies, the child process becomes an orphan process.
Earth Freybug is an established threat actor that has been conducting operations since 2012. The threat actor is primarily known for espionage and financially motivated campaigns targeting entities in various industry verticals. The Earth Freybug group is assessed to be a subset of another threat actor known as APT41 (AKA Winnti), which is a prominent China state-sponsored cyber espionage advanced persistent threat (APT) group. APT41 has conducted multiple software supply chain compromises, and specializes in gaining access to software companies to inject malicious code into legitimate files before distributing updates. The APT41 group has targeted a broad spectrum of organizations, including governments, hardware vendors, software developers, think tanks, telecommunication service providers, and educational institutes. APT41 is unique among China-based actors in that it leverages non-public malware that is commonly used in cyber espionage operations in what may be activity that falls outside the scope of state-sponsored missions. Use of this malware is assessed as a tactic, technique, and procedure (TTP) to avoid any attribution to China. Because of their operational nexus, Earth Freybug and APT41 share overlapping TTPs. Earth Freybug’s use of UNAPIMON and its sophisticated anti-monitoring capabilities pose a significant threat to organizations. Use of this malware allows the threat actor to evade detection and maintain persistence. These capabilities significantly enhance the potential for data hijacking, exfiltration, lateral movement within a compromised environment, and activity logging.
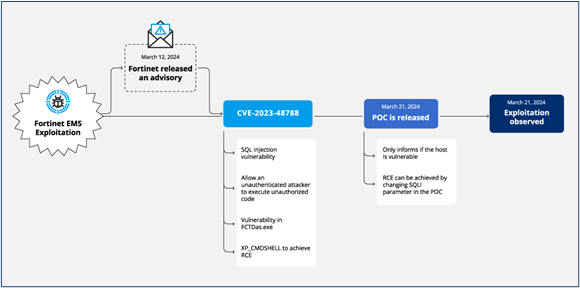
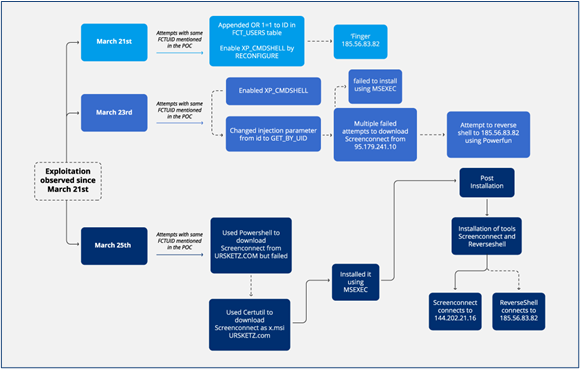
Connect:fun Campaign Targets Fortinet Exploit to Deploy Multiple Malware Families
A group of threat actors operating as part of a collective dubbed Connect:fun were found to be exploiting a critical-severity vulnerability in Fortinet’s FortiClient enterprise management service (EMS) devices in order to deploy three separate malware families on compromised networks. The relevant vulnerability, a SQL injection exploit tracked as CVE-2023-48788, allows a threat actor to execute commands and malicious scripts on compromised devices. Multiple attack chains have been identified as part of this campaign, and the earliest began with the threat actor scanning for vulnerable Fortinet devices on which to exploit the vulnerability, and then downloading the remote desktop software known as ScreenConnect and installing it on compromised devices using the msiexec.exe command. In later attacks, the Powerfun script, which allows threat actors to manipulate shells and execute commands via command-and-control (C2) infrastructure.
The vulnerability was first identified on March 12, 2024 in an advisory from Fortinet, which subsequently published a proof-of-concept (PoC) exploit on GitHub on March 21, 2024. Shortly thereafter, the threat actors behind the Connect:fun campaign began exploited the vulnerability in cyber attacks in what is assessed to be a targeted campaign rather than a blanket, automatic adoption by a botnet or similar operation. The speed with which the threat actor swiftly began to exploit the vulnerability and integrate it into its malware arsenal demonstrates the imperative of installing patches as soon as software developers make them available. The use of ScreenConnect is also notable given the manner in which threat actors have used legitimate remote management and monitoring (RMM) software as a way to maintain control over compromised networks while avoiding detection by anti-malware programs.
Recommendations to Keep Your Company Safe from Cyberattacks
Implement strong security measures. This includes using firewalls, antivirus software, and data encryption to protect your systems from unauthorized access. You should also regularly update your software and patch vulnerabilities.

Get In First: Register Now for the NMFTA Cybersecurity Conference
October 27-29 | Cleveland, OH
We're excited to announce registrations are officially open for the 2024 NFMTA Cybersecurity Conference. This event is the only cybersecurity event of its kind in the world. The annual conference aims to gather the greatest minds in trucking and cybersecurity to explore insights, research, innovations and best practices to protect against trucking cybercrime. With cyber criminals targeting the transportation industry, you literally cannot afford to miss this event.
See how we plan to help bolster your company's cyber resilience via the link below.
NMFTA On The Road
June 3-5
National Harbor, MD
Join NMFTA's Enterprise and Heavy Vehicle Cybersecurity Team at Gartner's Security & Risk Management Summit. They look forward to meeting everyone in attendance.
June 5-6
Plymouth, MI
Join Ben Gardiner, senior cybersecurity research engineer at NMFTA, at escar USA for his exclusive presentation. His talk is currently embargoed, but we can guarantee if you are interested in trucking cybersecurity research, you won't want to miss his presentation.
June 24-28
Warren, MI
NMFTA is excited to be a lead sponsor of the 2024 CyberTruck Challenge. This challenge is a premier event to bring together a community of interest related to heavy vehicle cybersecurity issues and develop talent to address those challenges.
Industry News
Trucking's Two Biggest Cybersecurity Threats Today
Successful cyberattacks present an existential threat to fleets of any size—however, there are best practices to reduce the risk of a successful attack.
How Carriers Can Avoid Cybersecurity Danger from Outside Vendors
A carrier can do all the right things, but if a key vendor fails to be vigilant about its own cybersecurity, the carrier can still fall victim to a breach that jeopardizes everything from its data to its financial security and its reputation.
House Transportation Committee Reviews AI Applications
“AI can only generate widespread and equitable mobility improvements if the right data and assumptions underpin the system. Large, transportation-specific data sets will need to be built, and AI algorithms will need to be trained to be free from bias.”
Preparing for the Costs of Supply Chain Disruptions
For businesses and their supply chain superheroes, these disruptions are having widespread impact. Impact that’s proving detrimental to teams, operations and our economy.
Freight Cybersecurity
News On Demand
Explore nmfta.org/cybersecurity for the most current insights on cybersecurity research, breaking news, updates, and alerts from NMFTA and the Cybersecurity and Infrastructure Security Agency (CISA).
New Interview with Marli Hall, Director of Public Relations: Prioritizing Trucking Cybersecurity—Before It's Too Late. Watch it now.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!



.png?width=380&height=320&name=ai%20and%20trucking%20(1).png)




