July 2024
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover system and rolling asset security, trending reports, and more.
Webinar: Unlocking the Potential of Seed Key Exchange
As vehicles become smarter and more connected, the need for secure communication channels is critical. This session will spotlight seed key exchange, essential for maintaining data integrity and secure interactions. Join NMFTA cybersecurity experts, Ben Gardiner and Joe Ohr, on Thursday, August 15 from 1:00-2:00 pm ET to gain insights into real-world case studies and strategies to enhance cybersecurity measures at your organization.
Whitepaper: Securing Legacy Maintenance Software
Trucking leaders, secure your legacy fleet maintenance against a hidden threat! NMFTA's "Securing Legacy Maintenance Software" whitepaper unveils the vulnerabilities lurking within your trusted, older programs. Discover how to safeguard critical data and prevent costly disruptions by implementing effective cybersecurity measures for these essential systems. Download this free resource and ensure your trucks keep moving.
Discover How Top Fleets Secure Their Operations at #NMFTACyber
October 27-29 | Cleveland, OH
This year's NMFTA Cybersecurity Conference is set to be a game-changer for the trucking industry, bringing together top fleets and experts to share their insights and strategies for navigating the ever-evolving landscape of cybersecurity. Discover what fleets and other industry experts will be speaking at #NMFTACyber via the link below.
Featured Fleets:
Thank You To Our Sponsor:
NMFTA Member, Saia, Lends Truck to DEF CON 32 Conference
A special thank you to NMFTA Member, Saia, for being the first fleet to lend one of their Class 8 trucks to DEF CON 32's Car Hacking Village (CHV) event, happening from August 8-11, 2024 in Las Vegas, NV. Those attending and participating in the Capture the Flag (CTF) challenge get the chance to learn about heavy vehicle systems and how to secure them as well as trying their hand at some introductory CTF challenges being hosted on the live vehicle network.
In This Month's Report...
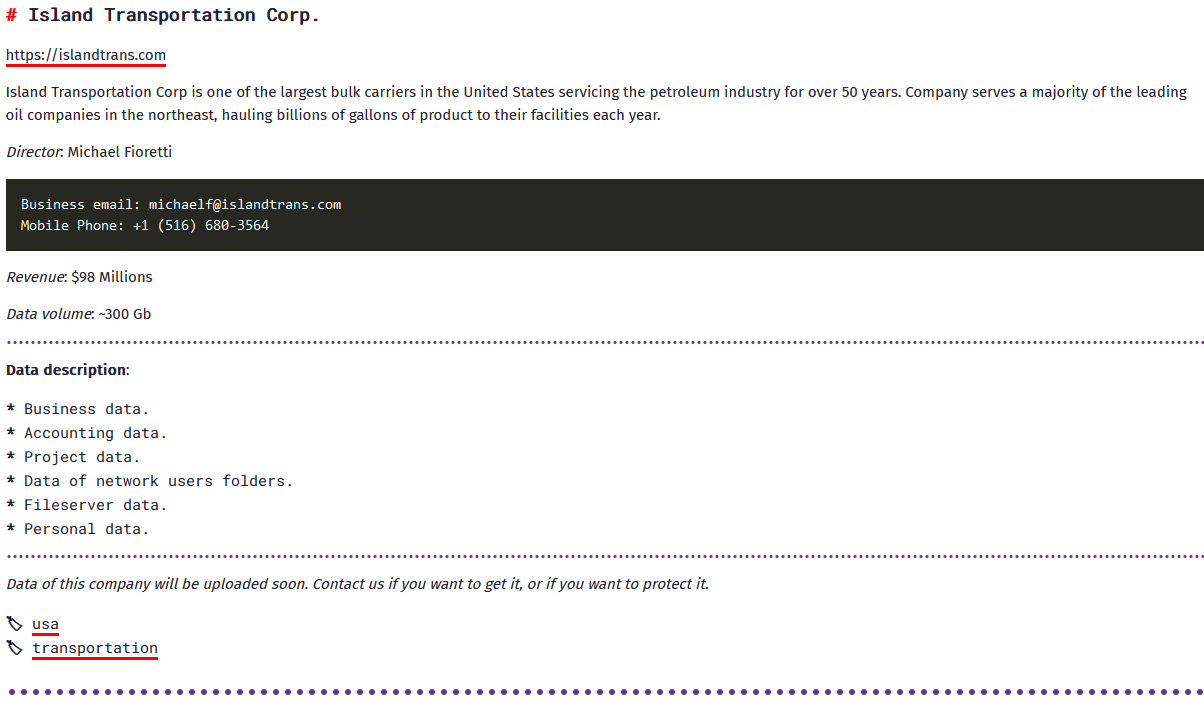
BianLian Ransomware Targets Oil and Gas Transportation Firm
On July 8, 2024, analysts identified a communication that the ransomware group BianLian posted on its dark web (DW) leak site in which it claimed to have targeted Island Transportation Corporation, a New York–based oil and gas transportation company. Island Transportation Corporation is one of the largest petroleum carriers in the northeast and claimed to service many major companies, though did not name them specifically. BianLian claimed to have acquired 300 gigabytes of data including finance data, project data, business information, personal information, and more.
Emerging in June 2022, BianLian appears to be financially motivated. The group mainly targets US-based companies and critical infrastructure but has recently begun to attack more international targets, including in Australia and Canada.
In a reference to BianLian’s tactics, techniques, and procedures (TTPs), the group normally gains access to a victim's system through valid Remote Desktop Protocol (RDP) credentials, open-source tools and command-line scripting for discovery and credential harvesting. The group then exfiltrates the victim’s data via File Transfer Protocol (FTP), Rclone, or Mega. Originally, BianLian employed a double-extortion model, but around January 2023, it shifted to primarily exfiltration-based extortion.
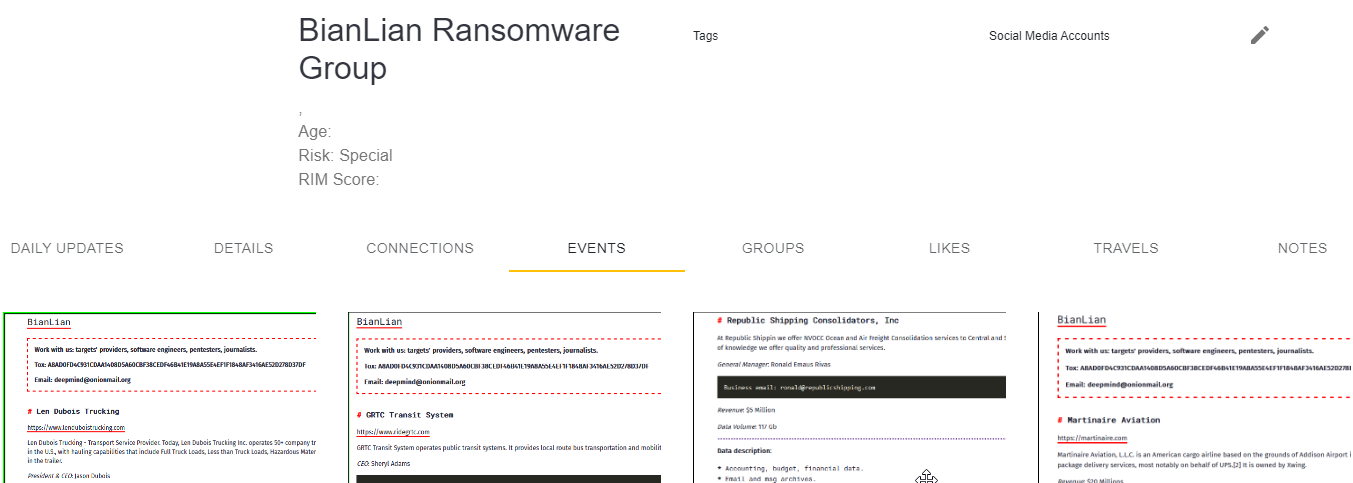
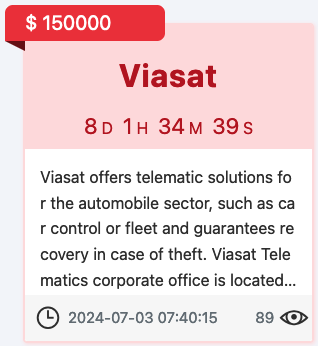
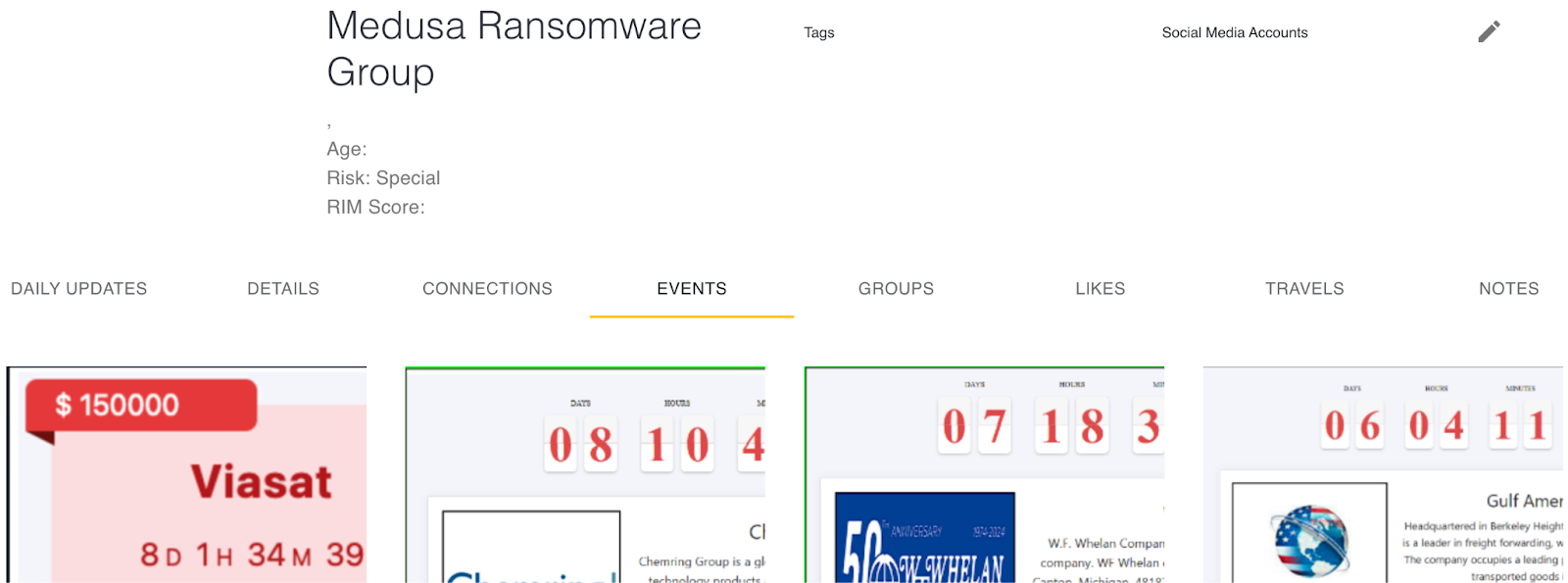
Medusa Ransomware Targets Visasat
On July 4, 2024, analysts identified a communication in which the ransomware group Medusa posted on its dark web leak site a claim of responsibility for a ransom attack against Viasat. Viasat offers telematic and communication solutions for the automobile sector such as vehicle and fleet control and communication. The Medusa ransom gang has claimed to have stolen 98.9 GB’s of data. The gang did not mention what information has been stolen although did indicate that the data will be made public on July 12, 2024.
Active since late 2022 Medusa appears to be financially motivated and is associated with the eponymous Medusa malware. The ransomware group targets corporate victims worldwide and operates in various sectors, including public administration, civil engineering, healthcare, education, construction, and hospitality. Targets are likely chosen by the group for maximum impact rather than in accordance with the industry.
In reference to Medusa’s TTPs, it generally obtains access to the victim's systems via vulnerabilities in RDP or deceptive phishing campaigns. Furthermore, the group usually implements a double-extortion tactic for additional leverage to collect ransom payments.
Cactus Ransomware Gang Targets FBT Inc. in California
On June 24, 2024, analysts identified a communication that was posted by the ransomware group Cactus in which the group claimed via its DW leak site to have targeted FBT Inc., a Bakersfield, California–based transportation and logistics company. Cactus did not indicate how much or what data it obtained but did provide proof of the hack by posting sensitive documents belonging to FBT Inc. on its DW leak site.
Cactus ransomware group appears to be financially motivated and has been active since March of 2023. The group typically targets large commercial entities. Previous Cactus victims operate in various sectors including construction, data management, retail, farming and manufacturing.
In a reference to the Cactus’ TTPs, the group leverages documented vulnerabilities in virtual private network (VPN) appliances in order to gain initial access. Analysts note that Cactus is observed to implement such tools as Chisel, Rclone, TotalExec and Scheduled Tasks in order to disable security software.
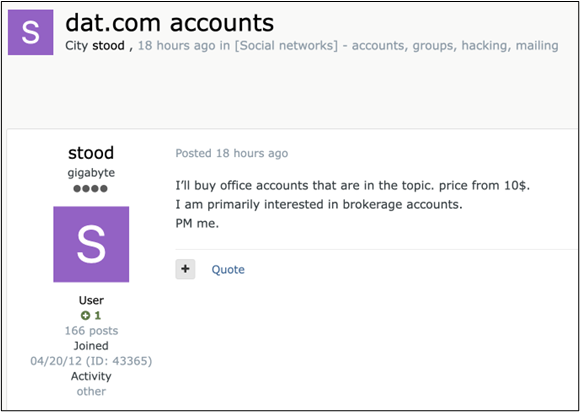
Cyber Forum User Seeking Freight Brokerage Accounts Access
On June 16, 2024, analysts identified a communication in which a Russian speaking user known as Stood is seeking freight brokerage accounts. Of note, the user mentioned DAT.com specifically although the user potentially referenced it as an example platform.
Furthermore, analysts identified that previous communications posted by the user were oriented towards web fraud, credential collection and web traffic routing to fraudulent sites.
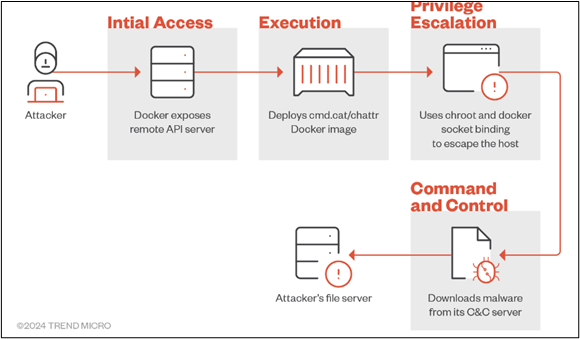
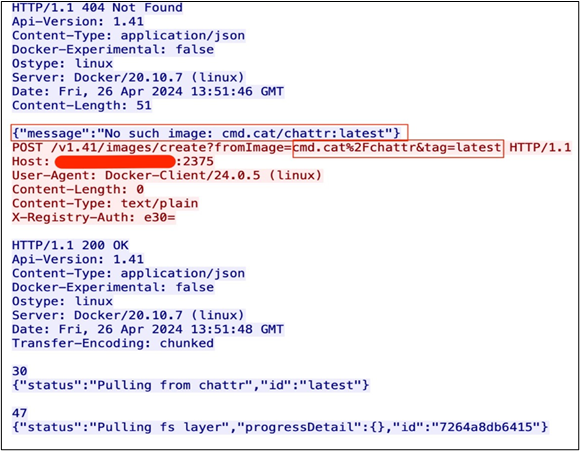
New CryptoJacking Campaign Commando Cat Exposes Vulnerabilities in Docker Remote API
A new cryptojacking attack campaign known as Commando Cat has been exposing vulnerabilities in docker remote application programming interface (API) servers to deploy crypto currency miners. The campaign, active since the beginning of 2024, involves deploying containers, which are static files that include executable code. The containers are composed of system libraries, tools, platform settings, and software programs, generated through the publicly available Commando Project on GitHub. The project creates docker images, which are templates for the creation of containers. The attackers use this program to create a cmd.cat/chattr docker image container with executable code that retrieves the malware payload from the attacker’s own command-and-control (C2) infrastructure.
To gain initial access, the attacker deploys what appears to be a harmless docker image into the target system and then uses a change root (chroot) command to deploy the payload into the target system and curl/wget to download the malicious code in order to bind it to the host system. This grants the attacker unrestricted access to the host’s system, where it can deploy its cryptojacking script.
The Commando Cat attack campaign exposes vulnerabilities in docker remote API servers as the generated docker images utilized in the attack can bypass security systems and deploy malware undetected. Additionally, the open-source nature of the docker images makes the process accessible for malicious actors. While the process is currently being utilized in cryptojacking schemes to steal central processing unit (CPU) power, the TTPs of gaining access to host systems to execute scripts, as used in the Commando Cat campaign, has the potential to be used in other forms of cyber attacks. Given its open-source quality, malicious actors will likely continue to develop this exploit if new container security features are not released to combat the tactics used during the Command Cat campaign.
Threat Actor |
Commando Cat |
Malware Identification/ Infrastructure |
Containers/docker images: Infection Chain: |
Relevant Vulnerabilities |
None identified |
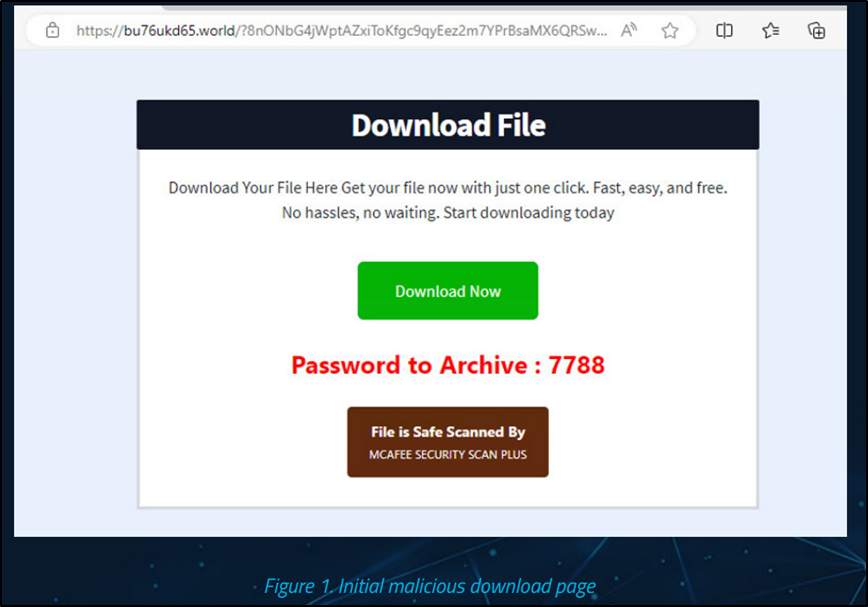
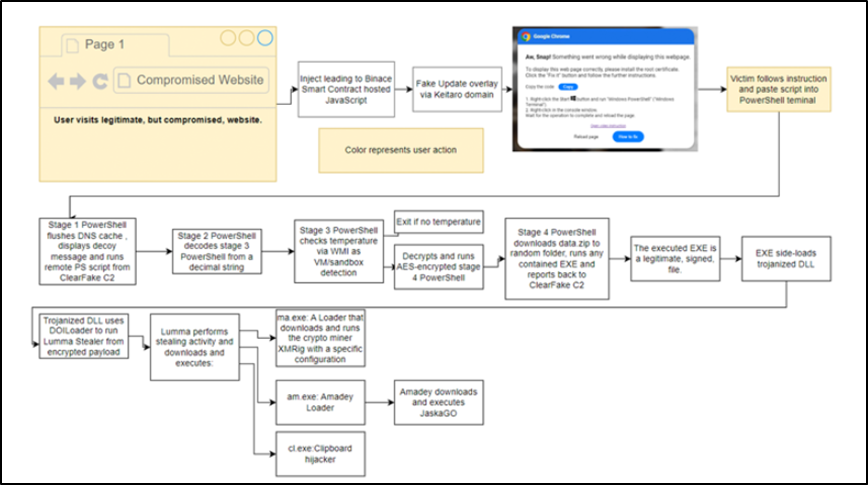
Threat Actors Deploy Hijack Loader Malware in Attacks Using Free Software Lures
Multiple threat actors were reported to be coercing unsuspecting victims to download free or illegal versions of commercial software to deliver a malware loader called “Hijack Loader” (AKA DOILoader & IDAT Loader), which subsequently deploys an information stealer known as “Vidar Stealer.” The Vidar info-stealer is commonly delivered through phishing campaigns and sites advertising cracked software. The malware itself comes with a wide range of capabilities to harvest sensitive information from infected hosts. Vidar has also been observed to be distributed via rogue Google Ads and an additional malware loader dubbed “Bumblebee.” What makes the campaign especially noteworthy is the use of dynamic-link library (DLL) side-loading techniques to stealthily launch Hijack Loaderm, which then acts as a conduit to drop Vidar Stealer by means of an AutoIt script.
In addition to using Vidar Stealer to hijack sensitive credentials from web browsers, the attack chain leverages additional payloads to deploy a cryptocurrency miner on the compromised host. The campaign coerces victims who land on a spoofed website into manually executing a PowerShell script to address a supposed issue with viewing web pages. The PowerShell script then serves as a launchpad for Hijack Loader, which subsequently delivers the Vidar Stealer malware.
Hijack Loader was first identified in the summer of 2023, and provides threat actors a variety of loading options for deploying second stage malicious payloads onto compromised networks, including Amadey, Lumma Stealer, Racoon Stealer v2, and Remcos RAT. In addition, Hijack Loader is now equipped with new detection and analysis evasion capabilities, which further enhance its effectiveness. Vidar is a commercial information stealer that was initially identified in 2018, and is an extremely dangerous malware that steals information and cryptocurrency from infected users. On its official website, Vidar is available for purchase based on the malware-as-a-service (MaaS) business model for a price of anywhere between $130 and $750, depending on the terms and length of the subscription.
However, a scaled-down version of the malware can be obtained for $250. Customers also have the flexibility to personalize some of the tool’s features, such as the types of information to be targeted. Vidar is specifically designed to steal browser histories, cookies, credentials, cryptocurrency wallets, and two-factor authentication (2FA) software data. The continued success of tools such as Vidar and their demonstrated use in deploying later-stage payloads reiterates the threat associated with MaaS programs, as they allow for less sophisticated threat actors to perpetrate their own cyber attack campaigns and offer an even wider range of threat actors access to compromised networks.
Threat Actor |
Vidar Stealer MaaS operators |
Malware Identification/ Infrastructure |
Malware tools: TTPs used in relevant campaign: |
Relevant Vulnerabilities |
None identified |
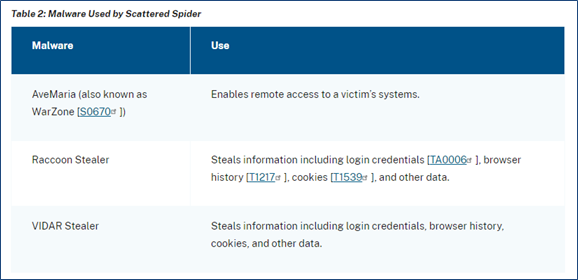
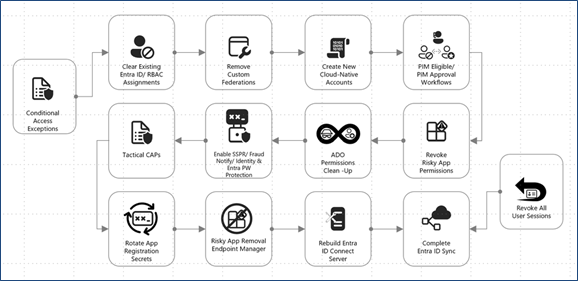
Scattered Spider Hacking Collective Targets Data Used in SaaS Environments
On June 20, 2024, analysts identified reports that a hacking collective tracked as Scattered Spider has recently transitioned to a TTP of targeting cloud-based enterprise data repositories used in software-as-a-service (SaaS) application environments. Scattered Spider is targeting cloud-based data warehouse facilities using stolen credentials obtained from multiple infostealer malware infections. These involve the use of hijacked credentials to access SaaS applications protected by single sign-on providers. Scattered Spider exfiltrates the files through the use of various cloud synchronization utilities, such as Airbyte and Fivetran, to transfer data from cloud-hosted data sources to external attacker-owned cloud storage resources, such as S3 buckets. These applications only require credentials and a path to the resources to sync the data to an external source automatically, often without the need for a subscription or expensive costs.
The Scattered Spider hacktivist collective is assessed as some type of offshoot or splinter group of a larger cohort of online cyber criminals that has dubbed itself "the Community," or "the Com.” It primarily operates in the United States and other Western countries, and has breached dozens of American organizations and their downstream third-party supply chains. Scattered Spider is a financially driven threat actor, and is primarily known for its SIM-swapping tactics and highly sophisticated credential-phishing skills. These include calling into enterprise help desks and resetting Okta credentials to take over accounts, notably using these TTPs to targeting the MGM and Caesars Entertainment resorts in Las Vegas, NV, in September 2023.
Scattered Spider’s current campaign underscores the corresponding vulnerabilities of storing large amounts of sensitive data on SaaS-hosted applications. When using SaaS, organizations face an increased risk of user account compromise. This risk is partly related to SaaS accounts being directly exposed to the Internet. Also, geographic restrictions are not a major factor in SaaS services, enabling brute force and other types of credential-based attacks to originate from any geographic location.
Threat Actor |
Scattered Spider: AKA UNC3944, Scatter Swine, Octo Tempest, and 0ktapus |
Malware Identification/ Infrastructure |
Novel TTP → Targets cloud-based enterprise data repositories used in SaaS application environments → Hijacked credentials to bypass protected by single sign-on providers. SaaS applications → Past Scattered Spider operations abuse SaaS permissions → SaaS is critical for enterprise operations → Increases vulnerability to supply chain attacks Cloud synchronization utilities → E.g., Airbyte and Fivetran → Used to transfer data from cloud sources |
Relevant Vulnerabilities |
None identified |
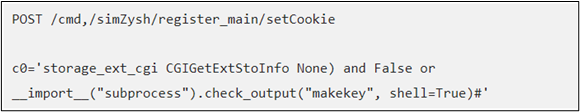
Mirai-like Botnet Takes Advantage of Vulnerabilities in EOL Zyxel Software
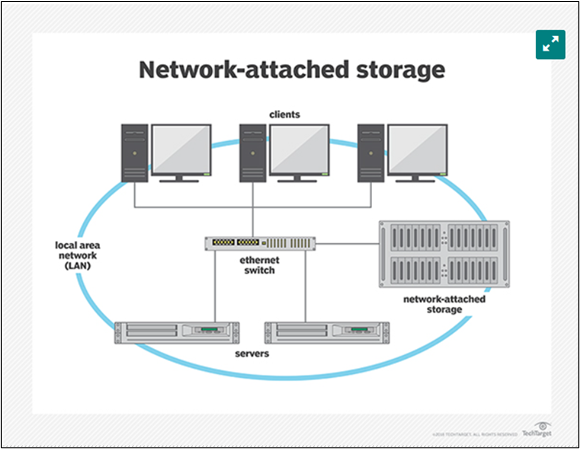
Throughout June 2024, indications that a Mirai-like botnet had attacked end of life (EOL) Zyxel network-attached storage (NAS) devices were identified. A botnet is a group of internet connected devices infected with malicious software that can be used in a number of different forms of cyberattacks. Mirai is a form of malware that infects devices that run on ARC processors, turning them into a network of remotely controlled bots. The Mirai botnet works by scanning the internet for ARC processors, which run on a stripped-down version of the Linux operating systems and infecting those devices. Its main purpose is to launch distributed denial-of-service (DDoS) attacks like those committed by hacktivist groups to briefly shut down the systems of targeted entities.
The Mirai-like botnet shares some characteristics with the original Mirai botnet but does not share the exact same code base. The identified botnet has an updated arsenal of exploits. The Mirai-like botnet exploited a vulnerability known as CVE-2024-29972, which is a critical bug identified in early June 2024 with a 9.8 out of 10 severity rating. The bug affected Zyxel NAS326 and NAS542 devices. The vulnerability is known as a command injection flaw, which allows an attacker to relay malicious code through an application to another system. In this instance, the malicious actor can execute commands on the affected devices by bypassing the Zyxel authenticator and opening up a backdoor into the device. Zyxel released a patch for this exploit at the same time that the exploit was publicly identified.
This exploit exposes vulnerabilities in EOL devices that malicious actors commonly target. In many cases, EOL devices are not given patches when exploits are identified, as their systems are no longer supported. This particular case is an exception due to the severity of the vulnerability. A common way malicious actors gain entry into a network is through out-of-date applications on target computers that contain unpatched exploits on unsupported systems. These vulnerabilities are especially potent on NAS devices, which can grant malicious actors access to entire connected networks.
NAS devices are regular targets of cyberattacks, specifically ransomware attacks, due to their cloud based storage capability, minimal security features, and its status as an Internet of Things (IoT) device connected to a main system. These aspects can provide an avenue for undetected entry and maintained persistence. NAS devices are vulnerable to many forms of malware and cyberattacks, including ransomware, DDoS, and information exfiltration. Due to the wide range of vulnerabilities and versatility of application access, it is critical to keep devices and applications up to date to avoid providing additional exploits to malicious actors probing into targeted systems.
Threat Actor |
Mirai-like botnet |
Malware Identification/ Infrastructure |
Infection Chain: → Out-of-date systems with critical vulnerabilities provide an avenue for malware to infect EOL Zyxel NAS devices. → Malware infects NAS devices and takes over the system as a botnet to deploy DDoS attacks. Exposes need to keep systems and applications up-to-date to avoid providing malicious actors avenues for system entry. |
Relevant Vulnerabilities |
None identified |
Implement strong security measures. This includes using firewalls, antivirus software, and data encryption to protect your systems from unauthorized access. You should also regularly update your software and patch vulnerabilities.
August 8-11
Las Vegas, NV
NMFTA is excited to once again sponsor DEF CON 32's Car Hacking Village, happening at the Las Vegas Convention Center. This challenge is an interactive and educational gathering where cybersecurity enthusiasts and experts explore and demonstrate vulnerabilities in automotive systems to improve vehicle security.
August 19-21
Lake Geneva, WI
Join NMFTA Cybersecurity Research Engineer, Anne Zachos, at the 2024 TMHA Safety & Security Conference. NMFTA looks forward to connecting with peers in the transportation industry, and sharing insights and recommendations on how to keep your rolling assets moving.
Protecting Trucks from Cyberattacks Through Legacy Maintenance Software
For most carrier fleets, there is nowhere the truck is more exposed to cyberattack than in the maintenance shop. Read this article by NMFTA chief operating officer, Joe Ohr, to learn what steps you can take to secure your fleet maintenance software.
Businesses Lack Understanding of Risks with Third-Party Vendors, Suppliers and Contractors: Survey
The survey specifically looks at how companies are tackling risk assessment within their vendor and supplier populations, the types of risks they are prioritizing, and their use of technology and artificial intelligence (AI) to monitor risk, among other themes.
Transportation a Top 10 Target of Cyberattackers
No other industry saw a year-over-year increase larger than transportation, with only the financial services sector coming close. Read this article to discover critical insights from the data collection experts at SOAX.
CDK: 'Substantially All' Car Dealerships Restored After Hack
Nearly 15,000 Car Dealerships were affected two weeks ago.
Listen: Are Cybersecurity Threats Growing in Freight?
NMFTA's Joe Ohr chatted with The Freight Coach's Chris Jolly last month and discussed the importance of making APIs more secure; how hackers are exploiting major cloud services to steal data and tips for staying safe; and how listeners could attend the trucking industry's only cybersecurity conference, #NMFTACyber, this October.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!

.jpg?width=1000&height=563&name=0624-CyberWebinar-0815-1000x563%20(2).jpg)










