January 2025
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover enterprise system and rolling asset security, trending reports, and more.
Hackers Are Targeting You, Your Truck, and Your Profits—Fight Back with Our NEW Cybersecurity Guidebook!
Cyberthreats are a growing challenge, but protecting your operations doesn’t have to be complicated or expensive. Our recently released Cybersecurity Best Practices Guidebook, packed with budget-friendly solutions, step-by-step tips, and real-world examples, is tailored specifically for small fleets and owner operators. Don’t leave your livelihood vulnerable—download the guidebook today and take control of your cybersecurity!
2025 Insights for Trucking Leaders
The new year brings in new threats. As we move into 2025, new cybersecurity threats—from AI-enhanced phishing to cyber-enabled cargo theft—are reshaping the landscape. Download our comprehensive report and explore critical developments you need to understand to stay ahead.
Speak at NMFTA's Cybersecurity Conference this Fall
October 26-28, 2025 | Austin, TX
The call for abstracts is now open for the NMFTA 2025 Cybersecurity Conference, dedicated to exploring the crucial intersection of cybersecurity and the trucking industry.
Save the Date for 2025 #NMFTACyber
October 26-28, 2025 | Austin, TX
Whether you're an IT pro on the front lines, a trucking executive seeking strategic guidance, or a cybersecurity researcher pushing boundaries, the NMFTA Cybersecurity Conference has something for you. Make plans to join us at the NMFTA Cybersecurity Conference, October 26-28, 2025, at the Westin Downtown Austin.
Why Is The U.S. Considering Banning
TP-Link?
New Blog
Have you heard about the United States (U.S.) possibly banning TP-Link? This article dives into the reasons behind the consideration and what it could mean for businesses and individuals using their products. It’s an eye-opener about the potential risks tied to technology we rely on every day.
Next Month! Join NMFTA at Manifest
NMFTA will be hosting a cybersecurity session, "Shaping Cybersecurity: Reflecting on a Decade of Trends and Preparing for Future Threats" with insights from Estes Express Lines' Todd Florence, Ward Transport & Logistics Corp.'s Mike Zupon, NMFTA's Joe Ohr and Artie Crawford. Gain actionable insights on emerging threats, shifting regulations, and state-of-the-art technologies to help you stay ahead in the ever-evolving cybersecurity landscape.
Use our link below and save $200 on your registration.
February 13, 2025 | 1:00 - 2:00 PM ET
Join NMFTA for a no-charge webinar, tailored specifically for owner operators. This webinar will dive into insights from our newly released Cybersecurity Best Practices Guidebook. Don't miss out on tips and strategies to safeguard your business and protect your data.
Watch on Demand
Protect yourself and your operation from cyberthreats. Watch a discussion on the core cybersecurity best practices that an owner operator or small fleet can implement to significantly boost cyber-resilience without breaking the bank.
Watch on Demand
Rewatch the NMFTA Cybersecurity team and Transport Topics webinar that will explored the rapidly growing role of AI in the transportation industry. They examined both the significant benefits AI offers and the critical risks it poses, providing a balanced view of its potential impact.
In This Month's Report...
Password Spraying Attacks Provide Significant Success Rates
Password spraying attacks are a type of brute force attack in which threat actors attempt to force access through the use of a constant, default, password across a large number of accounts. During this process the threat actor is attempting to identify accounts utilizing constant passwords while potentially avoiding account lockouts.
According to Trellix reports throughout November, the password spraying attack vector has resulted with prolific results for threat actors targeting North American and European entities. As such the top targeted sectors included the education, energy, and transportation sectors.
Examples of threat actors utilizing the password spraying vector include the Midnight Blizzard, a Russian-based threat actor which has been attributed to the Foreign Intelligence Service of the Russian Federation and has targeted Microsoft senior executives during 2023, the Chinese-based Storm-0940 threat actor which has targeted entities throughout North America and Europe and most recently a joint advisory published by multiple entities including the Federal Bureau of Investigations (FBI), Cybersecurity & Infrastructure Agency (CISA), and National Security Agency (NSA) in which Iranian threat actors have utilized the aforementioned vector during campaigns in October 2023.
Analysts note that multiple landscape shifts which have occurred during 2024 assist threat actors with collecting potential targets, and further targeting these victims. Such events include:
- The collection and publication of the ‘3.3BUniqueEmailsByAddkaAnd- BreachForums’ in which the BreachForums cyber user known as Addka72424 has collected and posted 3.3 billion unique email addresses previously posted and collected from different publicly accessible sources and data leaks.
- The collection and publication of the ‘RockYou2024’ password compilation which has been published by the cyber forum user known as ObamaCare and includes roughly 10 billion unique passwords.
Both events and the ongoing successful campaigns showcase the potential threat actors hold by utilizing information which has been published publicly of which include password spraying tools.



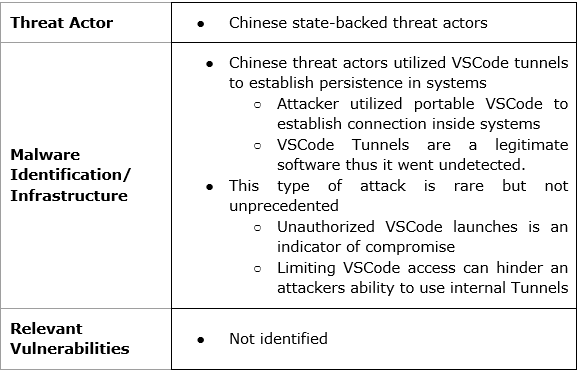
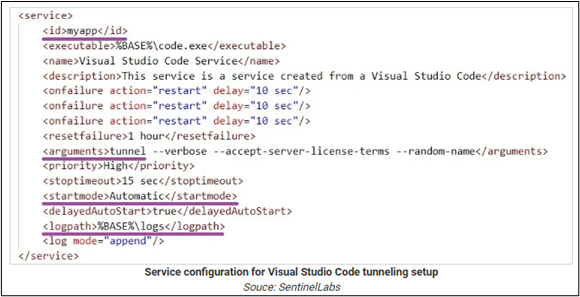
Chinese Hackers Target IT Services Through Visual Studio Code Tunnels
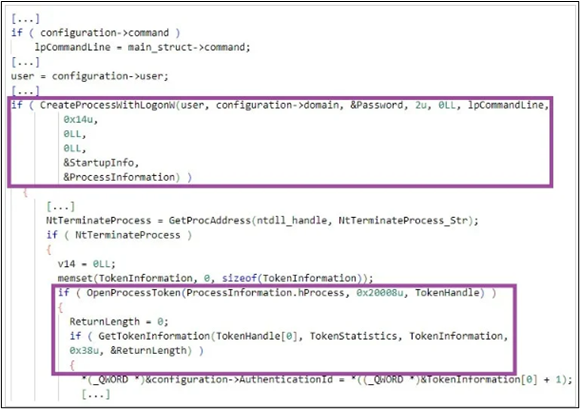
Chinese hackers have been regularly targeting Western telecommunications and IT companies for the last few years as part of a campaign against critical infrastructure. In a recent attack in Southern Europe, Chinese threat actors were identified utilizing Visual Studio Code (VSCode) tunnels to maintain established remote access within compromised systems. VSCode tunnels are a built-in feature of Microsoft's Remote Development software, which allows developers to access remote systems via VSCode. These tunnels allow developers to execute command codes and access internal files remotely increasing ease of access to the system for developers. However, if not properly succeeded this also creates a backdoor vulnerability threat actors can exploit.
To gain initial access the Chinese threat actors utilized an automated Structured Query Language (SQL) injection exploitation tool known as sqlmap on some internet-facing web servers. The attackers then deployed a Hypertext Preprocessor (PHP) webshell, which allowed the attacker to execute commands remotely and deploy malware payloads into the compromised system. Through this that attacker gained Remote Desktop Protocol (RDP) access to move within the compromised system wherein they deployed a portable VSCode and established the Tunnel as a backdoor into a system.
The use of legitimate services within systems is an increasingly common tactic, techniques, and procedures (TTP) that threat actors are using. As code becomes more technical and more systems develop different internal services, there become more ways for threat actors to manipulate legitimate software. The internal Microsoft system did not catch the VSCode tunnel, as it is a Microsoft system that security features were not trained to identify as a threat. The active times that the backdoor was utilized coincides with active work hours in China, strengthening the initial identification that Chinese threat actors were involved. This exploitation of VSCode tunnels is rare, but is likely to be utilized by threat actors until a fix is implemented. Monitoring for unusual VSCode launches and file transfers can indicate compromise. Limiting the use of Code tunnels can prevent malicious ones from becoming lost in a system, and limiting their use to certain authorized personnel can make it harder for threat actors to make use of VSCode tunnels without obtaining admin credentials.
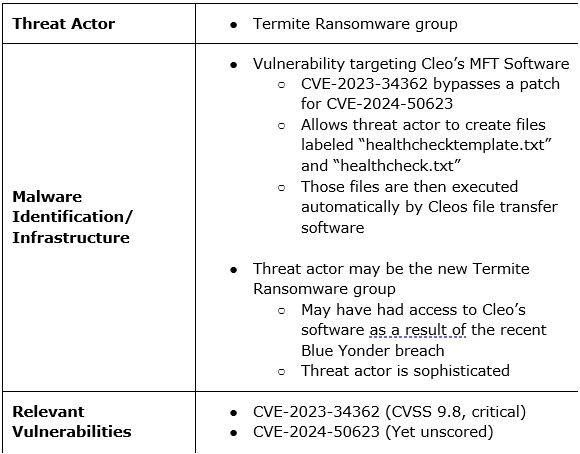
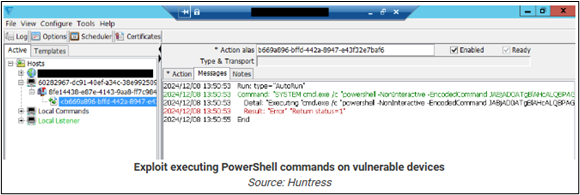
Unknown Threat Actor Utilizes New Cleo Zero-Day Flaw in Data Theft Attacks
An unknown threat actor has utilized a new zero-day vulnerability in Cleo managed file transfer (MFT) software tracked as CVE-2023-34362. The flaw is actually a bypass for a previously patched vulnerability tracked as CVE-2024-50623, which was patched in October 2024. The patch appears to be incomplete, as even updated systems are still vulnerable to exploitation and have been targeted in the most recent round of attacks.
CVE-2023-34362 is a remote code execution flaw that allows a threat actor to write files identified as “healthchecktemplate.txt” and “healthcheck.txt” into the autorun director of the target. When the Cleo software automatically runs the files, payloads contained within the files, as well as powershell commands, are downloaded and executed. The aforementioned powershell commands can download additional payloads and wipe malicious files to avoid detection and hinder the malware's identification.
While the threat actor is unknown at this time, researchers suspect the newly founded ransomware group known as Termite is responsible. Active since April 2024, Termite may be a rebrand of the group Babuk ransomware given its code appears to be an updated version of Babuk’s. The group claimed responsibility for the Blue Yonder breach that affected dozens of multinational and Fortune 500 companies in November 2024. As a part of that breach, Blue Yonder utilized an instance of Cleo’s software in its system, creating a possible access point to the company's software and allowing the group to identify the vulnerability.
The use of CVE-2023-34362 to bypass CVE-2024-50623 indicates that the threat actor responsible for the identified campaign is technically advanced. The exploit affects not only those systems that lack the patch update from October, but also fully updated systems. The presence of files labeled “healthchecktemplate.txt” and “healthcheck.txt” is an indicator of compromise. Any systems that utilize Cleo’s secure file transfer products, Cleo LexiCom, VLTrader, and Harmony are at risk and should be monitored regularly until Cleo comes out with a patch for the vulnerability.

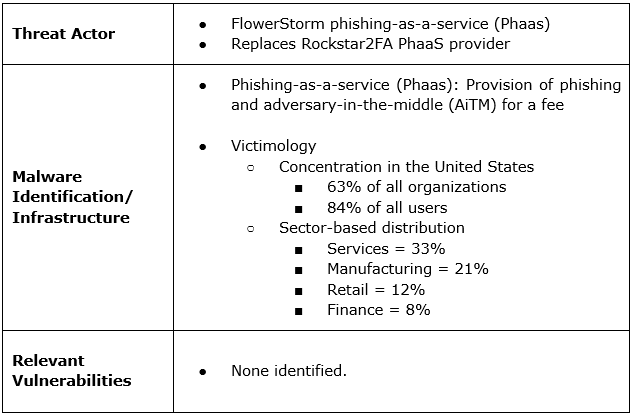
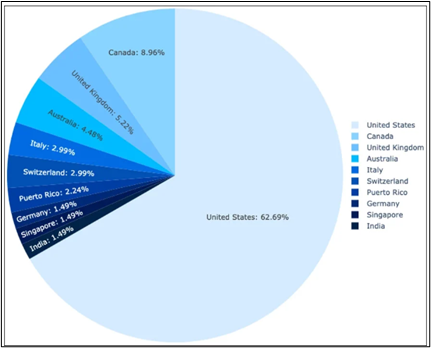
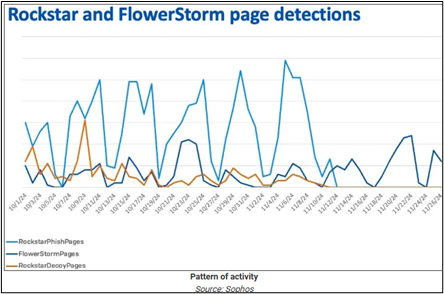
New Phishing-as-a-Service Platform FlowerStorm Gains Popularity with U.S.-Focused Attacks
A new Phishing-as-a-Service (PhaaS) platform known as FlowerStorm has rapidly grown in popularity, assuming much of the market share left behind following the shutdown of a previously active service known as Rockstar2FA. Rockstar2FA used to offer adversary-in-the-middle (AiTM) attack capabilities targeting Microsoft 365 credentials. FlowerStorm has supplanted Rockstar2FA in this space using much of the same infrastructure, offering paid access to a platform that specializes in AiTM and phishing attacks. Within the scope of FlowerStorm’s operations, 63% of all organizations and 84% of all users targeted in these attacks are located in the United States. In terms of sectors, businesses in services, manufacturing, retail, and finance are the most commonly targeted, reporting 33%, 21%, 12%, and 8% of all attacks, respectively. The platform utilizes phishing portals to mimic legitimate sources in order to farm data. Additionally, the platform stresses the use of multi-factor authentication (MFA) to prevent exposure and secure its backend.
FlowerStorm may be a reprand of Rockstar2FA as it exhibits many close similarities. Their operations appear to be sequential with FlowerStorm’s rise occurring immediately after Rockstar2FA fall. Both groups utilize similar domains and operate in the same cyber fields. Its TTPs expose a linear development between the platforms and show that the platform is continuing to gain traction indicating it likely has staying power. The significant concentration of FlowerStorm attacks that have taken place in the United States highlights the PhaaS service provider’s popularity among threat actors that are active in the country. This geographic concentration is likely to continue given the overlap in the sector-based distribution of attacks and the size of those sectors in North America.
Choosing Secure and Verifiable Technologies
Make smarter, safer technology choices with CISA's guide to secure and verifiable technologies. Read the article below and get practical advice to help protect data and ensure trust in the tools you use every day.
What Security Lesson Did We Learn in 2024?
Revisit key cybersecurity lessons from 2024, shared by industry experts in this insightful article. Read the article below to improve your strategies and understand the latest risks. This quick read offers valuable takeaways to protect your organization in the year 2025.
Critical Infrastructure Ransomware Attack Tracker Reaches 2,000 Incidents
Ransomware attacks on critical infrastructure are escalating, with over 2,000 incidents tracked by this university-led initiative. Read the article linked below and explore the alarming trend affecting essential systems worldwide.
China's Salt Typhoon Adds Charter, Windstream to Telecom Victim List
Dive into the details of China's Salt Typhoon cyberattacks targeting major telecom providers like Charter and Windstream. The article linked below reveals the scope of these breaches and offers crucial insights into protecting against advanced nation-state cyberthreats.
Trucking: What's in Store for 2025?
As the end of year approaches, the trucking industry is gearing up for 2025. What will next year have in store for the sector, its drivers and freight markets?
NMFTA's cybersecurity team was recently interviewed by Inside Lane's Shefali Kapadia. Read their top trends and predictions for 2025.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!







.jpg)




