June 2025
NMFTA Cyber Intelligence Newsletter
We’re witnessing an uptick in digital threats, from AI-powered ransomware to highly-coordinated attacks targeting vehicle systems and logistics infrastructure. The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to is arm you with intelligence, tools, and tactics to prepare for the attacks that are already underway. Each month we cover enterprise system and rolling asset security, trending reports, and more.
CyberTruck Challenge: Securing the Future of Heavy Vehicle Cybersecurity🚛
Last week, the NMFTA staff attended the CyberTruck Challenge: an annual event that is shaping the future of heavy vehicle cybersecurity by preparing the next generation of defenders. NMFTA is the premier sponsor of the event. Read how this unique gathering fosters real-world skills, collaboration, and innovation to stay ahead of evolving cyber threats in the transportation sector.
Cargo theft has become one of the most urgent operational threats in trucking, and it’s no longer confined to cut padlocks or missing trailers. For fleet leaders, the risk is no longer theoretical. Download NMFTA's new Cybersecurity Cargo Crime Reduction Framework to learn what you can do to protect your assets.
Roadmap to Resilience: Practical Cyber Defense for Trucking IT Teams
Watch on Demand
As cargo theft becomes more sophisticated through cyber-enabled tactics, your fleet could be the next target without even knowing it. Rewatch NMFTA’s webinar, Mitigating the Risk of Cyber-Enabled Cargo Theft, to uncover how these high-tech heists happen—and how to stop them before your freight disappears.
Watch on Demand
The NMFTA cybersecurity team hosted the Securing the Future of Heavy Vehicle Cybersecurity—The CyberTruck Challenge webinar. Discussion in the webinar revolved around the mission of the CyberTruck Challenge and how it prepares students to tackle cybersecurity threats in heavy vehicles.
Don't Miss the Trucking Industry's Only Cybersecurity Conference
October 26-28, 2025 | Austin, TX
Registration is now open for the 2025 NMFTA Cybersecurity Conference—your chance to connect with industry leaders, cybersecurity experts, and transportation professionals tackling today’s most urgent threats. Don’t wait, secure your spot now and be part of the movement to strengthen the digital defenses of freight and supply chain operations.
Ransomware as a Service: Emerging Threats⚠️
Forget lone hackers in basements. Today’s ransomware is a well-oiled machine, backed by criminal syndicates and offered as a service to anyone with a grudge and a credit card.
Discover how this shadow economy is targeting freight operations—and what you can do.
In This Month's Report...
Multiple PyPI Packages Found Using Gmail SMTP Servers to Exfiltrate Data
Seven malicious Python Package Index (PyPI) packages have been identified using Gmail’s Simple Mail Transfer Protocol (SMTP) servers to exfiltrate data and establish remote command connections. Some of the identified packages are several years old and one has been downloaded over 18,000 times. The identified malicious downloads include:
- Coffin-Codes-Pro (9,000 downloads)
- Coffin-Codes-NET2 (6,200 downloads)
- Coffin-Codes-NET (6,100 downloads)
- Coffin-Codes-2022 (18,100 downloads)
- Coffin2022 (6,500 downloads)
- Coffin-Grave (6,500 downloads)
- cfc-bsb (2,900 downloads)
The packages labeled “Coffin” impersonate legitimate coffin packages that are commonly used for adapting and integrating certain functions. The packages include hardcoded Gmail credentials that log into Gmail’s SMTP server allowing the threat actor to remotely access the system.
The malware’s age and number of downloads indicates the developer is well versed in social engineering techniques and that the malware may be widespread and include obfuscation techniques to avoid detection. The purpose of the malware remains unclear, but there are some indications it may be directed at cryptocurrency theft. The malware’s producer is also unknown at this time. These forms of threats are often disguised as legitimate in order to trick victims into downloading malware. When downloading packages off of the internet it is critical to verify their legitimacy in order to prevent compromises within internal systems.
The Reshaping of Cybercrime through Automation and Deception
In May 2025, cybersecurity authorities in the United States (U.S.) and the United Kingdom (UK) announced developments in the ongoing fight against cybercrime. The Federal Bureau of Investigation (FBI) revealed updates in the takedown of LabHost, a phishing as a service (PhaaS) platform that had operated from 2021 until April 2024. LabHost provided cybercriminals with pre-designed phishing kits, credential harvesting tools, and dashboards to manage stolen data making it easy for low-skill attackers to launch professional campaigns. Over 42,000 domains were used to mimic more than 200 legitimate organizations, including banks and government entities. The FBI disclosed that LabHost stored more than one million sets of stolen credentials and nearly 500,000 compromised credit card numbers.
Meanwhile, the UK’s National Cyber Security Centre (NCSC) issued a public warning following a rise in impersonation attacks targeting major retailers. These attacks involved threat actors posing as information technology (IT) help desk staff and persuading employees to reset passwords or provide system access. Unlike traditional malware-based intrusions, these attacks relied on social engineering techniques. Due to ongoing events the NCSC urged organizations to increase internal authentication procedures, enforce multi-factor authentication, and raise employee awareness about the risks of impersonation and internal fraud.
These two incidents illustrate a broader shift in the nature of cyberthreats, where automation and human manipulation are intertwined. LabHost industrialized phishing by turning it into a scalable service, effectively outsourcing trust exploitation to anyone willing to pay. At the same time, the UK impersonation attacks show that attackers can still succeed without writing a line of malicious code simply by imitating internal staff and leveraging social behavior. Together, these threats demonstrate that modern cybersecurity must extend beyond hardware and tools. It requires an approach that integrates technical defenses with proactive human awareness.
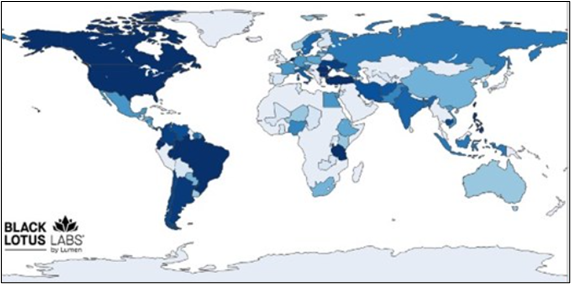
Newly-Identified Botnet Infects Thousands of Devices in North America
A new botnet has been identified which has infected thousands of Internet of Things (IoT) and end-of-life (EoL) devices across North America, incorporating them into the expanding proxy network. A botnet is a group of connected devices infected by malware that operate collectively to conduct criminal cyber activity. The identified botnet targets IoT and EoL devices that are no longer supported through updates, meaning there are likely vulnerabilities that can be exploited within the devices to gain initial access. The area with the highest concentration of targeted devices is North America with the U.S. being the country with the most compromised devices. Analysts note the botment has been identified in over 80 counties so far. The origin of the botnet may be Turkey as multiple servers have been identified in the country that support the botnet’s function.
It is unclear who is responsible for the botnet’s development. It may have been created to be a proxy-for-rent service where threat actors could rent the botnet to conduct their own attacks. This would provide the threat actor with anonymity. Multiple kinds of attacks have been conducted through the botnet including ad fraud, distributed denial-of-service, credential stuffing, and data exploitation. Law enforcement has disrupted the botnet, but it is unclear if any other servers can reestablish it. Ensuring all older devices that are unsupported by updates are disconnected from critical networks can protect internal systems from old and unpatched vulnerabilities.
Emulating the Unyielding Scattered Spider
Get an inside look at how security teams can emulate the tactics of Scattered Spider—one of today’s most elusive and damaging cyberthreat groups. Read the article below and get actionable insights and threat emulation strategies to help organizations prepare for sophisticated, real-world attacks.
OneDrive File Picker Flaw Provides ChatGPT and Other Web Apps Full Read Access to Users' Entire OneDrive
A newly-discovered vulnerability in Microsoft OneDrive’s file picker could expose organizations to serious security risks. Read the article from Oasis Security and learn how the flaw works and what steps your team can take to defend against potential exploitation.
Update to How CISA Shares Cyber-Related Alerts and Notifications
The Cybersecurity & Infrastructure Security Agency (CISA) has updated how it shares cyber-related alerts and notifications, aiming to streamline communication and enhance threat awareness across industries. Read this article to stay informed on the latest changes and ensure your organization doesn’t miss critical security updates.
Billions Lost, Freight Exposed: The Real Cyber & Cargo Threats
Cargo theft and cybersecurity breaches are no longer isolated incidents—they’re a growing epidemic in freight.
Rewatch this high-stakes episode of Driving Forward with guest experts James "Artie" Crawford and Benjamin Wilkens from the NMFTA.
Hosted by GLCS's Robert Bain (Strongest Man in Logistics), this episode pulls back the curtain on the evolving threats facing trucking companies and freight brokers.
Digital Defense | Joe Ohr & Artie Crawford of the NMFTA
On the latest episode of the Semi-Related Podcast, NMFTA Chief Operating Officer Joe Ohr and Director of Cybersecurity Artie Crawford join host Jacob Eischen to discuss how dark-web ransomware rentals, AI-forged emails, and hacked telematics give thieves a back-door pass to your freight and how fleets can prepare a road-ready defense plan. They also preview the NMFTA’s Cybersecurity Conference this October and the no-cost tools rolling out to help carriers of every size stay a step ahead of the next breach.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!




.png?width=500&height=281&name=CyberWebinar-CyberTruck-Challenge-May-8-1920x1080-1-1920x1080%20(1).png)




