July 2025
NMFTA Cyber Intelligence Newsletter
We’re witnessing an uptick in digital threats, from AI-powered ransomware to highly-coordinated attacks targeting vehicle systems and logistics infrastructure. The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed this monthly e-newsletter to arm you with intelligence, tools, and defense tactics. Each month we cover enterprise system and rolling asset security, trending reports, and more.
Why Fleets Can't Afford to Miss the
NMFTA 2025 Cybersecurity Conference🚛
Cyberthreats are rapidly evolving—and fleets can’t afford to fall behind. Read why this year's Cybersecurity Conference is a must-attend event for anyone serious about protecting their operations and staying ahead of attackers.
🚨 Less Than 20% of Stolen Cargo Is Ever Recovered—FBI Data Reveals Shocking Loss Rates
This stark statistic highlights the urgent need for proactive cargo security measures and stronger industry-wide defenses. Download NMFTA’s new Cybersecurity Cargo Crime Reduction Framework to take immediate action and safeguard your assets.
Source: Federal Bureau of Investigation, “Cargo Theft”– https://www.fbi.gov/investigate/transnational-organized-crime/cargo-theft
July 17, 2025 | 1:00-2:00 pm ET
This month, join NMFTA’s upcoming webinar, Panel Insights: NMFTA Cargo Crime Prevention Framework, set for July 17 at 1:00 pm ET. The NMFTA cybersecurity team and other cybersecurity experts will take a deep dive into real-world cargo theft trends, prevention strategies, and how to put NMFTA’s new framework into action.
Watch on Demand
As cargo theft becomes more sophisticated through cyber-enabled tactics, your fleet could be the next target without even knowing it. Rewatch NMFTA’s webinar, Mitigating the Risk of Cyber-Enabled Cargo Theft, to uncover how these high-tech heists happen—and how to stop them before your freight disappears.
Your Spot at the NMFTA 2025 Cybersecurity Conference is Waiting for You
October 26-28, 2025 | Austin, TX
Registration is now open for the 2025 NMFTA Cybersecurity Conference—where fleet leaders, cybersecurity professionals, and trucking industry experts unite to confront the most pressing digital threats facing transportation today. Act fast, this event will sellout. Be part of the only event dedicated to protecting the future of freight.
NMFTA Cybersecurity Team to Speak at DEF CON 33
Ben Gardiner, senior cybersecurity research engineer for NMFTA, will be addressing DEF CON 33 attendees on August 9 . His presentation, Blind Trailer Shouting, has been accepted. DEF CON is one of the world’s largest and most influential hacker and cybersecurity conferences, held annually in Las Vegas.
Learn How NMFTA is Securing the Future of Heavy Vehicle Cybersecurity🚛
Last month, NMFTA staff attended the CyberTruck Challenge: an annual event that is shaping the future of heavy vehicle cybersecurity by preparing the next generation of defenders. NMFTA is the premier sponsor of the event. Read how this unique gathering fosters real-world skills, collaboration, and innovation to stay ahead of evolving cyber threats in the transportation sector.
In This Month's Report...
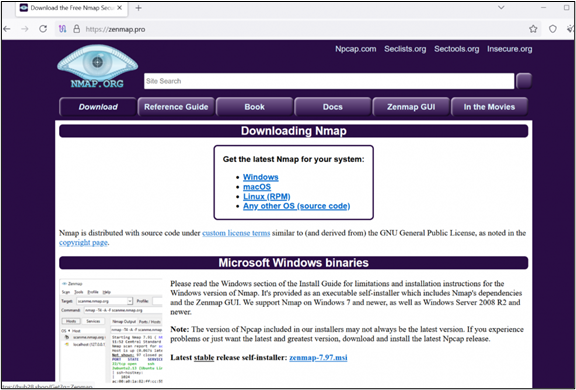
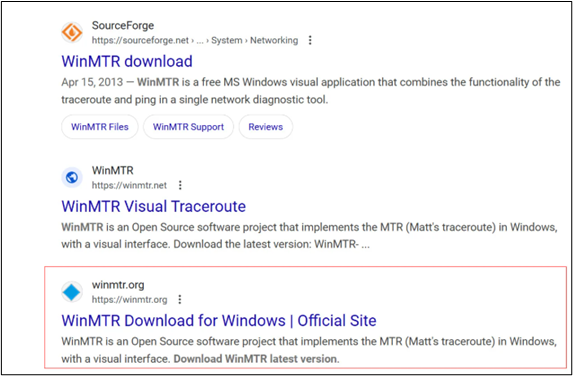
New Bumblebee Malware Campaign Targets IT Staff Through Typosquatting Tactics
A new Bumblebee malware campaign has been identified which utilized search engine optimization (SEO) poisoning and typosquatting techniques to mimic open-source projects in order to target information technology (IT) staff. The group utilized tools commonly used by IT staff to diagnose or analyze network traffic such as Zenmap and WinMTR. The threat actor developed clone websites that like the legitimate domain to trick IT workers into downloading malware onto their company networks. When interacted with, the fictitious site downloaded and delivered the intended packages as well as a trojanized malicious dynamic link libraries (DLL) which dropped the Bumblebee loader.
This campaign relies heavily on the notoriety of the programs it mimics as well as social engineering techniques to seem legitimate. The threat actor clearly has significant experience and skill coding in order to develop such a convincing fake site that successfully fooled IT specialists that regularly use the programs. Additionally, the malware exhibited sophisticated obfuscation capabilities in order to evade system detection upon download. Ensuring all domains are free from errors and have been verified can disrupt typosquatting campaigns and protect internal systems from compromise.
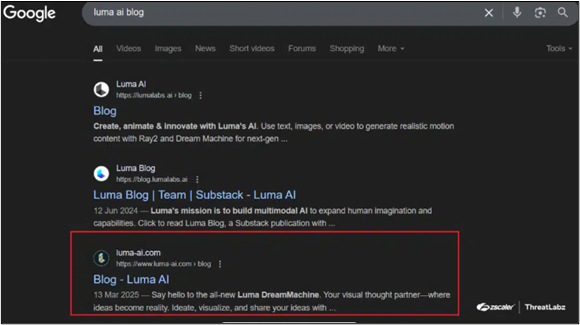
Threat Actors Are Hijacking Google AI Search Results to Deliver Malware Payloads
Threat actors have utilized Google's search functions to hijack searches for AI tools by developing AI-themed websites laced with infostealer malware. Upon interaction with the fake website, the page deploys JavaScript to fingerprint the browser and collect browser information. The visitor is then redirected to a malicious web page that includes various malware infostealer downloads. The redirection logic is hosted on AWS servers, which allows the malicious program to evade scanning detection. The campaign utilizes the current interest in AI development and often mimics the websites of large AI development brands Luma AI and ChatGPT. Most of the malicious sites were developed using the WordPress program and are search engine optimized (SEO) to attract more web traffic, expanding their targeting pool.
This campaign includes both sophisticated obfuscation and social engineering techniques. Given the new developments in the AI space, people are often unfamiliar with certain brands, allowing threat actors to take advantage of the average person's inexperience. Additionally, by utilizing legitimate systems and SEO techniques, the malicious sites can evade detection and gain legitimacy within Google’s search function increasing the likelihood of interaction. This mixture of social engineering, and system manipulation makes this campaign difficult to track and extremely effective. Checking all URLs carefully for signs of tampering such as typo squatting and unrecognized subdirectories can aid a user in identifying suspicious links
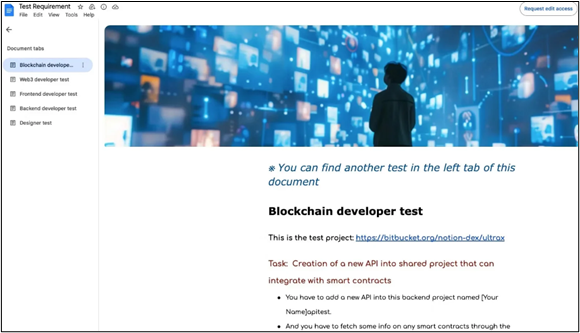
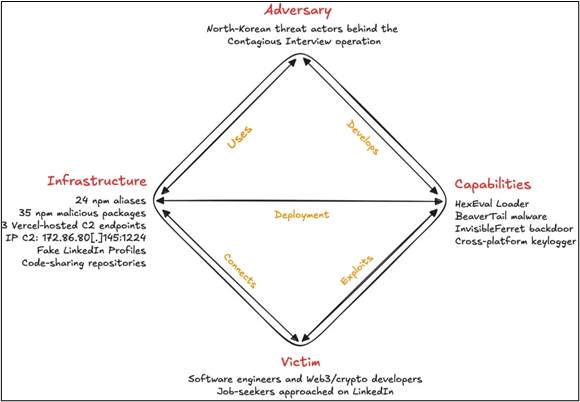
North Korean Cyber Campaign Targets Job Seekers With Fake Interview Links
North Korea initiated a new wave of cyberattacks dubbed “Contagious Interview," in which job seekers are targeted with fictitious job interview links. The links contain malicious node package manager (NPM) software packages that include info stealer malware and backdoors for future deployments. The latest wave of attacks utilizes 35 malicious packages uploaded to NPM through 24 accounts. As of this writing, there are over 4,000 downloads associated with these malicious packages. The packages are typically delivered to software engineers through North Korean operatives masquerading as job recruiters and are disguised as “coding assignments” for the applicants to complete as part of an interview process.
North Korean threat actors have been known for many years to engage in fake job application attacks. During the COVID-19 pandemic, North Korean agents would apply for remote jobs in order to infiltrate company networks to deploy malware. As these attacks have developed, they have begun to expand targeting to job applicants, especially those engaged in coding, IT, web development, and crypto. The packages typically contain info stealer malware, as well as modified backdoors, so that the threat actor can continue to steal data over a longer span of time, thus gaining access to multiple accounts to conduct further attacks. These tactics fall in line with known North Korean tactics, techniques, and procedures (TTPs) and targeting practices. Confirming the legitimacy of any downloads sent by a third party can protect against malware deployments.
Scattered Spider: Rapid7 Insights, Observations, and Recommendations
Scattered Spider has quickly become one of the most dangerous and disruptive threat groups targeting critical industries. Read Rapid7’s analysis for key insights, attack patterns, and expert recommendations to help defend your organization.
Ingram Micro Outage Caused by SafePay Ransomware Attack
A ransomware attack linked to the SafePay group has disrupted operations at Ingram Micro, one of the world’s largest IT distributors. Read the full report to understand the impact, attack details, and what it signals for supply chain cybersecurity.
Sustaining Select Efforts to Strengthen the Nation's Cybersecurity and Amending Executive Order 13694 and Executive Order 14144
Cybersecurity is now at the center of U.S. national policy—with the White House’s June 6 Executive Order (EO) updating EOs 14144 and 13694 to sharpen the focus on defending digital infrastructure, securing software supply chains, advancing encryption and post-quantum readiness, and targeting cyber sanctions specifically at foreign actors. Read the full order to understand how these shifts will impact federal agencies, industry contractors, and emerging technologies—your guide to staying ahead in a changing cyber landscape.
Iranian Cyber Actors May Target Vulnerable U.S. Networks and Entities of Interest
U.S. cybersecurity agencies are warning that Iranian state-sponsored or affiliated hackers may soon target vulnerable American networks, exploiting outdated software, weak passwords, and even critical infrastructure devices. Read the Cybersecurity and Infrastructure Security Agency's joint fact sheet now to understand the threats, discover proven mitigations, and protect your organization before it’s too late.
'CitrixBleed 2' Shows Signs of Active Exploitation
Scary news for Citrix NetScaler users: the newly discovered “Citrix Bleed 2” vulnerability (CVE‑2025‑5777) is now confirmed to be exploited in the wild—allowing attackers to steal session tokens, bypass multi-factor authentication (MFA), and hijack active user sessions. Read the Dark Reading report to learn how the flaw works, why it's critical, and what immediate patches and mitigations your team must apply.
Cybersecurity & Cargo Crime: Reducing Risk for Carriers | NMFTA's Ben Wilkens
Don’t miss this discussion as NMFTA cybersecurity expert Ben Wilkens joins on-air personalities Dave Nemo and Jimmy Mac to explore real-world cargo crime risks and proactive strategies to protect your fleet. Watch now and learn how to strengthen your defenses against evolving threats.
Billions Lost, Freight Exposed: The Real Cyber & Cargo Threats
Cargo theft and cybersecurity breaches are no longer isolated incidents—they’re a growing epidemic in freight.
Rewatch this high-stakes episode of Driving Forward with guest experts Artie Crawford and Ben Wilkens from the NMFTA.
Hosted by GLCS's Robert Bain, this episode pulls back the curtain on the evolving threats facing trucking companies and freight brokers.
Digital Defense | Joe Ohr & Artie Crawford of the NMFTA
On the latest episode of Optym's Semi-Related Podcast, NMFTA's Joe Ohr and Director of Cybersecurity Artie Crawford join host Jacob Eischen to discuss how dark-web ransomware rentals, AI-forged emails, and hacked telematics give thieves a back-door pass to your freight and how fleets can prepare a road-ready defense plan. They also preview the NMFTA’s Cybersecurity Conference this October and the no-cost tools rolling out to help carriers of every size stay a step ahead of the next breach.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!









.png)

