March 2025
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover enterprise system and rolling asset security, trending reports, and more.
Road to Resilience: Free Cybersecurity Resources for Trucking
Mid-sized fleets are prime targets for hackers, and a single attack could mean major downtime, lost revenue, and a serious headache. Our newly released Cybersecurity Best Practices Guidebook – Mid-Sized Fleet provide straightforward resources built specifically for mid-sized fleets.
Make cybersecurity a top priority with the Cybersecurity Controls Checklist from NMFTA. A practical, step-by-step guide to securing your business against cyberattacks.
Our Cybersecurity Best Practices Guidebook, packed with budget-friendly solutions, step-by-step tips, and real-world examples, is tailored specifically for small fleets and owner operators. Download the guidebook today and take control of your cybersecurity!
March 13, 2025 | 1:00 - 2:00 PM ET
Today, NMFTA will host the third installment in the roadmap to resilience series, targeted at mid-sized fleets (50 – 3,000 power units). This webinar will provide more advanced guidance and begin to incorporate technical controls and governance practices.
Watch on Demand
Rewatch the NMFTA webinar tailored specifically for owner operators. This webinar discussed insights from the Cybersecurity Best Practices Guidebook. Learn tips and strategies to safeguard your business and protect your data.
Watch on Demand
Protect yourself and your operation from cyberthreats. Watch a discussion on the core cybersecurity best practices that an owner operator or small fleet can implement to significantly boost cyber-resilience without breaking the bank.
NMFTA Announces A Newly-Discovered Vulnerability in Trailer Equipment and Releases Critical Advisory
New Press Release
A newly-discovered vulnerability in trailer equipment poses significant security risks to the trucking industry, potentially exposing fleets to cyberthreats. This NMFTA advisory provides crucial details on the issue and offers actionable steps for mitigation, making it essential reading for every trucking industry professional.
Save the Date for 2025 #NMFTACyber
October 26-28, 2025 | Austin, TX
We are seven months away from the 2025 NMFTA Cybersecurity Conference. Make plans to join us on October 26-28, 2025, at the Westin Downtown Austin. Join our email list and be the first to hear when registration opens.
In This Month's Report...
New Side-Channel Vulnerabilities Identified Affecting Apple Infrastructure
Two new side-channel vulnerabilities have been identified affecting Apple infrastructure wherein sensitive information can be stolen from web browsers. Both flaws stem from flaws in speculative execution implementation, when a computer performs tasks before it is known to be needed in order to avoid delays. The two vulnerabilities are known as False Load Output Predictions (FLOP) and Speculation Load Address Prediction (SLAP) attacks, which aim to speed up processing which causes a system to make mistakes in speculative execution thus leaving gaps of information the attacker can exploit. The attacks are executed remotely through web browsers using malicious code hidden in webpages.
Both of these forms of attacks utilize operations designed to decrease delays to extract information. Effectively, the attacker can grab bits and pieces of information by forcing a speculative execution implementation to guess wrong and run a process unnecessary to the function that is actually required, allowing the attacker to view that function and steal data. Through repeating these processes an attacker can build a portfolio of information that can be usable in other forms of attacks such as password spraying or phishing attacks. Additionally, these attacks can be executed remotely, granting the attacker anonymity and security.
This form of attack does not require a malware infection of a targeted system, making it versatile and less technical. Avoiding malicious webpages and monitoring internal traffic can prevent data leakages associated with this technique. Ensuring that all systems are fully updated can also make the vulnerability harder to exploit. Apple has indicated that it is working on a security update to path the issues.


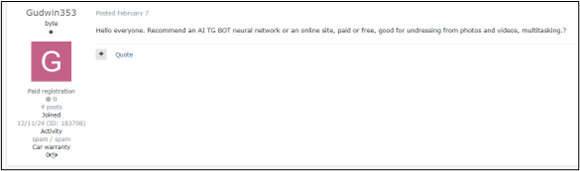
Growing Threat of Cybercriminals Utilizing AI for Fraud
Artificial Intelligence (AI) has grown into the mainstream. Threat actors have attempted to exploit it for criminal activity. AI offers new opportunities for threat actors to more easily manipulate people through social engineering with a multitude of fraud schemes. For example, analysts identified a post on the Russian hacking forum Exploit in which a user asked for recommendations of AI bots with the capability of undressing a person in a photograph. This indicates the user may engage in sextortion scams wherein the threat actor claims to have sensitive media involving a victim to extort money from the victim. Another incident occurred in Italy where scammers utilized an AI voice cloning tool to imitate the Italian defense minister's voice in an effort to extort money in a fake ransom scheme.
The use of AI to fabricate photos and videos is particularly dangerous. Recent reports indicate that a threat actor fabricated videos through AI wherein an Israel Defense Forces (IDF) spokesperson thanked Egypt for its cooperation in the recent Gaza Strip conflict. Protests over the claims of cooperation occurred in Egypt, and Israel has denied the legitimacy of these videos. Israel contests that the videos were developed in an effort to sabotage relations between Egypt and Israel to destabilize the area.
These forms of attacks are growing more frequently as AI grows in popularity. It is sometimes difficult to discern reality from fraud given AI’s rapid progression and improvements. Threat actors can utilize AI to execute social engineering attacks more frequently and with far less skill. AI will only continue to improve and AI fraud campaigns will only become more sophisticated. Confirming the legitimacy of any cyber interaction or media can mitigate the possibility of falling victim to AI fraud.

Russian Threat Actors Launch Phishing Campaign Targeting Signal Messaging App
Multiple Russian state-backed threat actors have utilized the “Linked Devices” feature provided by the Signal messaging app to conduct a device-linking phishing campaign. The campaign exploits this legitimate feature by creating fraudulent quick response (QR) codes and sending link requests or developing phishing pages to deceive potential victims into granting the threat actors access to the system. The Russian threat actor UNC4221 has specifically developed a malware kit designed to target signal groups utilized by military personnel in the ongoing Russo-Ukrainian war. Once access is granted to the threat actor, they can monitor all communications conducted through the signal account.
This form of unauthorized access has vast implications both for military personnel, as it has been observed, and private companies that conduct business through the app or utilize it for sensitive internal private communications. This form of attack does not require a device to be fully compromised as it only requires access to a viewable account. There is no technical solution for monitoring the threat of newly-linked devices to a signal network meaning the access can go unnoticed for a long period of time. Consistently reviewing connected devices on a Signal network can aid in identifying unauthorized access.
The Risks of Connected Systems in Trucking and the Greater Supply Chain
As trucking and supply chain operations become more connected, they also become more vulnerable to cyberattacks that can disrupt entire networks. Discover in this month's NMFTA CCJ article the growing risks of connected systems in transportation and why understanding them is critical
Guidance Strategies to Protect Network Edge Devices
Network edge devices are prime targets for cyberthreats, making their protection essential for maintaining a secure infrastructure. Read the article below and get actionable strategies to safeguard these critical entry points.
Chinese Advanced Persistent Threat Uses VPN Bug to Exploit Worldwide OT Orgs
A sophisticated Chinese APT group is exploiting a virtual private network (VPN) vulnerability to target operational technology (OT) organizations worldwide, posing a severe threat to critical infrastructure. Read the article below and discover the tactics behind these attacks and why OT security teams must act swiftly to mitigate the risks.
Infrastructure Laundering: Silent Push Exposes Cloudy Behavior Around FUNNULL CDN Renting IPs from Big Tech
Cybercriminals are using infrastructure laundering to mask their malicious activities, making traditional security measures less effective. Read the article below which uncovers how attackers exploit digital infrastructure to evade detection.
Doors Wide Open: Hundreds of Thousands of Employees Exposed; Thousands of Organizations Physically Vulnerable
Automated Messaging Systems (AMS) are leaving businesses vulnerable to critical security risks, exposing sensitive data to potential cyberthreats. Read the article below for a breakdown of these hidden dangers and learn how to protect your organization.
26 New Threat Groups Spotted in 2024: CrowdStrike
Cyberthreats are evolving rapidly, with 26 new threat groups identified in 2024 alone, highlighting the increasing sophistication of cyberattacks. Read the article below and learn crucial insights from CrowdStrike on emerging cybercriminal tactics.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!






.jpeg?width=600&height=400&name=010925-RoadmapToResilience-600x400%20(1).jpeg)







