December 2024
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover enterprise system and rolling asset security, trending reports, and more.
Just Released: Essential 2025 Insights for Trucking Leaders
The trucking industry is at a pivotal crossroads. As we move into 2025, new cybersecurity threats—from AI-enhanced phishing to cyber-enabled cargo theft—are reshaping the landscape. Download our comprehensive report and explore critical developments you need to understand to stay ahead.
Hidden Risks Inside U.S. Ports Revealed
From espionage to supply chain disruptions, Chinese technologies are posing serious threats to U.S. operations. Whether you’re an IT professional, supply chain manager, fleet executive, or risk manager, download the whitepaper now to understand how you can do your part in mitigating organization risk from potential widespread disruption.
Salt Typhoon's Espionage Campaign
New Blog
People's Public of China (PRC)-backed threat actor Salt Typhoon exploited wiretapping backdoors in U.S. telecom systems to access sensitive communications, including call logs, texts, and audio recordings, raising significant national security concerns.
While the trucking industry was not directly targeted, the attack underscores the importance of encrypted communications and robust cybersecurity measures to protect critical infrastructure.
Anyone responsible for cybersecurity in the trucking and supply chain sectors should read this blog to understand how advanced threats could impact operational integrity and national security.
Unlocking the Potential of AI in the Trucking Industry–Opportunities and Risks
New Blog
Are you a fleet manager, IT professional, or industry leader looking to leverage artificial intelligence (AI) effectively while navigating its complexities? Read this latest blog by NMFTA's Principal Cybersecurity Engineer, Ben Wilkens, who shares insights into balancing innovation with security and responsibility in your operations.
The Last-Minute Shopping Survival Guide
New Blog
Don’t let last-minute holiday shopping stress you out—this guide has everything you need to stay organized and stress-free! Learn how to stay safe online while snagging deals, including protecting your personal information and avoiding phishing scams. Click below and make your holiday shopping efficient and secure.
Two Months to Go! Join NMFTA at Manifest
Don’t miss NMFTA’s dynamic session exploring the biggest cybersecurity trends of the past decade and daring predictions for the future. Gain actionable insights on emerging threats, shifting regulations, and state-of-the-art technologies to help you stay ahead in the ever-evolving cybersecurity landscape.
Use our link below and save $200 on your registration.
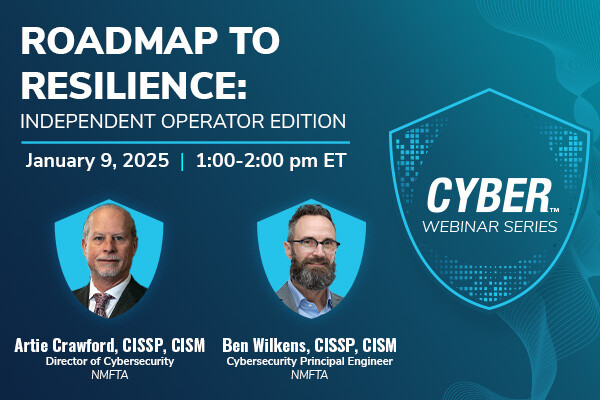
Cyber-Resilience Insights You Can't Miss
January 9, 2025 | 1:00-2:00 pm ET
Take steps now to protect yourself and your operation from cyberthreats. Join us for a discussion on the core cybersecurity best practices that an independent operator or small fleet can implement to significantly boost their cyber-resilience without breaking the bank.
ICYMI: NMFTA and Transport Topics Webinar on AI in Transportation
Watch on Demand
Rewatch the NMFTA Cybersecurity team and Transport Topics webinar that will explored the rapidly growing role of AI in the transportation industry. They examined both the significant benefits AI offers and the critical risks it poses, providing a balanced view of its potential impact.
ICYMI: Take a Look into the Trends of 2025
Watch on Demand
Rewatch the NMFTA Cybersecurity team discuss what's in store for 2025 and the trends impacting the supply chain cybersecurity. This panel discussion covered physical asset (vehicle and telematics) threats and enterprise cybersecurity threats in depth, as well as discussing the overall cybersecurity threat landscape.
In This Month's Report...
- Black Basta Ransomware Group Impersonates Microsoft IT Team to Breach Networks
- Fake Customer Support Centers Utilize Google Reviews to Steal Information
- Pygmy Goat Malware Utilized in Firewall Hack to Set Up Backdoor into Targeted System
- Threat Actors Utilize Exploit Identified in Array Networks Products
Black Basta Ransomware Group Impersonates Microsoft IT Team to Breach Networks
The ransomware group known as Black Basta has been observed targeting Microsoft Teams by impersonating IT specialists and contacting users to assist them with spam attack issues. Black Basta used a tactic it is well known for wherein the targeted companies saw their inboxes flooded with spam emails. None of the communications were outright malicious but, rather, were designed by Black Basta to overwhelm the targets with spam. The group would then utilize Microsoft Teams and pose as a Microsoft Help desk employee claiming to fix the spam issue. The Black Basta operative would then trick the target into installing an AnyDesk remote support tool thus giving the threat actor access to the target's computer. A Black Basta ransomware payload would then be directly delivered into the compromised system to steal data. In previous attacks, Black Basta would call the target instead of communicating via email, still posing as an IT specialist to aid the target in fixing the spam issue.
Active since April 2022, Black Basta appears to be financially motivated. The group has targeted a wide range of businesses and critical infrastructure in North America, Europe, and Australia. Black Basta frequently targets the healthcare and public health sectors, in particular, and has impacted hundreds of organizations worldwide. In a reference to its tactics, techniques, and procedures (TTPs), BlackBasta operates as a ransomware-as-a-service (RaaS) which enables the group to sell or rent predeveloped ransomware tools to its affiliates to execute ransomware attacks. Black Basta affiliates primarily use spear phishing to obtain initial access and utilize Remote Destkop Protocol (RDP) access for lateral movement in a system. BlackBasta uses RClone to exfiltrate data from a victim's servers then encrypts the data, executing a double extortion method commonly used by ransomware threat actors.
The identified attacks involve sophisticated and targeted social engineering campaigns in which Black Basta has experience in implementing, as the group’s favorite targeting method is spear phishing. Spear phishing is a specific and deliberate version of phishing attacks that are normally general and abstract. This campaign first overwhelms and frustrates the target with spam emails, thus making the victims more likely to engage with IT services and less likely to check credentials in favor of rectifying the issue quickly. So, Black Basta needs only to look official enough to pass as a Microsoft Help Desk representative in brief interactions. When granted access into the target system voluntarily, the group can implement malware behind any kind of firewall and bypass most other security measures. This approach also leaves a smaller cyber footprint making the threat actor harder to identify and making the malware harder to detect. This campaign exemplifies the creativity of threat actors, and reinforces the practice of confirming any correspondence and never disclosing personal credentials with a help desk that a user did not initiate contact with.


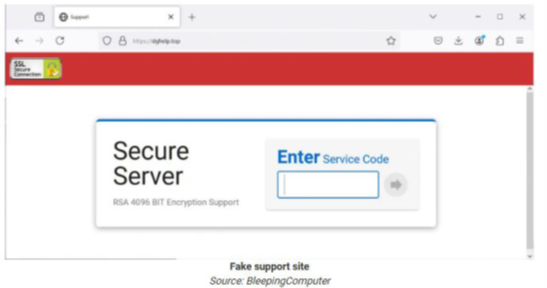
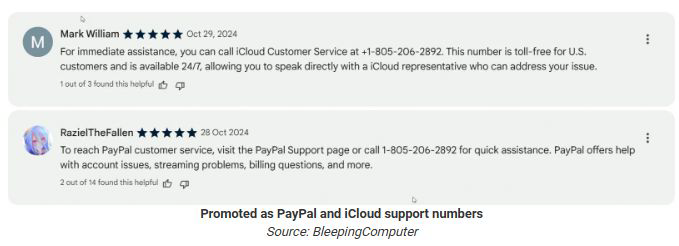
Fake Customer Support Centers Utilize Google Reviews to Steal Information
An unknown threat actor has been perpetrating an ongoing cyber and social engineering campaign that involves the use of Google reviews to trick victims into downloading remote access software. The scam begins through the threat actor writing a series of fraudulent reviews on a company’s website that include the phone number (805) 206-2892. The reviews are typically written for cybersecurity companies such as LastPass, which has been heavily affected by this campaign, because victims would likely be looking at reviews for a cybersecurity company and may be dealing with a cybersecurity issue. Upon calling the number, the scammer would pick up the phone and ask the victims a series of tech-related questions to build trust and convince the victim to download remote access software that gives the scammer access to the victim's computer and allows the scammer to steal data or deliver malware into the system.
While LastPass has been heavily affected, this campaign has also targeted other companies such as Amazon, Adobe, Facebook, Hulu, Verizon, PayPal, and iCloud. All of the scam reviews identified as part of this campaign have involved the same phone number, (805) 206-2892. Additionally, the reviews appeared not only on Google reviews but also on internal forums that allow users to write reviews directly on company sites, and on social media platforms. However, Google was the most commonly identified method for the scam. The fraudulent reviews have been continuously taken down but are replaced with more reviews daily.
This campaign utilized sophisticated social engineering techniques to trick victims into deliberately granting internal access to the unidentified scammer. The campaign utilized reviews on high traffic or highly specific companies and industries to increase the likelihood of interaction with victims, as the victims would be actively seeking specific aid or services. Once the number was disseminated, the scammer utilized exceptional interpersonal communication skills to trick victims into downloading malicious content. The campaign relies heavily on victim interaction and consent meaning the threat actor must be an expert in manipulation and may have some relevant experience in this process whether through legal or illegal means. No threat actor has been identified in relation to this scam. The investigation into the scam's origins is ongoing, as is the scam. The phone number (805) 206-2892 has been identified in all the reviews linked to this campaign, meaning users should avoid and report any reviews that include it. Analysts note that as knowledge of the scheme becomes more widespread, it is likely the scammer will introduce new phone numbers, so vigilance is advisable when interacting with any reviews that include contact information. Any links or phone number included in any online reviews should be viewed with skepticism.

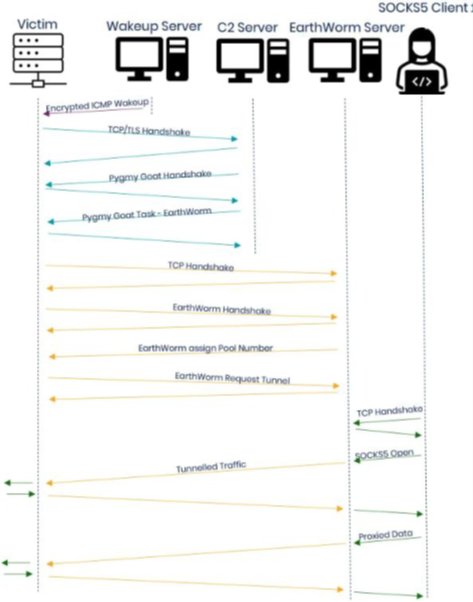
Pygmy Goat Malware Utilized in Firewall Hack to Set Up Backdoor into Targeted Systems
A malware known as Pygmy Goat has been observed in use creating a backdoor in Sophos XG firewall devices as part of a cyber campaign by Chinese threat actors. Pygmy Goat is an x86-32 executable and linkable format (ELF) shared object with the file name Libsophos.so. The malware utilizes the LD_PRELOAD environment variable to load its malware payloads into its target’s Secure Shell (SSH). This process allows the malware to deploy slowly and undetected by the target system. Once deployed, the malware establishes a backdoor that bypasses the Sophos firewall and establishes a connection to its command-and-control (C2) server. It communicates with the C2 via Transport Layer Security (TLS) to secure its communications and remain undetected. The malware includes capabilities that mimic Fortinet's certificate authority (CA) to further evade detection. Once established, malware payloads can be deployed directly into the infected device and data can be extracted from it through the backdoor.
The Pygmy Goat malware is known as a rootkit which is designed to infiltrate a system and control it while remaining undetected. This tactic is commonly used by Chinese state-backed threat actors. Pygmy Goat was designed to impersonate Sophos coding, using similar commands and thus becoming difficult for a system to identify. The malware targets network devices and includes persistence features and remote access capabilities making it a complex malware. Similar malware was identified in 2022 linked to the Chinese threat actor known as Tstark. While no threat actors have been definitively named as the perpetrator of this campaign, the TTPs utilized strongly suggest the threat actor is of Chinese origin.
Pygmy Goat is a sophisticated malware with capabilities that make it ideal for espionage purposes. Significant time was invested in developing the malware's evasion and obfuscation capabilities for the purpose of ensuring the malware can maintain persistence and exfiltrate data continuously. Its similarities to previous malware with confirmed links to the Chinese government indicate this campaign is likely part of China's growing cyber and corporate espionage sector. Monitoring for unauthorized encrypted file transfers accompanied with the Libsophos.so file can indicate Pygmy Goat’s presence in a system. Regularly checking internal systems and flagging suspicious behavior can also provide obstacles to Pygmy Goat’s operation.
Threat Actors Utilize Exploit Identified in Array Networks Products
Threat actors have attempted to take advantage of a remote code execution vulnerability present in Secure Sockets Layer (SSL) virtual private network (VPN) products by Array Networks. The vulnerability is tracked as CVE-2023-28461 and has a severity score of 9.8 out of 10. Identified in 2023, the exploit involves a bug that allows threat actors to browse through internal file systems or execute remote code on the SSL VPN while avoiding authentication. Effectively the threat actor can simulate hypertext transfer protocol (HTTP) and bypass security measures through the VPN itself. This bug was patched in March 2023, but is still being exploited today. The threat actor allegedly responsible for this latest round of exploitations related to CVE-2023-28461 is a group known as Earth Kasha. The group is a known China-linked state sponsored hacking group that may be
related to the APT10 hacking group. Earth Kasha was reportedly identified using the bug to set up backdoor access to affect systems.
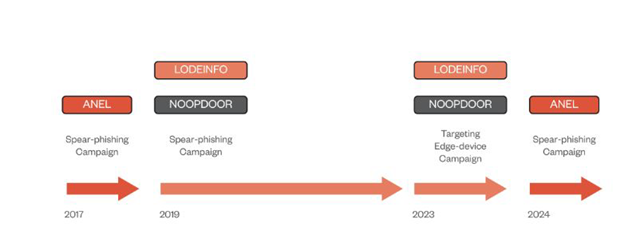
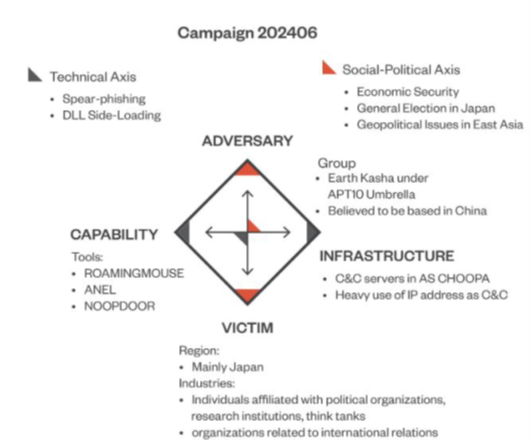
The exploit CVE-2023-28461 is over a year old, as is the patch to fix it. However, it is still being actively exploited. As a result of this latest round of attacks, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) reiterated the practice of updating systems whenever patches become available to prevent the exploitation of fixed issues. Earth Kasha is known to utilize various exploits and constantly change tactics as it probes for entry into systems. It is likely to continue attempting to use this exploit wherever possible. Its use of such an old exploit indicates its actively looking for ways to target the CVE-2023-28461 vulnerability.
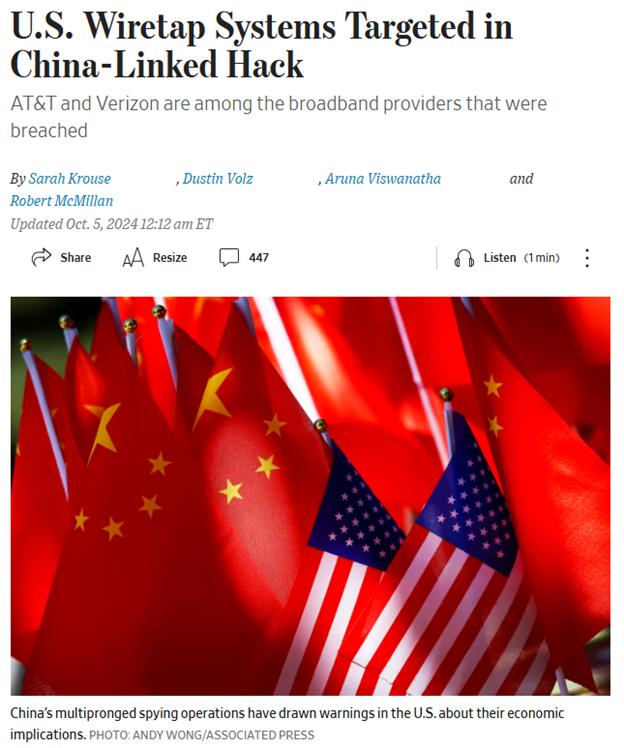
On November 13, 2024, the U.S. CISA issued a joint press release with the Federal Bureau of Investigations (FBI) regarding an investigation into the extent of previously reported Chinese intrusions into US telecommunications infrastructure. According to the release, the investigation uncovered a “broad and significant” campaign that Chinese state-sponsored threat actors had launched against multiple telecommunications companies in the United States with the goal of stealing “customer call records data” and compromising the communications of a select few individuals “who are primarily involved in government or political activity.” Also targeted in these data thefts were “law enforcement requests pursuant to court orders.”
This press release, which contained limited details regarding the findings or scope of the investigation, followed media reports published in early October 2024 about Chinese threat actors infiltrating AT&T, Verizon, and Lumen, among other telecommunications firms, to steal information relating to court-authorized wiretapping activities. In late October 2024, CISA and the FBI issued a separate joint statement announcing the start of its investigation into Chinese hacking of U.S. telecommunications infrastructure.
The main goal in this campaign was cyber espionage and data theft, common tactics that align with the Chinese government’s political and economic objectives. The scope and level of sophistication seen in these cyber attacks reiterate the ongoing threat that Chinese threat actors pose to critical infrastructure in the United States.
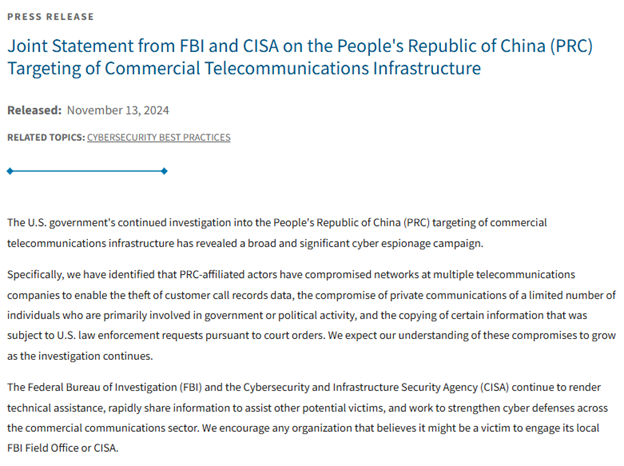
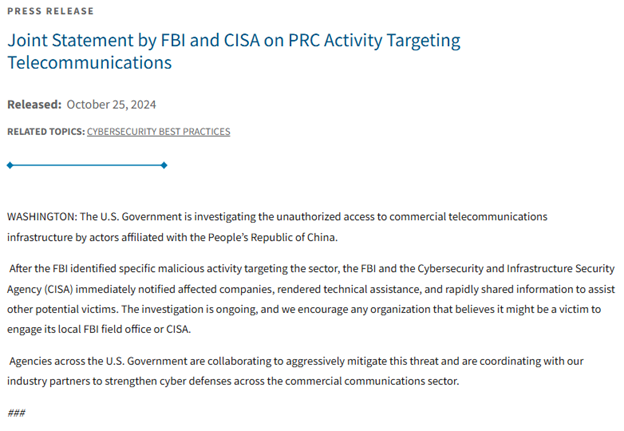
Joint Statement from FBI and CISA on the People's Republic of China Targeting of Commercial Telecommunications Infrastructure
Learn how the FBI and CISA are addressing cybersecurity threats from the People's Republic of China targeting U.S. commercial telecommunications in this critical joint statement.
Quantum Technologies in Transportation Report
Dive into the U.S. Department of Transportation's (DOT) Quantum Workshop Report to uncover cutting-edge insights and strategies shaping the future of quantum applications in transportation.
DOT Identifies Priority Areas, Near-Term Applications for Quantum
Discover how the U.S. DOT is prioritizing quantum technology to revolutionize transportation systems and address near-term challenges in the article below.
AI Red Teaming: Applying Software TEVV for AI Evaluations
Explore how CISA is leveraging AI red-teaming to enhance software testing, evaluation, validation, and security in this forward-thinking article.
Podcast: Cyber Threats and Solutions in the Supply Chain
NMFTA's Joe Ohr chatted with Logistics of Logistics' Joe Lynch last month about the critical role of cybersecurity in the supply chain, transportation, and logistics space. In our digital era, cyber threats like ransomware from organized, state-sponsored groups pose significant risks to global supply chains.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!







.jpg?width=600&height=400&name=600x400-email-v1%20(1).jpg)

