February 2025
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover enterprise system and rolling asset security, trending reports, and more.
Plan Your Defense Against Cyberthreats Our NEW Checklist.
Cyberthreats targeting the transportation industry, including small fleets and owner operators, are increasing in 2025. You need to make cybersecurity a top priority to keep your operations afloat. The Cybersecurity Controls Checklist from NMFTA provides a practical, step-by-step guide to securing your business against cyberattacks. Download the checklist and implement simple but crucial steps toward strengthening your cybersecurity defenses.
Hackers Are Targeting You, Your Truck, and Your Profits—Fight Back with Our Cybersecurity Guidebook!
Cyberthreats are a growing challenge, but protecting your operations doesn’t have to be complicated or expensive. Our recently released Cybersecurity Best Practices Guidebook, packed with budget-friendly solutions, step-by-step tips, and real-world examples, is tailored specifically for small fleets and owner operators. Don’t leave your livelihood vulnerable—download the guidebook today and take control of your cybersecurity!
2025 Insights for Trucking Leaders
The new year brings in new threats. As we move into 2025, new cybersecurity threats—from AI-enhanced phishing to cyber-enabled cargo theft—are reshaping the landscape. Download our comprehensive report and explore critical developments you need to understand to stay ahead.
NMFTA Announces Major Enhancements to Telematics Security Requirements Matrix
New Press Release
NMFTA has announced significant enhancements to its Telematics Security Requirements Matrix, a critical tool for ensuring cybersecurity in the transportation industry. Read the press release and learn how you can stay informed about the latest security protocols and best practices essential for protecting your fleets.
Why Is The U.S. Considering Banning
TP-Link?
New Blog
Have you heard about the United States (U.S.) possibly banning TP-Link? This article dives into the reasons behind the consideration and what it could mean for businesses and individuals using their products. It’s an eye-opener about the potential risks tied to technology we rely on every day.
Call for Abstracts are Open for
NMFTA's Cybersecurity Conference
October 26-28, 2025 | Austin, TX
Submit your call for abstracts for the NMFTA 2025 Cybersecurity Conference, This is an excellent opportunity to share your insights, research, and innovations with a diverse audience. The submission deadline is Friday, February 28, 2025.
Save the Date for 2025 #NMFTACyber
October 26-28, 2025 | Austin, TX
Whether you're an IT pro on the front lines, a trucking executive seeking strategic guidance, or a cybersecurity researcher pushing boundaries, the NMFTA Cybersecurity Conference has something for you. Make plans to join us at the NMFTA Cybersecurity Conference, October 26-28, 2025, at the Westin Downtown Austin.
February 13, 2025 | 1:00 - 2:00 PM ET
Today, join NMFTA for a no-charge webinar tailored specifically for owner operators. This webinar will dive into insights from our newly released Cybersecurity Best Practices Guidebook. Don't miss out on tips and strategies to safeguard your business and protect your data.
March 13, 2025 | 1:00 - 2:00 PM ET
In March, NMFTA will host the third installment in the roadmap to resilience series, targeted at mid-sized fleets (50 – 1000 power units). This webinar will provide more advanced guidance and begin to incorporate technical controls and governance practices. Click below to register.
Watch on Demand
Protect yourself and your operation from cyberthreats. Watch a discussion on the core cybersecurity best practices that an owner operator or small fleet can implement to significantly boost cyber-resilience without breaking the bank.
In This Month's Report...
Server Misconfiguration Exposes Database on Movement of Electric Vehicles
A data breach originating from misconfigured storage servers at Volkswagen's software subsidiary, Cariad, has exposed sensitive information from approximately 800,000 electric vehicles across a variety of brands and regions including Volkswagen, Audi, Seat, and Skoda. This data was stored on Amazon Web Services (AWS) cloud storage and was publicly accessible for several months due to a misconfiguration. The compromised data included location information for about 460,000 vehicles, with precise location accuracy reaching up to centimeters. The breach further exposed personally identifiable information (PII) such as names, email addresses, phone numbers, and physical addresses of vehicle owners.
According to identified reports, the breach was initially discovered by a whistleblower. Cariad then moved to secure the data and issued notices to customers indicating that no further action was necessary, as no sensitive information such as passwords or payment data was affected. Cariad had also emphasized that the data had several security mechanisms that were required in order to access the data, further lowering the chances of unauthorized access. The details potentially offered to threat actors made it possible to build in-depth movement patterns of individuals and vehicles, revealing sensitive information. This incident underscores the importance of data security measures to protect customer information and maintain data trust and confidentiality.

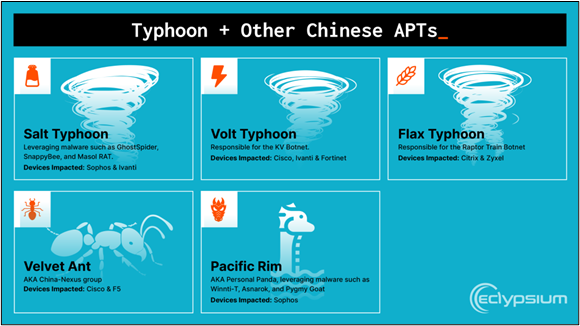
U.S. Treasury Department Confirms Chinese Cyberattack via Third-Party Service
In December 2024, the U.S. Treasury Department confirmed that the government agency experienced a cybersecurity breach, which it attributed to a Chinese state-sponsored threat actor. The Chinese attackers exploited a vulnerability in BeyondTrust, a third-party remote management software that the Treasury Department used internally for technical support activities. BeyondTrust detected suspicious activity in which threat actors obtained a key which secured a cloud-based service and offered threat actors remote access to Treasury workstations and unclassified documents. Upon the identification of the suspicious activity, BeyondTrust informed the Treasury Department of the breach.
Following the breach, the Treasury Department began collaborating with the US Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigations (FBI) to assess the breach's impact. Initial investigations classified the incident as a "major cybersecurity incident”, which underscores the vulnerabilities and possible avenues of infection associated with third-party service providers and the critical importance of implementing cybersecurity measures. These incidents further highlight the need for organizations to implement security protocols, regular suspicious activity evaluations, and ensure that third-party services adhere to the highest security standards to safeguard sensitive information.
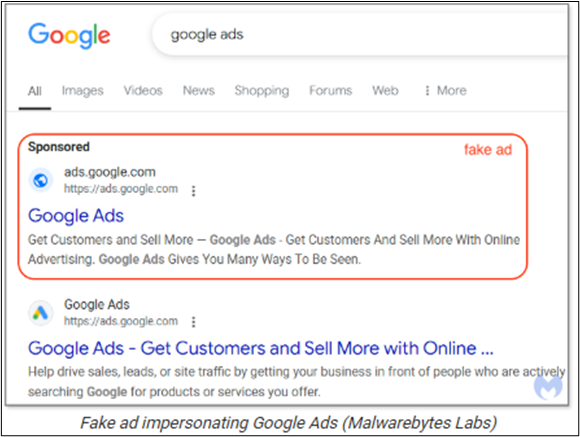
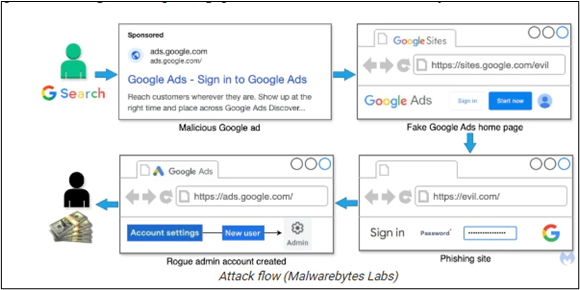
Hackers Observed Using Google Search Ads in Malvertisements Phishing Campaign
A recent cybercampaign has been identified in which hackers utilize Google Ads to promote phishing sites to steal advertisers’ credentials for the ads platform. Essentially, the hacker purchases fictitious ads on Google search result pages or other Google-affiliated web pages where the ads appear. Upon interaction, the link will take the user to a login site designed through the Google Sites program to imitate the Google Ads homepage, where login credentials are input and stolen. The hacker can then take over the Google Ads account.
This form of phishing attack is known as malvertisment. After the credentials are taken the victim may receive login emails from atypical locations. If no action is taken, the hacker is able to create an administrator account and hijack the Google Ads account entirely. The attacks may originate from Brazil, as some login notification messages received by victims have originated from Brazil. Other possible locations include Hong Kong and China.
The Google Sites platform is regularly used to host phishing campaigns because it allows threat actors to develop their own websites that imitate login pages. Threat actors will often use the customizable features on Google Sites to camouflage their phishing sites as legitimate. Google regularly blocks ads that are identified as fictitious, but more ads replace the blocked ones making the problem seem unmanaged. Checking the URLs of websites that require login credentials can safeguard against accidentally exposing sensitive information. Additionally, utilizing ad blockers can prevent fictitious ads from appearing altogether.
Ransomware Gangs Pose as Microsoft IT Support in Email Bombing Attacks
Multiple ransomware gangs have been identified conducting email bombing campaigns, wherein a threat actor spams emails to a targeted email account, to then pose as Microsoft Teams tech support offering to fix the email spamming issue. The attack begins with the threat actor bombarding a targeted system with thousands of emails in a very short amount of time, so much so that the emails become a hindrance to the victim. The threat actor would then make contact with the victim and conduct a Microsoft Teams call posing as Microsoft IT. During this process, the victim would grant the threat actor access to their computer, allowing the threat actor to download malware onto the compromised system. This attack Tactics, Techniques, and Procedures (TTP) has been observed consistently over the last year, with previous examples linked to the ransomware group Black Basta.
In the most recent attacks, some code has been identified as linked to the threat actor STAC5143. After being granted access to the targeted system by the victim, the threat actor delivered several malware payloads, including a Java archive file and a RPivot backdoor giving the threat actor a direct connection to the victims system. Some obfuscation techniques have also been observed in use to avoid initial detection.
This form of attack requires sophisticated social engineering skill wherein the threat actor can put up a convincing enough act to trick a victim into divulging sensitive data. In this campaign, the social engineering is occurring person to person, making it even more difficult to identify malicious intent before the attack is already underway. It also leaves less of a code trail through which the threat actor can be tracked. An indicator of compromise is a large volume of emails being received in a short time and interactions with individuals claiming to be from Microsoft IT unprompted. It is critical to confirm the credentials of any IT person that attempts to access a system externally. Contacting an IT department personally and directly is another way to derail email bombing attacks

Oh No Cleo! Malichus Implant Malware Analysis
This deep dive into the Cleo software vulnerability and its malware analysis is a must-read. Read the article below for a break down of the threat in a way that’s both technical and accessible, helping you stay ahead of emerging risks.
Trucking Experts Link Cybersecurity to Company Culture
With cyberthreats evolving rapidly, the trucking industry faces increasing risks that could disrupt supply chains and business operations. Read the article below and get insights on the key cybersecurity challenges for 2025 and essential strategies to help companies stay ahead of potential attacks.
Target Rich, Cyber Poor: Strengthening Our Nation's Critical Infrastructure Sectors
There's an urgent need to strengthen cybersecurity in critical infrastructure sectors that are highly targeted yet lack sufficient protection. Read the article below and see how CISA provides key insights and strategies to help organizations defend against escalating cyber threats.
Actively Exploited Fortinet Zero-Day Gives Attackers Super-Admin Privileges
Cybercriminals are actively exploiting a Fortinet zero-day vulnerability to gain super admin privileges, posing a serious threat to cloud security. Read the article below and learn more about the attack, its implications, and the urgent steps organizations must take to protect their systems.
Product Security Bad Practices
Using insecure products can put your organization at serious risk. Read the CISA report linked below and learn about the most dangerous product security bad practices to avoid. Understanding these pitfalls is essential for strengthening your cybersecurity posture and preventing costly breaches.
Chinese Innovations Spawn Wave of Toll Phishing Via SMS
A new wave of toll phishing scams via short message service (SMS), fueled by Chinese technological innovations, is tricking victims into unauthorized charges and data theft. Read the article linked below to learn these scams work and get crucial tips to protect yourself from falling victim.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!







.jpeg?width=600&height=400&name=012725-CyberWebinar-PracticalCyber-600x400%201%20(1).jpeg)

.jpg)
.png?width=900&height=600&name=CIR%20Images%20(11).png)




