April 2025
NMFTA Cyber Intelligence Newsletter
The National Motor Freight Traffic Association, Inc. (NMFTA)™ has designed a monthly e-newsletter to bring cybersecurity awareness to trucking and supply chain professionals. Each month we cover enterprise system and rolling asset security, trending reports, and more.
Attention: Changes Coming to NMFTA Cyber Intelligence Newsletter
Roadmap to Resilience: Free Cybersecurity Resources for Trucking
Make cybersecurity a top priority with the Core Cybersecurity Controls Checklist from NMFTA. A practical, step-by-step guide to securing your business against cyberattacks.
Mid-sized fleets are prime targets for hackers, and a single attack could mean major downtime, lost revenue, and a serious headache. Our newly released Cybersecurity Best Practices Guidebook – Mid-Sized Fleet provide straightforward resources built specifically for mid-sized fleets.
Our Cybersecurity Best Practices Guidebook, packed with budget-friendly solutions, step-by-step tips, and real-world examples, is tailored specifically for small fleets and owner operators. Download the guidebook today and take control of your cybersecurity!
April 10, 2025 | 1:00 - 2:00 PM ET
Today, join NMFTA for an in-depth webinar where we explore the latest insights from our whitepaper, Not Your Average Ransomware: RaaS in the Transportation Industry.
May 8, 2025 | 1:00 - 2:00 PM ET
Next month, join the NMFTA cybersecurity team for the Securing the Future of Heavy Vehicle Cybersecurity—The CyberTruck Challenge webinar. This webinar will provide an overview of the mission of the CyberTruck Challenge and explain how it prepares students to tackle cybersecurity threats in heavy vehicles, and more.
Watch on Demand
NMFTA hosted the third installment in the Roadmap to Resilience series, targeted at mid-sized fleets (50–3,000 power units). This webinar provided more advanced guidance to incorporate technical controls and governance practices.
NMFTA and Cybersecurity Principal Engineer Wins 2025 Cybersecurity Excellence Award
NMFTA and its cybersecurity principal engineer, Ben Wilkens, have been honored with the 2025 Cybersecurity Excellence Award for their project, "Empowering Small Fleets with Cybersecurity Tools: NMFTA’s Game-Changing Guidebook." This recognition highlights NMFTA's commitment to enhancing cybersecurity within the trucking industry, offering valuable insights into their efforts to support small and mid-sized fleets in strengthening their digital defenses.
Save the Date for the NMFTA 2025 Cybersecurity Conference
October 26-28, 2025 | Austin, TX
We are six months away from the 2025 NMFTA Cybersecurity Conference. Make plans to join us on October 26-28, 2025, at the Westin Downtown Austin. Join our email list and be the first to hear when registration opens.
In This Month's Report...
Increase in Threat Actors Targeting Critical Infrastructure
Cybersecurity firm Dragos recently released their 2025 OT/ICS Cybersecurity Report detailing the increased collaboration between cybercriminal groups and nation states. More specifically, Operational Technology (OT) and Industrial Control Systems (ICS) are under threat from increased ransomware activity. Dragos highlights a 60% increase in groups targeting the OT/ICS environment due to ransomware adversaries leveraging remote tools and services due in part by geopolitics and state-sponsored hacktivism activity. More than 50% of the ransomware Dragos responded to in 2024 involved some element of a remote service attack, with all remote service attacks at minimum disrupting operations. While OT/ICS environments were one facet impacted, attacks on industrial organizations increased by 87% from 2023 – 2024. For example, more than 50% of all observed ransomware victims were in the manufacturing sector, representing 1,171 attacks. This was composed of a total of 80 identified groups, up 60% from 2023. Furthermore, Dragos identified nine active groups and two new OT cyberthreat groups, GRAPHITE and BAUXITE that share substantial technical overlaps with known nation state actors from both Iran and Russia.
According to Dragos: “A striking trend in 2024 was the continued lowering of the barrier to entry for adversaries targeting OT/ICS.” This is problematic because 70% of the vulnerabilities researched were deep within ICS networks. 39% of these could cause both a loss of view and a loss of control while 22% of advisories were network-exploitable and perimeter-facing. As mentioned, adversaries routinely exploited internet-facing applications such as Virtual Private Networks and Firewalls. These exploits allowed threat actors to gain initial intrusion into victim networks and move laterally through compromised systems, executing Stage 1 and Stage 2 kill chains of the ICS environment. Notable threat groups such as Volt Typhoon and Sandworm have extensively leveraged ICS environments for exploitation, directed towards the United States. This raises concern as there are many similarities between ICS and space architecture, creating a potential risk for similar tactics to be employed against space systems. For example, malware such as FrostyGoop are designed to manipulate Modbus TCP/502 communications within ICS environments.
The utilization of Modbus TCP in ICS attacks highlights a potential vector for adversaries to exploit vulnerabilities in space-based infrastructures, where similar protocols may affect us. Additionally, BAUXITE targeted Sophos firewalls and conducted port scanning on multiple OT/ICS assets. Sophos firewall exploitation can offer more efficient targeting of space system manufacturing sectors via supply chains for more disruptive and longer drawn-out attacks. Moreover, the convergence of cybercriminals and nation states equip both entities with more sophisticated toolkits as well as allowing for more aggressive attacks with reduced attribution.
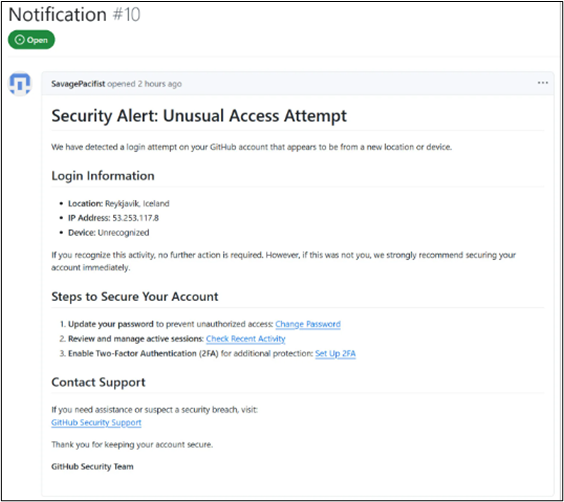
Fraudulent Security Alert Messages Used in Account Hijack Scheme on GitHub
Over 12,000 GitHub repositories have been targeted with a fraudulent security alert message involved in a new phishing campaign. The message links to the download of a malicious authorization app identified as OAuth. Upon download the app grants the hackers full control over the associated GitHub account and the code within the repository. The attacks included the same fraudulent security alert indicating an attempted login from Reykjavik Iceland and included the IP address 53.253.117.8. The information is designed to make the alert look more legitimate and trick the user into interacting with the provided links, which include the OAuth authenticator app.
The identified messaging utilizes sophisticated social engineering skills as the samples of the communications are detailed and convincing. The use of identical messaging indicates that the same threat actor is responsible for all identified attacks. The call back address links to onrender.com web page, further indicating a possible platform that the threat actor utilized to develop the OAuth app. The use of an authentication app to gain access to a system plays on the fear of a target victim after receiving the unauthorized access alert. This tactic increases the likelihood that a victim may interact with the link, as they may be preoccupied worrying about the fake alert. This is a common tactic utilized by experienced hackers that engage in social engineering campaigns. As of this writing, the responsible threat actor has not been identified.
SANS 2025 Threat Hunting Survey: Advancements in Threat Hunting Amid AI and Cloud Challenges
Learn how organizations are adapting their threat detection strategies to address the challenges posed by AI and cloud technologies from the SANS 2025 Threat Hunting Survey. This comprehensive analysis is an essential read for organizations aiming to enhance their defenses against increasingly sophisticated cyberthreats.
2025 OT Cybersecurity Report: 8th Annual Year in Review
Read the Dragos 2025 operational technology (OT) Cybersecurity Year in Review report for an in-depth analysis of the evolving threat landscape, including the identification of new threat groups like VOLTZITE, GANANITE, and LAURIONITE. This comprehensive overview provides critical insights into the tactics and targets of these adversaries, enabling organizations to enhance their defenses against emerging cyberthreats.
Cybersecurity for Smaller Trucking Fleets and Owner-Operators
Learn essential cybersecurity strategies tailored for owner-operators and small to mid-sized trucking fleets, focusing on practical measures such as regular software updates and system patches to mitigate cyber threats. Read the article below and find out why implementing these recommendations is vital for safeguarding sensitive data.
NMFTA Guides Cybersecurity Protocols for Mid-Size Fleets
NMFTA released the Roadmap to Resilience, a series of cybersecurity guidebooks specifically tailored for midsize fleets, offering practical strategies to safeguard operations against cyber threats. Read the article below and learn how you can enhance your organization's asset protection plan.
Auto-ISAC Releases Updated "Best Practices Guides" for Automotive Community
The Automotive Information Sharing and Analysis Center (Auto-ISAC) has released updated Best Practice Guides to assist automotive industry stakeholders in identifying and managing cybersecurity risks. These guides are essential for organizations aiming to enhance vehicle cybersecurity across key areas such as management and operations, awareness and training, governance, third-party risk management, and secure development lifecycle.
Nearly 24,000 IPs Behind Wave of Palo Alto Global Protect Scans
A new wave of scanning activity is targeting Palo Alto Networks' GlobalProtect portals, with nearly 24,000 unique IP addresses involved, raising serious concerns about potential exploitation. Read the article below and stay informed on emerging threats.
Refer a Colleague
Would you like others at your company to be added to the NMFTA Headline Newsletter email distribution list? Send them this link or fill out the form for them on their behalf below!











.png?width=2500&name=AutoISAC_logos_trans%20(1).png)

